Fake Youtube Extension Files: YXH-youtube_player.xpi and YXH-youtube_player.crx
While Mozilla Firefox and Google Chrome are widely regarded as browsers that are vastly more secure than the common Internet Explorer, criminals can still attack computer users using these two browsers. One of the most common types of attack takes advantage of the vast amount of options that computer users have for customizing these two browsers, attacking through malicious add-ons and plug-ins. YXH-youtube_player.xpi and YXH-youtube_player.crx are two malicious browser extensions that are specifically designed to attack computer users with these two particular browsers; YXH-youtube_player.xpi attacks computer users with the Mozilla Firefox Browser and YXH-youtube_player.crx attacks computers with the Google Chrome browser (demonstrated in Figure 1 & 2 below). According to ESG security researchers, YXH-youtube_player.xpi and YXH-youtube_player.crx spread through a Facebook social engineering attack. A dangerous malware campaign designed to infect inexperienced computer users relies on malicious links that lead to pop-up windows prompting the victim to download the YXH-youtube_player.xpi and YXH-youtube_player.crx extensions. This malware campaign can spread both through Facebook walls and shares as well as through sites that use integrated Facebook functionality through a comments box compatible with Facebook.
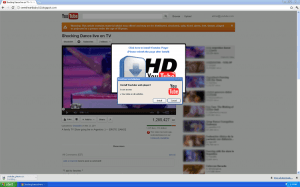
Figure 1. YXH YouTube Player Attack using Google Chrome Browser

Figure 2. YXH YouTube Player Attack with 'install YouTube Player' pop-up alert using Google Chrome Browser
How the YXH-youtube_player.xpi and YXH-youtube_player.crx Scam Works
The YXH-youtube_player.xpi and YXH-youtube_player.crx add-ons spread through social engineering. Basically, an infected user will display a link with a shortened URL supposedly linking to a popular YouTube video. When a user clicks on this fake link, a highly authentic copy of the YouTube web page shows up on the victim's browser. Conveniently, before the victim has a chance to visit the fake YouTube page, a pop-up window will appear (Figure 1 above). This is convenient because the fake YouTube page that appears is just for show not standing up to careful scrutiny. The pop-up window will prompt the victim to download a fake YouTube extension for watching videos in High Definition (Figure 2 above). This extension is installed like most legitimate browser extensions, and its download and installation begins automatically, before the victim can weigh their options or realize that YXH-youtube_player.xpi and YXH-youtube_player.crx are not legitimately connected to YouTube in any way. It is easy to be duped through this scam, considering that YouTube is a trusted website which when it comes to online security, has a really good track record. However, criminals are quite good at copying legitimate web pages in order to steal passwords or to perpetrate attacks such as this one. Once installed, the YXH-youtube_player.xpi and YXH-youtube_player.crx fake extensions initiate the download of a dangerous Trojan infection onto the victim's computer system. The Trojan infection responsible for these actions has been traced to JS/TrojanClicker.Agent.NDA, a Trojan known for promoting certain websites and initiate denial of service attacks.
This attack has become a common method of infection for a number of PCs, which proves to be a prudent time that all computers should take necessary actions to protect themselves with a useful anti-spyware program.