Gumblar Trojan Resurfaces and Exploits Adobe Reader and Acrobat Vulnerabilities
Security researchers are witnessing a reemergence of Gumblar, a piece of malicious code that is spread through unsecure or compromised legitimate web sites.
Gumblar was found on thousands of legitimate websites that here hacked into back in May of this year. The compromised websites were injected with malicious code to display an iframe which allows an attacker to bring content from one website to another. The iframe would lead unsuspecting computer users to the gumblar(dot)cn (read more on gumblar(dot)cn) domain where the system could be exploited through software vulnerabilities within Adobe Systems applications.
Over time, since May of this year, Gumblar has changed its methods of spreading on the Internet. Gumblar has been updated to put the malicious code directly onto a compromised website instead of hosting the payload on a remote server. This allows the hackers behind Gumblar to slip through the cracks in the event of the malicious hosting domain being shut down by an ISP.
The creators behind Gumblar have also went as far as to inject malicious iframe into forums which initiates a drive-by attack, exposing users to malicious content the instant that they visit a legitimate site that was compromised. After a computer is infected, Gumblar is able to look for the FTP credentials which the hackers uses to compromise other web sites.
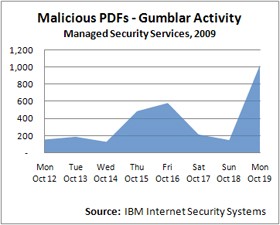
Figure 1. Malicious PDFs Gumblar Activity Chart
At one time, Gumblar was believed to be one of the biggest threats on the Internet because of its ability to spread through infected web sites and steal FTP credentials from an infected system. Researchers at IBM believe that Gumblar attacks may be connected with pay-per-click fraud because it is able to hijack the Internet Explorer web browser program and replace Google search results with those of compromised web sites. The "Malicious PDFs - Gumblar Activity" chart shown in Figure 1, demonstrates an increase of recent attacks that IBM Internet Security Systems has seen in their global hits on malicious Adobe PDF files. The Gumblar surge was ironically noted after Adobe released an updated batch of security patches on versions of Adobe Reader and Acrobat 9.1.3 and earlier. The vulnerability is actively being exploited with malicious PDFs by cybercriminals.
We believe Gumblar may prove to be one of the most aggressive threats on the Internet. If you store FTP login credentials on your computer, then you must safeguard that information. If your system succumbs to a Gumblar attack, then you could put other computer users at risk that visit the website that you run. Users of Adobe Reader and Acrobat are recommended to upgrade to versions 9.2 for Adobe Reader and 9.2 for Acrobat.