Trojan.Ransom.Gen
The Trojan.Ransom.Gen Trojan is the malware infection responsible for many ransomware variants such as the infamous Ukash Virus family as well as North American ransomware infections, such as the FBI Moneypack ransomware threat. Trojan.Ransom.Gen is distributed via malicious email attachments and social engineering attacks targeting inexperienced computer users. Once Trojan.Ransom.Gen infiltrates a computer, Trojan.Ransom.Gen installs a ransomware threat that blocks access to the targeted computer as a way of forcing the victim to pay a large amount of money. If you cannot gain access to your computer due to the presence of an obtrusive, full screen message claiming to belong to law enforcement, ESG security researchers strongly advise using a reliable and fully updated anti-malware application to remove Trojan.Ransom.Gen and its associated malware from your computer permanently.
The basic principle behind most ransomware infections is taking the victim's computer hostage in order to demand a ransom from the computer user. Trojan.Ransom.Gen is not exception; this malware infection prevents the PC user from gaining access to the infected machine. To do this, Trojan.Ransom.Gen creates a fake message from a law enforcement agency. This message varies depending on the victim's computer's IP address. The IP address can be use to determine a computer's geographical location. Using this information, Trojan.Ransom.Gen displays a message in the targeted victim's language and supposedly being sent by the law enforcement agency belonging to the victim's country (for example, victims in the United States receive a message from the FBI while victims in the United Kingdom receive a message from the Metropolitan Police or from Scotland Yard). This message will typically allege that the targeted computer was associated with illegal activities, such as copyright infringement or viewing forbidden pornographic material. It will usually threaten the victim with jail time unless a fine is paid using the Ukash or Moneypak money transfer services.
Since Trojan.Ransom.Gen blocks access to the infected computer, it may be difficult to remove this threat without being able to access anti-malware software on the infected machine. Fortunately, Windows allows computer users to bypass Trojan.Ransom.Gen by using Safe Mode to start up the infected computer. This can also be done by starting up the infected computer from an external memory device, such as a CD or a shared drive.
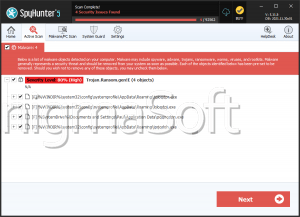
File System Details
| # | File Name |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|
| 1. | C:\WINDOWS\System32\DLA\DLACTRLW.EXE | |
| 2. | C:\PROGRA~1\EPSONS~1\EVENTM~1\EEventManager.exe | |
| 3. | C:\WINDOWS\system32\spoolsv.exe | |
| 4. | C:\Program Files\USB TV\EM28XX\BDARemote.exe | |
| 5. | C:\Program Files\Common Files\Logishrd\KHAL2\KHALMNPR.EXE | |
| 6. | C:\Program Files\Adobe\Acrobat 10.0\Acrobat\Acrotray.exe | |
| 7. | C:\WINDOWS\system32\ctfmon.exe | |
| 8. | C:\Program Files\Internet Explorer\iexplore.exe | |
| 9. | C:\Program Files\Bonjour\mDNSResponder.exe | |
| 10. | C:\Program Files\Java\jre6\bin\jqs.exe | |
| 11. | C:\WINDOWS\system32\wscntfy.exe | |
| 12. | C:\Program Files\Dell\Media Experience\DMXLauncher.exe | |
| 13. | C:\Program Files\Common Files\LogiShrd\LComMgr\LVComSX.exe | |
| 14. | C:\WINDOWS\system32\Ati2evxx.exe | |
| 15. | C:\WINDOWS\stsystra.exe | |
| 16. | C:\Program Files\ATI Technologies\ATI.ACE\Core-Static\MOM.exe | |
| 17. | C:\Program Files\Microsoft Small Business\Business Contact Manager\BcmSqlStartupSvc.exe | |
| 18. | C:\Program Files\Hp\HP Software Update\HPWuSchd2.exe | |
| 19. | C:\WINDOWS\system32\RUNDLL32.EXE | |
| 20. | C:\WINDOWS\system32\wbem\wmiprvse.exe | |
| 21. | C:\Program Files\Intel\Intel Matrix Storage Manager\Iaantmon.exe | |
| 22. | c:\Program Files\Microsoft SQL Server\90\Shared\sqlwriter.exe | |
| 23. | C:\Program Files\Intel\Intel Matrix Storage Manager\Iaanotif.exe | |
| 24. | C:\Program Files\Common Files\LogiShrd\LComMgr\Communications_Helper.exe | |
| 25. | C:\Program Files\ScanSoft\PaperPort\pptd40nt.exe | |
| 26. | C:\WINDOWS\Explorer.EXE | |
| 27. | C:\Program Files\Logitech\SetPoint\SetPoint.exe | |
| 28. | C:\Program Files\ATI Technologies\ATI.ACE\Core-Static\ccc.exe | |
| 29. | C:\Program Files\Common Files\Java\Java Update\jusched.exe | |
| 30. | C:\Program Files\Common Files\InstallShield\UpdateService\ISUSPM.exe | |
| 31. | C:\WINDOWS\system32\cidaemon.exe | |
| 32. | C:\WINDOWS\system32\cisvc.exe | |
| 33. | c:\Program Files\Microsoft SQL Server\90\Shared\sqlbrowser.exe | |
| 34. | C:\WINDOWS\system32\svchost.exe -k NetworkService | |
| 35. | C:\WINDOWS\system32\svchost.exe -k WudfServiceGroup | |
| 36. | C:\WINDOWS\system32\svchost.exe -k imgsvc | |
| 37. | C:\WINDOWS\System32\svchost.exe -k netsvcs | |
| 38. | C:\WINDOWS\system32\svchost.exe -k LocalService |