Bamital Botnet $1 Million/Year Cybercrime Ring Dismantled by Microsoft and Symantec
 The daunting task of security experts and researchers to combat malware and cybercrooks has paid off in a great way as software giants Microsoft and Symantec dismantle a cybercime ring responsible for controlling hundreds of thousands of compromised PCs without the knowledge of their users.
The daunting task of security experts and researchers to combat malware and cybercrooks has paid off in a great way as software giants Microsoft and Symantec dismantle a cybercime ring responsible for controlling hundreds of thousands of compromised PCs without the knowledge of their users.
What is known as the Bamital Botnet or Bamital, a Trojan infection affecting a vast group of compromised computers reaching numbers in the hundreds of thousands, was disrupted when technicians working on behalf of Microsoft Corp and Symantec shut down servers that controlled these compromised systems.
Data centers located in Weehawken, New Jersey and Manassas, Virginia was raided by technicians from Microsoft and Symantec with the assistance of U.S. Federal Marshals under an order issued by the U.S. District Court in Alexandria, Virginia. During the raid, the control of one server at the NJ facility was seized and then persuaded the operators of the Virginia data center to shut down a server at their parent company located in the Netherlands. Richard Boscovich, Microsoft's Digital Crimes Unit assistant general counsel, explained to sources that they had "a high degree of confidence" that the operation was successful in ceasing the cybercrime operations and Bamital botnet.
Botnets are known to be a major source for spreading malware, hacking systems and carrying out malicious actions without detection on the Internet. With most botnets being a group of many compromised computers under the control of a command and control server, the potential destruction they can cause is virtually endless.
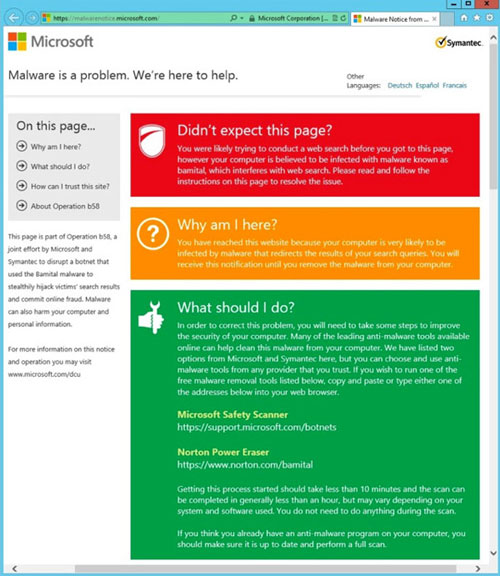
Bamital botnet was believed to be responsible for compromising what Microsoft and Symantec estimate between 300,000 and 1 million PCs, all infected with malicious software confined to the botnet. Now with such a large number of computers no longer able to receive commands from the server that was shut down, these systems will be directed to a site informing the users that their computer was infected with malware when the attempt to search the web. Through this ordeal, Microsoft and Symantec are offering free resources to the effected computer users to restore access to web searches. The message pushed out to the users, as shown in Figure 1 below, will read: "You have reached this website because your computer is very likely to be infected by malware that redirects the results of your search queries. You will receive this notification until you remove the malware from your computer."
Figure 1. Example of Microsoft message alerting PC users of Bamital
Investigative forces have not always been as lucky as Microsoft and Symantec in making such a bountiful discovery of a massive botnet. In the past, crime units of security companies and various law enforcement agencies around the world would make a break in their cases every blue moon but would only be successful effecting up to tens-of-thousands of compromised systems within a botnet. The Bamital botnet ring is by far one of the larger group of compromised systems that have met its demise at the hand of a crime unit.
Microsoft has been a strong force in obtaining court orders to disrupt botnets. The disruption of Bamital would make it the 6th time Microsoft has attained such orders since 2010. That may seem like a small number but in retrospect, taking down a botnet server responsible for controlling up to a million compromised systems is no small feat.
Monetarily Microsoft and Symantec estimate that Bamital was responsible for attaining at least $1 million in profits in a given year for the organizers of the operation. Speaking of the operators of Bamital, 18 'John Doe' assailants scattered from the United States, Australia, Russia, Romania and Britain, were found to have dealings in this matter registering websites and operating under fictitious names.
Bamital was not your ordinary botnet either. It redirected search results from just about every large internet search engine. Through devious link baiting and search results poisoning methods, Bamital authors were able to force infected computers to generate massive amounts of automated ad clicks granting the creators a handsome payday.
Bamital may turn out to be rather reminiscent of the DNS Changer Trojan, which was where after servers were taken down people were still told to go to a site to check if they were infected with the DNS Changer threat. Due to the vast outreach of Bamital, it could end up causing precautions even though the command and control server has met its demise. Basically, there are still upwards of a million infected computers out there that could render malicious actions without the guidance of its ring-leaders. Microsoft and Symantec uncovered infected systems having a cookie placed on the system written in Russian. This could be conclusive evidence of the origin of some of the 18 alleged hackers.
Microsoft, since the shutdown of Bamital, has provided specific details of the takedown and operation on its blog linked here. The efforts of Microsoft and Symantec will go noticed by many and we may even see a slight decline in fraudulent activity on the Internet for a short period of time. Hopefully, other security and crime units can synergize their efforts to combat cyber gangs, just as Microsoft and Symantec have done to make life easier for all of us in our cyber-crazed world.