'Hacking Team' Surveillance Software Provider for Government Agencies Hacked, 400GB of Data Leaked
 Hackers are on the move this year and are targeting government agencies by exposing an abundant amount of data harbored by a popular surveillance software provider.
Hackers are on the move this year and are targeting government agencies by exposing an abundant amount of data harbored by a popular surveillance software provider.
In what is claimed to be an exposure of over 400GB of data, hackers leaked information belonging to Hacking Team, a surveillance software provider for government agencies around the world.
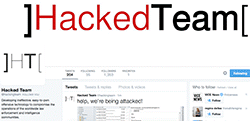
Hacking Team, an interesting name to call a legitimate company who is known for providing surveillance programs to several government agencies across the globe, is the brunt of an attack by hackers from many angles. One of the angles has proven to be the Hacking Team's Twitter account, which was defaced by cybercrooks, which are being used to expose the internal emails and correspondence with the company's customers. The Hacking Team Twitter logo and short bio have also been changed to read: "Hacked Team - Developing ineffective, easy-to-pwn offensive technology to compromise the operations of the worldwide law enforcement and intelligence communities."
Looking further into the company's Twitter account, there is a pinned tweet on the profile that says, "Since we have nothing to hide, we're publishing all our e-mails, files, and source code," followed up by links to actual torrent files. Use of the links provided within the tweet will redirect browsers directly to download the torrent files later initiating the download of the compromised data.
As far as the type of data compromised in the hacking incident, it is alleged that it exposes covert surveillance activity of many governments. With the data exposed amounting to nearly 400GB, the possibilities of there being some serious backlash and exposure of government secrets are highly likely. Hacking Team's business will receive a serious blow to their reputation, and the fallout of this incident has yet to be seen or even predicted for that matter.
Among the European countries alone whose government utilized the Hacking Team's services are the Czech Republic, Germany, Hungary, Luxembourg, Poland, Spain, Switzerland and many more. The list doesn't stop there; it also includes the United States of America, several Asian countries, Middle Eastern areas, and even African countries.
Deep into the secrets of how organizations like Hacker Team utilize and develop their surveillance software for government agencies, some of the developments are classified as malware. Such software is used to monitor the activity of subjects that prove to be of interest to some governments. You can think of it as a way to keep peace on the technical front of governments when it comes to cyber security infrastructures.
Security researchers are already on the case of this hacking incident and formulating tools that detect traces of malware known to he used by governmental organizations. In that, there may be a path to tracing the data exposed in the hacking case or eventually track down the perpetrators responsible for the attack.
The latest data to come out of the hacking incident has concluded that the Hacking Team practiced extremely careless password use practices. There is no doubt that the use of weak passwords helped contribute to the company's hacking demise.
Unfortunately, due to the data exposed consisting of every government client along with the time they first purchased services from Hacking Team, recuperating from the breach will take time and relentless efforts by Hacking Team. Moreover, the amount paid by each government entity for surveillance software is now known to whoever chooses to capture a fraction of the 400GB of data spilled onto the internet.