Zcrypt Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 71 |
| First Seen: | May 25, 2016 |
| Last Seen: | May 2, 2022 |
| OS(es) Affected: | Windows |
The zCrypt Ransomware is an encryption ransomware Trojan. Like most variants of these infections, the zCrypt Ransomware encrypts its victims' files and asks that the victims pay a ransom in exchange for decrypting their files. The zCrypt Ransomware poses a real threat to computers, making any files that have been encrypted by the zCrypt Ransomware useless until decrypted. Currently, it may not be possible to decrypt the files encrypted by the zCrypt Ransomware without access to the decryption key. The best way to recover from a the zCrypt Ransomware attack is to wipe the affected hard drive clean and restore the files that were encrypted from a backup. Because of this, preventive measures such as the use of a reliable security program and keeping backups of all files are essential in halting attacks like the zCrypt Ransomware and other ransomware Trojans.
Table of Contents
The the zCrypt Ransomware Infection Process
The most common way in which the zCrypt Ransomware is distributed is through corrupted spam email attachments and links. Computer users may receive an unsolicited email message that may appear to come from a legitimate source, such as a shipping company. These email messages will contain an embedded link or file attachment that, when opened, infects the victim's computer with threats. The zCrypt Ransomware is being spread through corrupted torrents distributed on popular peer-to-peer file sharing networks. Preventive measures, such as avoiding any unsolicited email attachments and using a reliable anti-spam filter, can prevent the zCrypt Ransomware from reaching your computer.
How the zCrypt Ransomware may Infect a Computer
The zCrypt Ransomware is not different from most other encryption ransomware Trojans. The main purpose of the the zCrypt Ransomware attack is to encrypt the victim's files. Because of this, as soon as the zCrypt Ransomware enters a computer, it will scan all drives for files with certain extensions. The following are examples of file types that may be targeted by threats like the zCrypt Ransomware:
.sql, .mp4, .7z, .rar, .m4a, .wma, .avi, .wmv, .csv, .d3dbsp, .zip, .sie, .sum, .ibank, .t13, .t12, .qdf, .gdb, .tax, .pkpass, .bc6, .bc7, .bkp, .qic, .bkf, .sidn, .sidd, .mddata, .itl, .itdb, .icxs, .hvpl, .hplg, .hkdb, .mdbackup, .syncdb, .gho, .cas, .svg, .map, .wmo, .itm, .sb, .fos, .mov, .vdf, .ztmp, .sis, .sid, .ncf, .menu, .layout, .dmp, .blob, .esm, .vcf, .vtf, .dazip, .fpk, .mlx, .kf, .iwd, .vpk, .tor, .psk, .rim, .w3x, .fsh, .ntl, .arch00, .lvl, .snx, .cfr, .ff, .vpp_pc, .lrf, .m2, .mcmeta, .vfs0, .mpqge, .kdb, .db0, .dba, .rofl, .hkx, .bar, .upk, .das, .iwi, .litemod, .asset, .forge, .ltx, .bsa, .apk, .re4, .sav, .lbf, .slm, .bik, .epk, .rgss3a, .pak, .big, wallet, .wotreplay, .xxx, .desc, .py, .m3u, .flv, .js, .css, .rb, .png, .jpeg, .txt, .p7c, .p7b, .p12, .pfx, .pem, .crt, .cer, .der, .x3f, .srw, .pef, .ptx, .r3d, .rw2, .rwl, .raw, .raf, .orf, .nrw, .mrwref, .mef, .erf, .kdc, .dcr, .cr2, .crw, .bay, .sr2, .srf, .arw, .3fr, .dng, .jpe, .jpg, .cdr, .indd, .ai, .eps, .pdf, .pdd, .psd, .dbf, .mdf, .wb2, .rtf, .wpd, .dxg, .xf, .dwg, .pst, .accdb, .mdb, .pptm, .pptx, .ppt, .xlk, .xlsb, .xlsm, .xlsx, .xls, .wps, .docm, .docx, .doc, .odb, .odc, .odm, .odp, .ods, .odt.
Once the zCrypt Ransomware encrypts the victim's files, it drops text and HTML files containing its ransom message. The zCrypt Ransomware also changes the affected computer's Desktop image to display the same content. The zCrypt Ransomware's ransom message alerts the victim about what has happened and includes instructions on how to buy BitCoin and pay the ransom amount, which is set at 1.2 BitCoin. The files encrypted by the zCrypt Ransomware cannot be decrypted without the decryption key currently.
Dealing with the zCrypt Ransomware
Malware analysts strongly advise computer users to avoid paying the zCrypt Ransomware ransom. Paying the asked fee allows con artists to continue creating these threat attacks and preying on inexperienced computer users. Backing up all files will make you invulnerable to these attacks and will cost only a fraction of what it would cost to recover from an attack such as the zCrypt Ransomware.
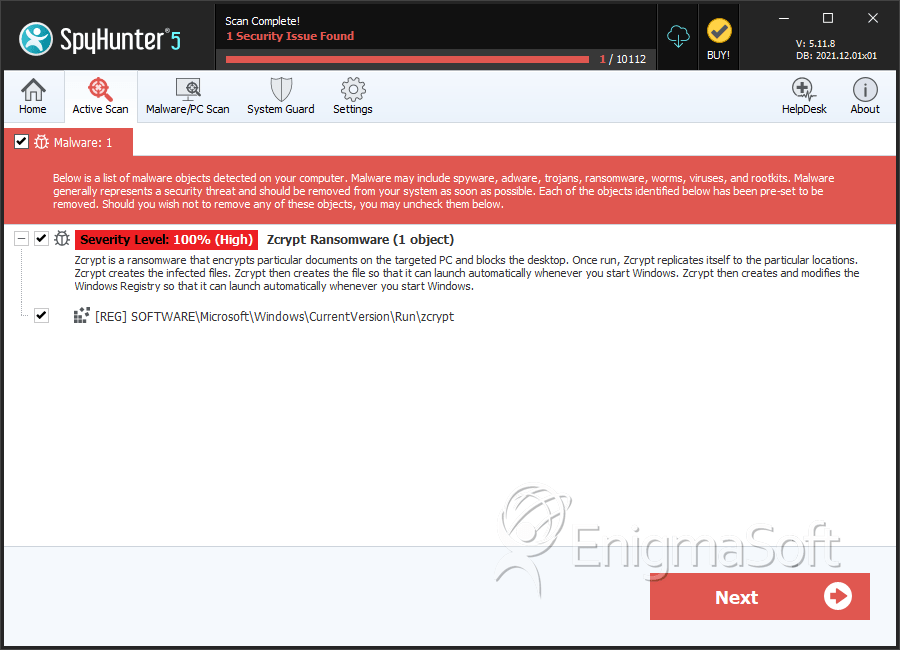
SpyHunter Detects & Remove Zcrypt Ransomware