North Korean Hackers Setup Fake Cybersecurity Firm to Target Security Experts
 A hacking group that is backed by the North Korean government is targeting cybersecurity researchers with malware as part of a new social engineering attack.
A hacking group that is backed by the North Korean government is targeting cybersecurity researchers with malware as part of a new social engineering attack.
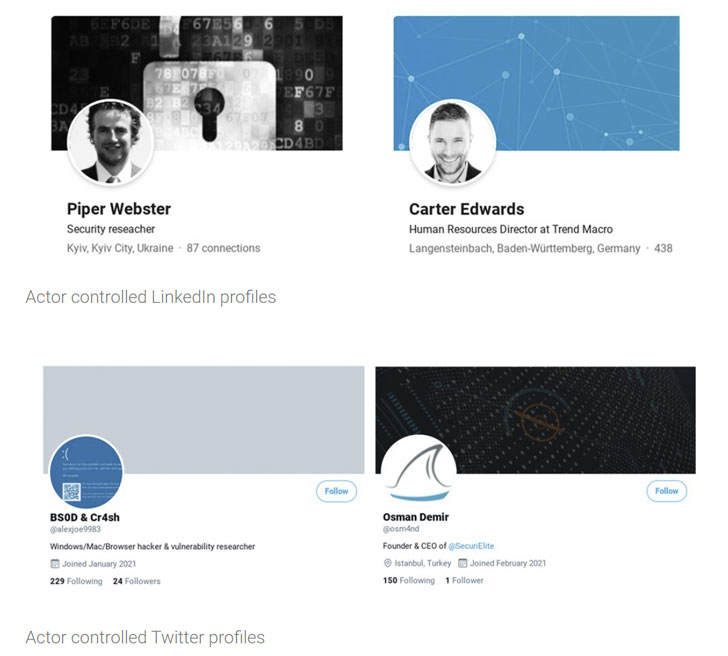
According to a late March report from Google's Threat Analysis Group, the hackers set up a phony security company called SecuriElite along with several social media accounts on Twitter and LinkedIn in an effort to fool researchers into visiting the company's website that was set up with a browser exploit.
TAG's Adam Weidemann said of the website that launched on March 17th, "The new website claims the company is an offensive security company located in Turkey that offers pentests, software security assessments and exploits,"
Eight Twitter profiles and seven LinkedIn profiles were created for so-called employees claiming to be vulnerability researchers and HR personnel at the fake security firms. All of the profiles have since been suspended.
Additionally, Google added the purported website's URL to its Safebrowsing blocklist service to prevent anyone else from accidentally visiting the site.
The actual motive behind the attacks is still a mystery, although some suspect that the NoKo hackers may have been attempting to get a hold of zero-day research in order to use those unpatched vulnerabilities to execute future attacks on additional targets.