Malicious CryptoWall Ransomware Threat Updated to Version 2.0 with New Obfuscator
In the science of updating malware threats, hackers are mostly proactive in their abilities to update threats that have a serious effect on the systems that they infect. One threat that has caused massive issues for computer users is CryptoWall Ransomware due to its ability to encrypt files on an infected system.
CryptoWall ransomware has been a threat that was introduced to computer security experts many months ago where it was noticed to act much like other well-known encryption threats. CryptoWall ransomware's ability to encrypt files and then ask that a fee be paid for a decryption key is a well-thought-out attack on computer users. The crypto-malware that CryptoWall ransomware is has been mostly distributed through fake emails claiming to be a legitimate entity, such as in the cases of fake IRS emails.
Figure 1. - CryptoWall Ransomware Threat message in an updated version
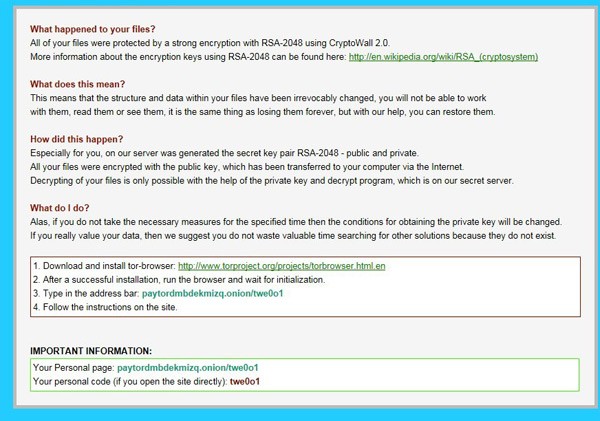
In recent discoveries of the CryptoWall ransomware threat, it was found to be updated to a new version, a modified threat that deploys new capabilities. The behavior of the updated CryptoWall ransomware, which is now dubbed as CryptoWall 2.0 and shown in Figure 1 above, has a new packer/obfuscator that can integrate a large number of methods designed to prevent debugging and analysis. This would be a way for CryptoWall 2.0 to evade methods that lead to the removal of CryptoWall or putting a stop to its encryption actions on an infected computer.
CryptoWall 2.0 was also found to utilize new command and control servers, which are designation points for the malware to contact for updated or new instructions to carry out on infected computers. Researchers from F-Secure, who have taken special notice to the updated CryptoWall threat, have found that it was signed with a digital certificate released just hours before its latest malvertising campaign started, a campaign that allowed it to spread through malicious advertisements. Many of those sites spreading CryptoWall were legitimate only the advertisements feed through the Zedo network were actually malicious and initially unaware to the webmasters.
Of the sites found to spread CryptoWall in an updated form where hindustantimes[dot]com, bollywoodhungama[dot]com, one[dot]co[dot]il, codingforums[dot]com, and mawdoo3[dot]com. It is a rather common action for hackers to feed malicious ads through a network due to having them signed with a new digital certificate, which is mostly undetected until someone notifies the ad network of the malvertising campaigns taking place.