Cybercrooks Hack Hosting Providers to Conduct Massive Phishing Attacks
 The global phishing survey for the second half of 2012 was recently released by the Anti-Phishing Working Group (APWG) revealing how cybercriminals were able to break into the systems of hosting providers leading to massive phishing attacks on organizations.
The global phishing survey for the second half of 2012 was recently released by the Anti-Phishing Working Group (APWG) revealing how cybercriminals were able to break into the systems of hosting providers leading to massive phishing attacks on organizations.
There are only a handful of ways that hackers are able to spread their 'malware love' onto computer users around the world. The Internet is the prime source for spreading malware, which compromised sites or phishing sites play a large part in the efforts of hackers and their heinous acts.
By attacking hosting providers, or basically infiltrating hosting providers, hackers are able to hijack hundreds to thousands of websites at one time. The latest APWG global phishing survey for the second half of 2012 reveals to us that hackers were able to compromise a shared virtual server between July and December of 2012. At that time, attackers planted their malicious elements on every single domain hosted on the particular shared virtual server that they targeted.
Obviously, the initial outcome of hacking a hosting provider is never good especially considering how virtually all websites hosted in the constrained server environment can be compromised in one malicious blow.
"Breaking into hosting facilities is a high-yield activity for phishers," said Rod Rasmussen, president and CTO of IID, and a co-author of the study.
"This activity is part of a larger trend – we also see criminals hacking into shared hosting and using those servers for other malicious activities, such as launching denial-of-service attacks, infecting the computers of the legitimate website visitors via exploit code, and creating botnets."
The APWG second half of 2012 global phishing survey will give light to how effective phishing attacks involving shared virtual servers are in revealing that 47% of these attacks as a whole where secluded to such types of servers.
As far as the phishing websites go, the ones that were attacked and taken over by cybercrooks, most of the registrar companies of the sites are based in China. Certain domain name registrars and registries are taken advantage of, mostly concentrated in one place. For the attacks to cease, the registrar or registry companies must be proactive in mitigating such abuse.
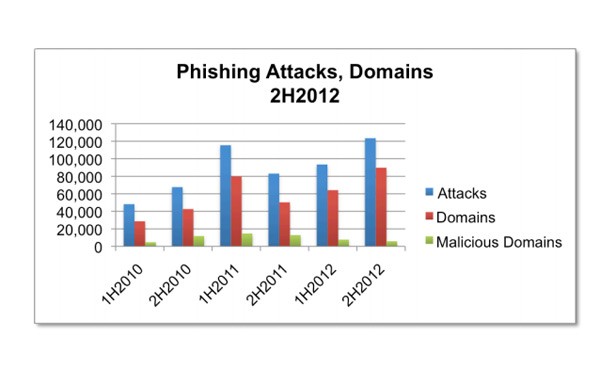
As far as the reach of how many phishing attacks were recorded within the APWG survey for the second half of 2012, it was revealed that 123,486 phishing attacks took place. Of those, 297 top-level domains were abused, and a total of 82% of the phishing sites were registered on .info, .tk and .com domains. During the first half of 2012, about 486 institutions were targeted, but during the second half of 2012 that number increased to 611. The contrast throughout the years is represented by half-years in the Phishing Attacks, Domains Chart in Figure 1 below. The complete Global Phishing Survey by the Anti-Phishing Working Group for the second half of 2012 can be viewed in its entirety here in PDF format.
Figure 1 - Phishing attacks on hosting providers yearly/half-year chart. Source: APWG