Android.Bankosy Trojan Steals Two-Factor Logins from Android Smartphones
 We all want to believe that the connection from our smartphone to the internet is secure. After all, there's nothing like finding out a hacker was able to access your banking account to steal money all due to your smartphone relinquishing personal information without your knowledge.
We all want to believe that the connection from our smartphone to the internet is secure. After all, there's nothing like finding out a hacker was able to access your banking account to steal money all due to your smartphone relinquishing personal information without your knowledge.
In the latest security hole within the open Android smartphone operating system, an information-stealing Trojan identified as Android.Bankosy is capable of stealing login credentials even through a popular two-factor authentication method. Two-factor authentication (2FA) has been around for many years and is known to be an added layer of security used by large companies like Google, Facebook, Twitter, and Microsoft on top of normal password logins. In most cases, 2FA is used to verify the identity of someone attempting to log into an online account and may send either an SMS message to your smartphone or initiate a voice call to deliver a code that you must enter to log into an account.
The recently-evolved threat Android.Bankosy has now adapted the ability to intercept those 2FA codes sent either through SMS message or voice calls. The author of Android.Bankosy has evoked rather clever methodology and coding into the malware threat that targets users primarily in the Asia-Pacific region of the world. The Android devices infected with Android.Bankosy initially received an update to the malware enabling it to perform the newfound functions of stealing 2FA verification codes and login credentials.
Obtaining a 2FA code through SMS message is a rather easy feat. However, doing the same with voice calls is where the updates to Android.Bankosy comes into play as it is now able to temporarily forward any voice calls from the victim to the attacker's phone number. Setting up the call forwarding method is as easy as entering and calling dialing "*21" and then the destination phone number, which the Android.Bankosy threat is doing on infected devices.
Once a 2FA code is obtained by the Android.Bankosy threat, it is then sent through a voice call and rerouted to the attacker's phone. From there, the attacker may instruct a Command and Control (C&C) server to deliver instructions to the infected smartphone and disable call forwarding by dialing the digits "#21#".
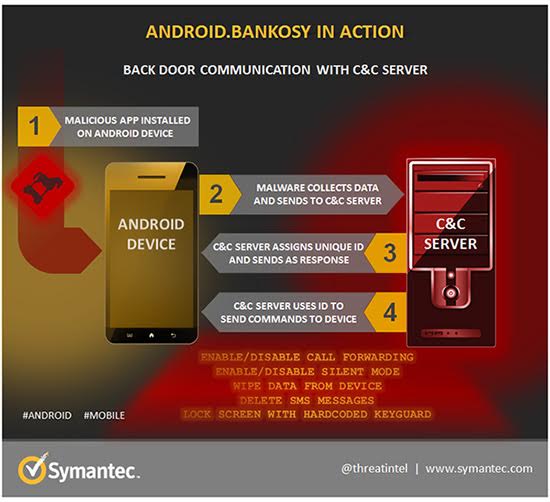
The dubious actions of Android.Bankosy are relatively new to the scheme of attacking smartphones. However, there have been many instances of similar malware and Trojan horse threats compromising smartphones running the Android OS and later instructing them to carry out other actions, including the recording of logins and passwords. This is the first time we have seen a case where 2FA is exploited in such a manner. The chart below is step-by-step communication activity initiated by Android.Bankosy.
Android.Bankosy communication in action Chart – Source: Symantec.com
What is also discerning about the Android.Bankosy threat is that it may be instructed to perform other functions while residing on an Android smartphone. Among those actions, Android.Bankosy may be told by a C&C to lock the phone, silence its audio and of course, forward phone calls. Not only would attackers armed with Android.Bankosy be able to compromise a 2FA code, but they may also eavesdrop on conversations potentially spilling other personal information without notification to the victim.