Cryptojacking Malware Spreading to Government and University Websites to Mine Monero Cryptocurrency
 As time progresses, so do the actions of hackers who are now conducting the action of cryptojacking, which is a process of infecting a computer only to hijack its functions and CPU resources to mine cryptocurrency. As it turns out, the cryptojacking actions have made their way onto several government and University websites.
As time progresses, so do the actions of hackers who are now conducting the action of cryptojacking, which is a process of infecting a computer only to hijack its functions and CPU resources to mine cryptocurrency. As it turns out, the cryptojacking actions have made their way onto several government and University websites.
The cryptocurrency mining code that has made its way to hundreds of unsuspecting sites is known as Coinhive. So far, Coinhive has raked up as many as 400 sites to inject them with malicious JavaScript code that can then be used to infect visiting systems. Probably the most disconcerting aspect of the infected sites is that many of them include high profile sites, such as ones belonging to the San Diego Zoo, Lenovo, the National Labor Relations Board, and now, random government and University sites.
Cryptocurrency is all the new rave and cybercrooks are literally cashing in on their ability to leverage cryptocurrency by instructing infected computers to mine crypto. However, the methods for spreading malicious Coinhive code was once left on the launching pad. Moving to today, malicious cryptojacking threats are in abundance and growing by the day. The launch pad used for spreading cryptojacking threats are primarily infected websites, and cybercrooks are heavily targeting any vulnerable site they can find.
Cryptojacking Government and University Sites Reaches New Demographic for Hackers to Leverage
Having cryptojacking threats present on government and University sites hits a new demographic for computer users, which may leave many unsuspecting users as newfound victims. By finding a new demographic for the spread of cryptojacking threats, a cybercook could then speculate on gaining further traction for mining cryptocurrencies using robust systems, which are used within government offices and Universities.
The choice cryptocurrency that recent hackers are mining through infected computers is Monero. The unsuspecting code within Coinhive, which is the JavaScript program used in these attacks, isn't initially a malicious application. Computer users must understand that Coinhive is a legitimate platform for mining Monero cryptocurrency through a website. Unfortunately, cybercrooks are leveraging Coinhive to perform malicious actions in using infected PCs to mine cryptocurrencies, mostly without notifying a victimized computer user.
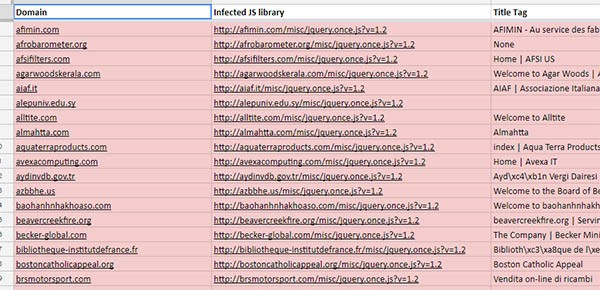
The recent cryptojacking campaign is using the same Coinhive code injection methods as those we have seen in the past. Among the nearly 400 websites attacked, there are some surprising findings within the full list, which can be found here. Thanks to research performed by Troy Mursch via BadPackets.net, a cryptojacking site list was compiled, which identifies many surprising government and University sites being infected with the malicious script code ready to infect visiting computers.
A Snippet of Cryptojacking Campaign-Attacked Sites discovered by Troy Mursch
Many of the sites found to be victims of malicious cryptojacking script injections are hosted on Amazon servers in the USA, which is a widely popular platform for professional hosting services. Mursch believes that many of the sites were compromised due to an outdated of Drupal, which allowed hackers to discover vulnerabilities that have not been patched and inject such sites with malicious Coinhive code. In knowing this information, it behooves webmasters to take heed to the warning and ensure that their webservers are properly updated and not susceptible to cryptojacking attacks.