Windows Anti-Malware Patch
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
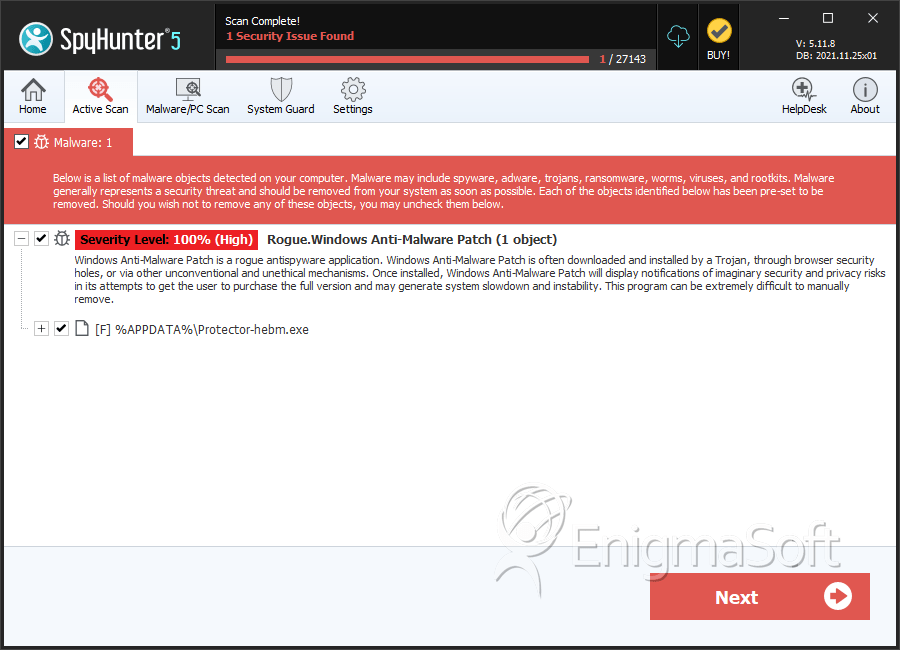
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 15 |
| First Seen: | August 11, 2012 |
| Last Seen: | January 8, 2020 |
| OS(es) Affected: | Windows |
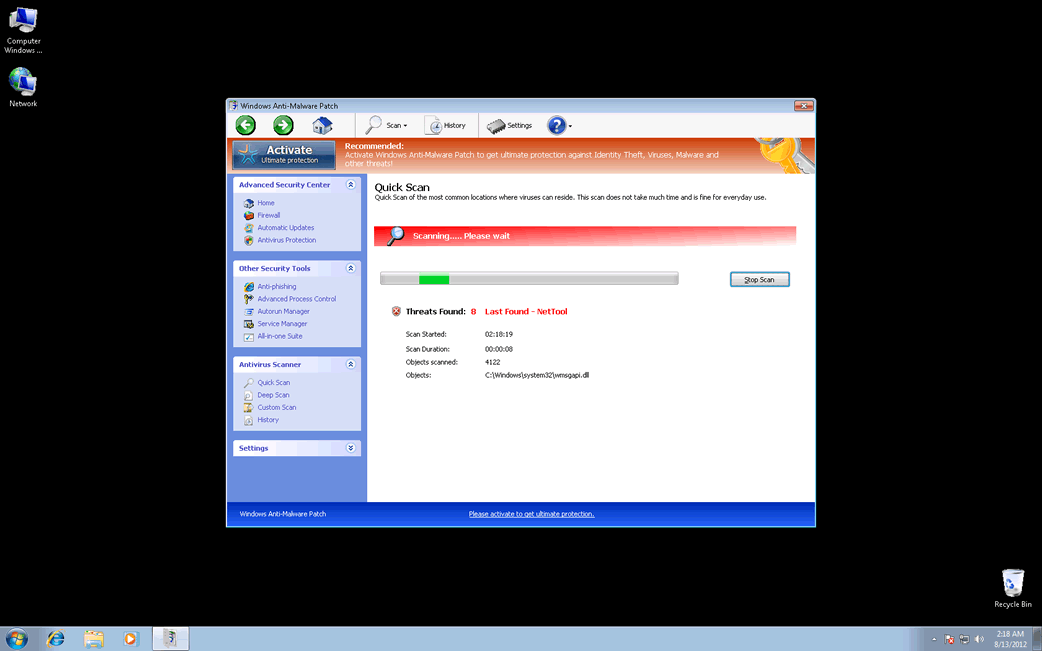
Windows Anti-Malware Patch Image
Windows Anti-Malware Patch is neither a security patch nor an anti-malware tool. Windows Anti-Malware Patch is actually a malware infection labeled as a rogue anti-malware program. Rogue anti-malware programs such as Windows Anti-Malware Patch have the main goal of convincing PC users that their machine is infected with malware by posing as legitimate anti-malware tools. This is part of a known online scam designed to snatch away inexperienced computer users' money. Windows Anti-Malware Patch itself belongs to a very large family of these kinds of malware threats known as FakeVimes.

The FakeVimes family of malware has existed in one way or another since 2009. In the years since, criminals have released dozens of these fake security programs. Although most reliable anti-malware applications are well prepared to deal with FakeVimes-related malware infection, variants of FakeVimes malware released in 2012 (including Windows Anti-Malware Patch itself) often include a rootkit component from the Sirefef family. This rootkit component makes these FakeVimes variants more difficult to remove and detect than ever before. Because of this, you may require the help of an anti-rootkit tool to remove Windows Anti-Malware Patch completely.
Table of Contents
How Criminals Attempt to Rob Your Money Utilizing Windows Anti-Malware Patch
The main goal of the Windows Anti-Malware Patch scam is to persuade computer users that they must purchase an unnecessary and useless upgrade which is usually quite expensive. Some variants of FakeVimes that carry out this scam include programs such as Virus Melt, Presto TuneUp, Fast Antivirus 2009, Extra Antivirus, Windows Security Suite, Smart Virus Eliminator, Packed.Generic.245, Volcano Security Suite, Windows Enterprise Suite, Enterprise Suite, Additional Guard, PC Live Guard, Live PC Care, Live Enterprise Suite, Security Antivirus, My Security Wall, CleanUp Antivirus, Smart Security, Windows Protection Suite, Windows Work Catalyst. All of these fake security programs will issue fake notifications, cause browser redirects and application crashes. ESG malware analysts strongly advise not to purchase Windows Anti-Malware Patch or any other fake security applications that are part of the FakeVimes family.
Removing Windows Anti-Malware Patch Safely from Your Computer
Although it is entirely possible to remove Windows Anti-Malware Patch manually, ESG security researchers advise using a reliable anti-malware program with anti-rootkit technology. Incorrect removal of Windows Anti-Malware Patch can damage your operating system and be ineffective. You can 'register' Windows Anti-Malware Patch with the registration code 0W000-000B0-00T00-E0020 in order to stop Windows Anti-Malware Patch from displaying annoying error messages or causing other symptoms. ESG security researchers note that using the above code to 'register' Windows Anti-Malware Patch will not remove this malware intruder from your computer but can help as part of an overall treatment for your computer.
SpyHunter Detects & Remove Windows Anti-Malware Patch
Windows Anti-Malware Patch Video
Tip: Turn your sound ON and watch the video in Full Screen mode.
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | adf00fcc32c3eebe01adc18de4e6f014c7858b60af599c3b8fb372bafb1b8e2d.exe | 63fb15b80a2d8a5b875e00d9fc74b202 | 4 |
| 2. | %AppData%\Protector-[RANDOM].exe |
