Fireball Is the Biggest Adware Campaign the World Has Ever Seen, Researchers Say
 'Adware is malware with a legal team,' infosec guru and avid Twitter user SwiftOnSecurity once said. The coming days should be pretty busy for the legal team of Rafotech, a Chinese digital marketing company and app developer. That's because according to Check Point, Rafotech is responsible for Fireball, a browser hijacker that has affected a quarter of a billion computers across the globe.
'Adware is malware with a legal team,' infosec guru and avid Twitter user SwiftOnSecurity once said. The coming days should be pretty busy for the legal team of Rafotech, a Chinese digital marketing company and app developer. That's because according to Check Point, Rafotech is responsible for Fireball, a browser hijacker that has affected a quarter of a billion computers across the globe.
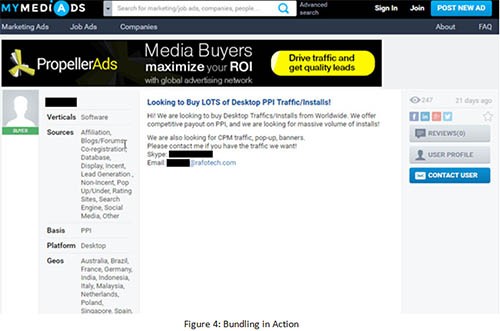
The researchers say that Fireball uses the most common adware distribution method – bundling. Bundling means pushing unwanted programs alongside legitimate (in most cases free) ones and preying on users' assumption that installing software involves clicking the Next button several times. Check Point's experts said in their blog post that Fireball has been bundled both with Rafotech's own products, the Mustang Browser and Deal Wifi, and with Soso Desktop and FVP Imageviewer, software developed by other vendors. The researchers also posted a screenshot which shows how a person using an @rafotech.com email wants to buy installs worldwide.
Screenshot using @rafotech.com email to purchase adware traffic
Whether any money has been paid for aggressively pushing unwanted software on computer users is unknown, and it must be said that Check Point's estimated number of affected systems is entirely based on their own research. The search engines researchers link to Rafotech have attracted quite a lot of traffic, though.
The Indicators of Compromise section of Check Point's blog post contains some decidedly shady domains like hohosearch[dot]com and trotux[dot]com, and if Alexa is anything to go by, these websites are visited by a substantial number of users every day. Most of the visitors are located in India and Brazil which is also in line with Check Point's research.
This is what Fireball is all about at the moment. Its purpose is to modify the home pages, install browser extensions, and redirect traffic to Rafotech's search engines, with the idea of boosting the marketing agency's ad revenue. The search engines also contain tracking pixels which give Fireball's developers a bit more information on the people whose traffic has been hijacked.
It's not the most dangerous thing you can find on your computer, it must be said. Despite this, Check Point's researchers are extremely concerned. And if everything they're saying is true, they should be.
Since the whole operation revolves around ad revenue, classifying Fireball as anything more than adware could be considered unfair. The experts do say, however, that Fireball can execute code on the host computer and that it can easily be converted from a humble browser hijacker into a powerful information stealer or malware dropper. This is especially worrisome because many of the affected systems aren't home computers.
In fact, Check Point reckon that Fireball can be found on 20% of all the corporate networks in the world. What the researchers are saying is that one in five business organizations can easily fall victim to a serious data breach.
It all sounds rather gloomy, and it will be interesting to see what Rafotech has to say for itself. As of the time of writing, the Chinese company hasn't issued a statement. Home users and system administrators shouldn't wait for a response, though. What they should do instead is make sure that there are no browser hijackers on their machines.
Fortunately, determining whether this is the case is fairly easy. All you need to do is make sure that your homepage hasn't been touched, that all the browser extensions have been installed manually by you, and that there is no suspicious software in the Add/Remove Programs list in the Control Panel. Mac OS users aren't safe, either. They also need to ensure that their browsers are unmodified and they might want to look for unknown files in the Applications folder.