Gmail Phishing Scam Rapidly Spreading to Trick You Out of Your Google Account Login Credentials
 Let's face it; hackers have no mercy when it comes time that they exploit computer users through their naiveté or lack of enough knowledge to avoid becoming the next victim of data and identity theft. As it turns out, hackers are actively peddling a quite massive and aggressive phishing campaign that is seeking the login credentials to Gmail accounts.
Let's face it; hackers have no mercy when it comes time that they exploit computer users through their naiveté or lack of enough knowledge to avoid becoming the next victim of data and identity theft. As it turns out, hackers are actively peddling a quite massive and aggressive phishing campaign that is seeking the login credentials to Gmail accounts.
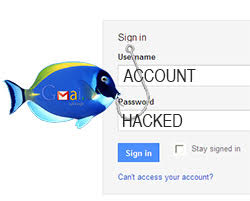
Hackers behind an enormous Gmail phishing campaign have employed sophisticated automation feature code onto websites that look to mimic a Gmail login page. The phishing technique used is one that is actively tricking Internet users into unknowingly give hackers access to their Gmail accounts.
The act of Phishing, which is known as a process where a website or web page is created to closely resemble a legitimate site, dates nearly as far back as the age of the Internet. In common phishing schemes, a legitimate site is either compromised or mimicked on another page to fool computer users. The technique of phishing ends up making computer users believe that they have landed on a legitimate page where they are required to enter their login credentials to access their account.
In the case of the recent Gmail phishing attack, a page resembling the login site for Gmail is used to collect the login username and password to computer user's Gmail account, which then gives a hacker unadulterated access to a Google account. As you may know, a Google account may consist of a lot of information, not just the emails in a user's Gmail Inbox. We're talking about having access to a user's calendar, Google Play store access, personal photos, and even files stored on one's Google Drive.
Gmail users are being tricked left and right with the new phishing scheme. It all starts with users receiving a spam message, one that contains seemingly innocent information but is enough to draw the curiosity of some computer users to open the message. The spam message includes an attachment that masquerades as a PDF file, which is also perceived by unsuspecting users as a harmless file. When a computer user clicks on the PDF file, it then executes sophisticated malware that will redirect a user's web browser to a fake Google login page with the pretense that logging in will grant access to open the image attachment.
As you can guess, entering login credentials in the fake Google login page will then send the username and password to hackers where they can later use it to access user's Google accounts.
One of the more surprising aspects of the recent Google and Gmail phishing attack is the phishing pages do not appear to set off Google's HTTPS security warning. The Google HTTPS security warning is designed to alert users when they land on an unsafe web page or one that has been identified in the past as being malicious.
Not only have hackers upped the ante on their phishing techniques, but the recent Gmail phishing attack is said by many computer security researchers to be among the most sophisticated of its type. To add insult to injury, the attack is spreading rapidly by scouring sent messages within the "sent mail" folder of victimized Gmail users only to send the malicious email to any contacts that it discovers on the account. By sending messages to known contacts, the recipient will naturally trust the sender and be more inclined to open the malicious attachment, which so far is tricking many savvy users.
Google is aware of the phishing attack and is further investigating the matter. As an initial response to the phishing attack, a Google spokesperson said, "We help protect users from phishing attacks in a variety of ways, including: machine learning based detection of phishing messages, Safe Browsing warnings that notify users of dangerous links in emails and browsers, preventing suspicious account sign-ins, and more. Users can also activate two-step verification for additional account protection."