How to Stop UltraModel Adware/Malware Targeting Mac OS Users
 UltraModel is a piece of adware specifically targeted against MacOS machines. Designed as a macOS application with an accompanying browser extension, it promises to provide an enhanced web search experience on Safari, Firefox, or Google Chrome. Alas, this is not the case. Instead of making your web surfing life easier, UltraModel will bombard you with intrusive ads in various forms — pop-ups, redirects, web surveys, banners/coupons, etc. — with the sole purpose of generating pay-per-click advertising revenue to its developers. Advertisements presented this way may often pose security risks including, but not limited to:
UltraModel is a piece of adware specifically targeted against MacOS machines. Designed as a macOS application with an accompanying browser extension, it promises to provide an enhanced web search experience on Safari, Firefox, or Google Chrome. Alas, this is not the case. Instead of making your web surfing life easier, UltraModel will bombard you with intrusive ads in various forms — pop-ups, redirects, web surveys, banners/coupons, etc. — with the sole purpose of generating pay-per-click advertising revenue to its developers. Advertisements presented this way may often pose security risks including, but not limited to:
- redirecting to malware-laden websites – online games, dating platforms, rogue antivirus software, etc
- executing a malicious script
- downloading additional malware capable of doing all sorts of further damage.
Also, the UltraModel adware may hijack your browser, modifying your homepage and search engine, and even plant a keylogger to gather sensitive browsing data along the way. In the worst-case scenario, the app may end up stealing your identity or get another piece of malware to do so.
Why You May Not Remember Ever Installing UltraModel
Most users won’t know they have this potentially unwanted application (PUA) running on their Macs until they have experienced a slowdown in their system’s performance and felt the annoyance of unremitting web ads. Ultra-Model-associated ads are easy to recognize by their underlying text that says, "Powered by UltraModel," "Ads by UltraModel," "Brought to you by UltraModel," as well as any other variation containing the UltraModel label.
The vast majority of PUAs usually come with more popular programs in software bundles. Unless you keep a watchful eye on every installation step, you will allow the UltraModel app to join your /Applications folder. Once in, UltraModel will gain permission to read the contents of every webpage you visit (see screenshot #1 below).
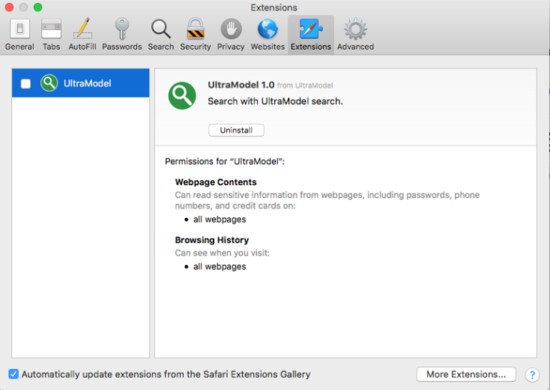
Screenshot #1 UltraModel Permission Source: VirusTotal
Alternatively, you may also come across the app by clicking on a banner advertising it as a helpful tool.
Now Let’s Remove UltraModel From Your Mac PC
You need to use a two-pronged approach to remove UltraModel from your Mac. The PUA has two components — the application itself and a browser extension — both featured in an archive called UltraModel.app.zip. To get rid of the extension, you must remove the app first (see screenshot #2 below).
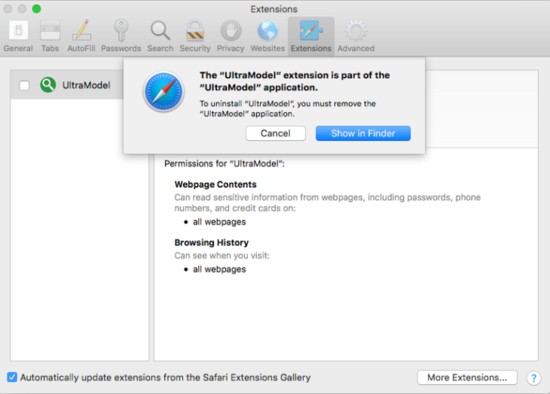
Screenshot #2 UltraModel Components Source: VirusTotal
Step 1: Uninstall the UltraModel App
To uninstall UltraModel, you need to remove it from your /Applications folder. To do so, you need to:
- Open the Finder tool to select Applications from the menu on the left to generate a grid view of all your apps.
- Delete UltraModel by right-clicking on the app and select Move to Trash. If you can’t find the app on the list, it may have hidden itself behind a different name. If so, take a look at the gird and move any unfamiliar apps to the trash, as well.
- If there is an UltraModel widget on the menu bar, close it.
- Empty your Trash folder by right-clicking your bucket-like trash icon from the Menu bar, and pick the Empty Trash option.
- Select Go > Go to Folder and look for residual UltraModel files in the following directories:
/Users/Shared
/Library/LaunchAgents
/Library/Application Support
/Library/LaunchDaemons
Step 2: Remove the UltraModel Extension from Safari/Firefox/Chrome
The procedure involves three main steps, namely:
- opening the browser menu to reach the list of Extensions
- removing UltraModel, as well as any other suspicious extensions from that list
- resetting the browser to its factory settings.
Contingent upon which browser you use, you will find your Extensions under the Add-ons menu (in Firefox), Tools (Chrome), or Preferences (Safari). Once you have deleted the unwanted extension(s), don't forget to reset your browser to its factory settings.