CTB-Locker (Critoni) Ransomware Targets French Businesses With Relentless File Encryption
 Social engineering techniques have been a new front line of attack for hackers who are exploiting updated ransomware threats such as the CTB-Locker malware.
Social engineering techniques have been a new front line of attack for hackers who are exploiting updated ransomware threats such as the CTB-Locker malware.
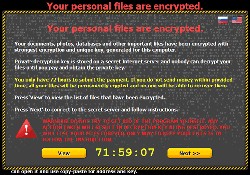
CTB-Locker Ransomware, also known as the Critoni Ransomware threat, has been an aggressive file encryption Trojan that destroys files on an infected computer. What CTB-Locker Ransomware is able to conduct is the actions of encrypting files and then displaying notifications exclaiming how a payment will grant a key to decrypt the affected files. In the latest variations of CTB-Locker or Critroni Ransomware, it is not allowing the encrypted files to be decrypted. Fundamentally, once files are encrypted by CTB-Locker, they are lost forever.
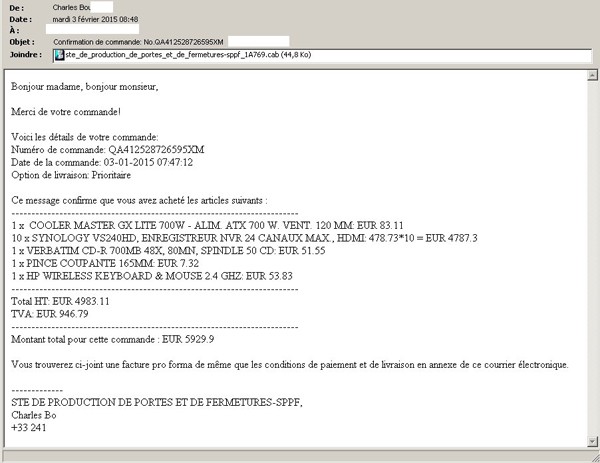
In the latest findings of the activities conducted by CTB-Locker Ransomware, it is being distributed through social engineering methods where it ends up being delivered to management departments at businesses located in France. The delivery takes place within a face invoice through a malicious email. The malicious emails, as demonstrated in figure 1 below, are formulated to look like they belong to co-workers to establish a level of trust. Opening up the email will reveal a nicely-crafted message and claims to be an electronic invoice for about $6,865. Opening the CAB file attachment, which is not a common file type that indicates malware, will initiate the malware where it will then add the Critoni or CTB-Locker Ransomware to the affected computer.
Figure 1. Malicious email distributing CTB-Locker (Critoni) Ransomware - Source: Bitdefender
After opening up the attachment and unleashing CTB-Locker, files will then be located for encryption. The latest versions of CTB-Locker have been found to offer an extended period of paying the fine, up to 96 hours. Moreover, the demands of CTB-Locker are updated to ask for 3 BTC, which equates to about $656. It is possible that the so-called extended time it now offers gives the ransomware threat more time to encrypt additional files including ones on connected storage devices.
Ransomware threats have long been a growing epidemic for PC users. New and sophisticated ransomware threats, such as CTB-Locker, have been on our radar screen for years as we discover their evolution and prominence as some of the post dangerous malware threats to grace computers in a long time. Being that CTB-Locker has been updated to be more aggressive and cause massive destruction, it is prudent that not only French computer users learn about how it attacks, but others around the globe should take heed to the recent warnings. Many businesses that CTB-Locker is attacking in France have backup systems in place. However, those that do not have backup countermeasures should beware of the wrath of CTB-Locker and its destructive nature. Such a threat could be a devastating blow to a company that relies on their data for day-to-day operations. Just think, one sweep from CTB-Locker Ransomware and your business could be facing bankruptcy or closed doors.
The takeaway from the latest version of CTB-Locker or Critoni Ransomware, is not the fact that it encrypts files but the idea of it not allowing those encrypted files to be recovered or decrypted. Basically, CTB-Locker destroys files that it encounters, which leaves the only solution being that you take proactive measures to back up your data and utilize the latest antispyware software available to help prevent dangerous ransomware infections such as CTB-Locker.