Sirefef
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
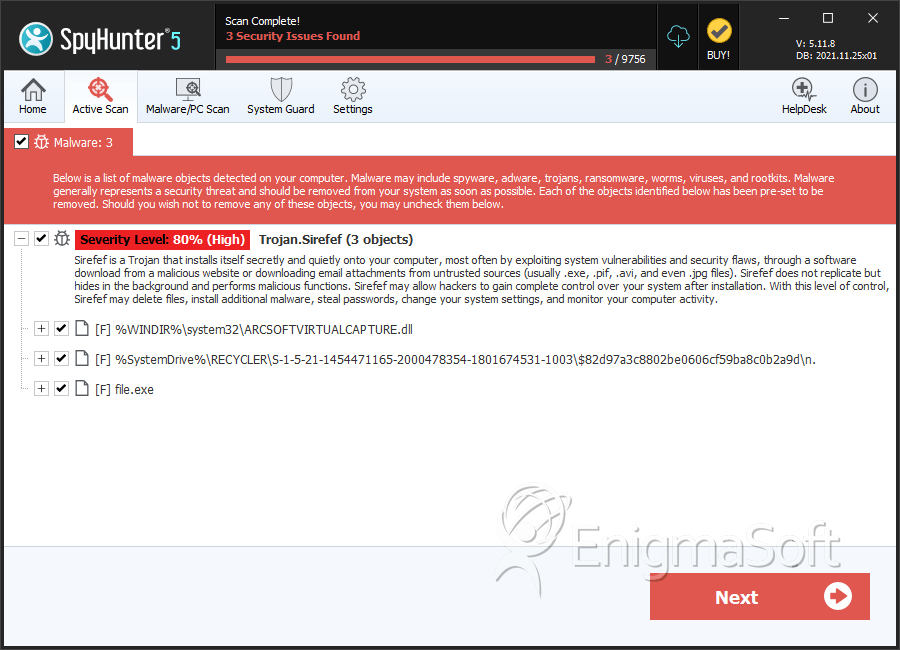
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 3,798 |
| First Seen: | September 20, 2011 |
| Last Seen: | November 28, 2024 |
| OS(es) Affected: | Windows |
Sirefef is a multi-component malware family that has been very active in 2012. Commonly known as a variant of the infamous ZeroAccess family of rootkits, any infection associated with a Sirefef component is considered extraordinarily severe by ESG security researchers. ESG security analysts strongly recommend using an advanced anti-malware solution with anti-rootkit capabilities to remove any component in the Sirefef family. Due to Sirefef's advanced rootkit techniques, this malware infection can evade detection and removal and improper removal can lead to irreparable operating system damage. Because of this, ESG malware analysts strongly dissuade any attempt to remove any Sirefef component manually.
Since there are many components involved in a Sirefef infection and countless variants of this malware infection, the actual payload of this infection varies from one case to another. ESG security researchers have noted that the Sirefef family of malware has been used to protect and install browser hijackers, fake security programs (Sirefef has been particularly linked to a massive outbreak of FakeVimes infections in 2012), and banking Trojans. However, most variants in the Sirefef family will have the following features:
- Malware in the Sirefef family has the ability to set up a backdoor into the compromised computer and contact a remote host in order to receive or send data.
- Sirefef malware can download and execute malicious files from a remote server.
- Malware components of the Sirefef family use advanced rootkit techniques to evade detection by most security programs and have the ability to disable many security applications and Windows components that are not properly updated.
Malware in the Sirefef family tend to infect system drivers and can reinstall themselves automatically after removal. They will also use advanced encryption to hide their components in a hidden file system within the infected hard drive. Due to the severity of a Sirefef-related infection, some essential system files may become irrevocably corrupted. In these cases, it may be necessary to reinstall your operating system and lose your data completely. The AA, AC, and AH variants of the Sirefef family (Trojan:Win32/Sirefef.AA, for example) will typically infect the victim's computer system so severely that it may be necessary to wipe the victim's hard drive and reinstall Windows entirely in order to be completely sure that the Sirefef infection has been removed completely.
SpyHunter Detects & Remove Sirefef
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | services.exe | 014a9cb92514e27c0107614df764bc06 | 3,687 |
| 2. | cdralw2k.dll | 11028c6a84a967070cb1286550f2058f | 35 |
| 3. | n. | ba8c8f4e925dad0cf586d50b21e45c4d | 20 |
| 4. | n. | b7c68d4a8c8a26616277bf1ff68d91e2 | 11 |
| 5. | n. | ae9388af2150a021069fc330f2ba3038 | 8 |
| 6. | n. | ae3981ec9692fcc8861db818e761bff8 | 3 |
| 7. | afd.sys | ||
| 8. | mrxsmb.sys | ||
| 9. | i8042prt.sys | ||
| 10. | netbt.sys | ||
| 11. | raspppoe.sys | ||
| 12. | win32k.sys | ||
| 13. | ipsec.sys | ||
| 14. | serial.sys | ||
| 15. | file.exe | 17ccd894ee2ac81292487a367ac84c53 | 0 |
