Trojan.Barys
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 11,310 |
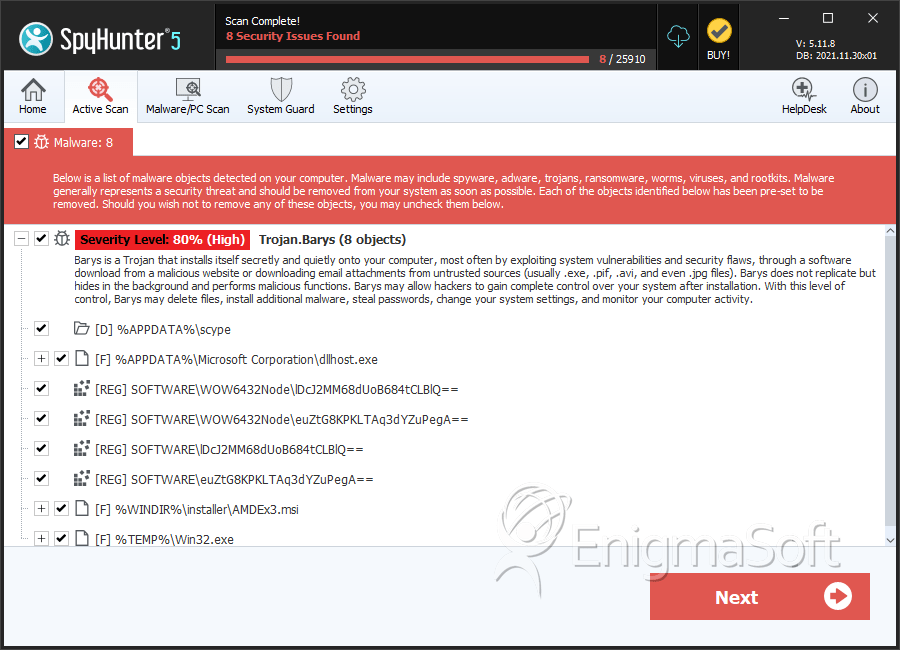
| Threat Level: | 80 % (High) |
| Infected Computers: | 2,018 |
| First Seen: | April 3, 2012 |
| Last Seen: | September 3, 2023 |
| OS(es) Affected: | Windows |
The Barys malware falls in the category of a Trojan Downloader and is programmed to allow its operators to download and upload files to your computer without you noticing it Malware researchers note that the Barys Trojan has some interesting features like the implementation of the Dropbox online file storage service. The Barys Trojan also could be encountered under the name of Trojan:Win32/Congrim. The Barys Trojan may be delivered to users via spam campaigns or travel bundled with free program installers that are promoted on suspicious websites. The Barys Trojan is known to make TCP connections via port 443 to remote hosts such as Software.trickip.net, 83.133.127.200, Weaversbase.com and Cms.abmr.net.
The Congrim (Barys) Trojan might install its main executable in the AppData folder, and its support components in the Temp folder to prevent easy detection. The Barys Trojan can provide its operators with a remote access to infected systems and allow them to run arbitrary code that may inflict severe damages to single computers and networks alike. The Barys Trojan could be instructed to download and install cryptomalware like the Onion Ransomware and the Locker Ransomware. Malware researchers point out that the Barys Trojan may create a Mutex in the Windows Registry to prevent more than one instance from running on infected systems. Additionally, the Barys (Congrim) Trojan may use TMP and DLL files to carry out commands and inject code into running processes like explorer.exe, dw20.exe and iexplorer.exe. The Barys Trojan may modify the security settings of Internet Explorer to tag its 'Command and Control' servers as safe. The Barys Trojan Downloader is written with the Microsoft C++ programming language and may run on all Windows versions and architectures. Therefore, you should install a renowned anti-malware solution to prevent the infiltration of the Barys Trojan or clean the infected machine.
Table of Contents
SpyHunter Detects & Remove Trojan.Barys
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | AMDEx3.msi | 07e30abd8c44221053a93e706c13dbfd | 113 |
| 2. | dllhost.exe | 9aca244ac7d1805ce5998764761141b7 | 89 |
| 3. | AMDEx3.msi | 13588a92d58cf32b972e71e4878bf789 | 33 |
| 4. | AMDEx3.msi | 90080da4654d078064c8a6b1fd89c4d8 | 32 |
| 5. | AMDEx3.msi | a5734cefcf843cb733ce34e869902c74 | 30 |
| 6. | amdex3.msi | e9a47c0f1d0974f6d7dcb3e1e069eaaa | 25 |
| 7. | AMDEx3.msi | a53b02cf714e75a18a60f5c9e11a545b | 24 |
| 8. | file.exe | b3c0abefe12f511f0b625039804185fb | 18 |
| 9. | AMDEx3.msi | b1efb08443b114d5c7d422312dc59ef6 | 16 |
| 10. | AMDEx3.msi | 9fcbe186e76f5434ad87595f0a4433bc | 4 |
| 11. | dllhost.exe | 5c91601e3ceedf54069feb57d9bc0f79 | 4 |
| 12. | AMDEx3.msi | 9759482e6f93c7ca41a9f05de3e3be40 | 2 |
| 13. | AMDEx3.msi | de717f4f98a4f0963554e725ea12945d | 2 |
| 14. | Win32.exe | 2f2fec8c582fc7e1459fde95625ac090 | 2 |
| 15. | AMDEx3.msi | 3dcce5a59d9017f05a0e26cae4b8a79a | 1 |
| 16. | AMDEx3.msi | db5bac62cbdb394b53900b7ffa0b80fa | 1 |
| 17. | AMDEx3.msi | 0dbf938908c20144e8e359542f6f8fb4 | 1 |
| 18. | AMDEx3.msi | 0b7ad487dbc603f449171c020a9781db | 1 |
| 19. | explorer.exe | 426a6e545a2ea7f1eaf4b895f6cd10aa | 1 |
| 20. | file.exe | 9284e7df99f7c54beb0b4a4471c4a204 | 0 |
| 21. | file.exe | 7ce5f02c49eccf00abce59a1d267dd3a | 0 |
| 22. | file.exe | de1cf2d6f8b70e672de8b07f46f3ebff | 0 |
| 23. | file.exe | 2de7466e8d58342becc48fe790fc7649 | 0 |
| 24. | file.exe | 36e8f222aef751257428b7db83c7372b | 0 |
| 25. | 1964f777975d9a809bd6171348572a4e4db287e557f26fccae66bbbe1ba0a541.exe | a7261182d71b38248f429e62004dd52e | 0 |
| 26. | 229022f4344e4dd9d34649728bfd5edf705b77a5b440c8875b2aaa1eeb96128f.exe | c70fba80e0989170a3199a4014532f68 | 0 |
| 27. | wincsa.exe | ce175ad8406b4b791c099ca8c4072b4c | 0 |
Registry Details
Directories
Trojan.Barys may create the following directory or directories:
| %APPDATA%\scype |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.