@LOCKED Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 1 |
| First Seen: | March 10, 2016 |
| OS(es) Affected: | Windows |
The @LOCKED Ransomware is a variant of Unlock92, a known family of ransomware Trojans. Several variants in this ransomware family have been observed in 2018. The @LOCKED Ransomware, like most modern ransomware Trojans, is commonly delivered to victims through corrupted spam email appendage. The victims will be presented with spam email message with an appended text document, which encompasses corrupted macro scripts that were programmed to download and install the @LOCKED Ransomware onto the victim's computer. Once the @LOCKED Ransomware has been installed, it will take the victim's files hostage and demand a ransom payment for restoring access to the infected data.
Table of Contents
Symptoms of a @LOCKED Ransomware Attack
The @LOCKED Ransomware is installed in the AppData directory and uses the AES encryption to make the victim's data inaccessible. The @LOCKED Ransomware targets the user-generated data in its attack, which may include a wide variety of images, texts, media files, and numerous other file types. The file types that threats like the @LOCKED Ransomware target in these attacks include:
.jpg, .jpeg, .raw, .tif, .gif, .png, .bmp, .3dm, .max, .accdb, .db, .dbf, .mdb, .pdb, .sql, .dwg, .dxf, .cpp, .cs, .h, .php, .asp, .rb, .java, .jar, .class, .py, .js, .aaf, .aep, .aepx, .plb, .prel, .prproj, .aet, .ppj, .psd, .indd, .indl, .indt, .indb, .inx, .idml, .pmd, .xqx, .xqx, .ai, .eps, .ps, .svg, .swf, .fla, .as3, .as, .txt, .doc, .dot, .docx, .docm, .dotx, .dotm, .docb, .rtf, .wpd, .wps, .msg, .pdf, .xls, .xlt, .xlm, .xlsx, .xlsm, .xltx, .xltm, .xlsb, .xla, .xlam, .xll, .xlw, .ppt, .pot, .pps, .pptx, .pptm, .potx, .potm, .ppam, .ppsx, .ppsm, .sldx, .sldm, .wav, .mp3, .aif, .iff, .m3u, .m4u, .mid, .mpa, .wma, .ra, .avi, .mov, .mp4, .3gp, .mpeg, .3g2, .asf, .asx, .flv, .mpg, .wmv, .vob, .m3u8, .dat, .csv, .efx, .sdf, .vcf, .xml, .ses, .qbw, .qbb, .qbm, .qbi, .qbr , .cnt, .des, .v30, .qbo, .ini, .lgb, .qwc, .qbp, .aif, .qba, .tlg, .qbx, .qby , .1pa, .qpd, .txt, .set, .iif, .nd, .rtp, .tlg, .wav, .qsm, .qss, .qst, .fx0, .fx1, .mx0, .fpx, .fxr, .fim, .ptb, .ai, .pfb, .cgn, .vsd, .cdr, .cmx, .cpt, .csl, .cur, .des, .dsf, .ds4, , .drw, .eps, .ps, .prn, .gif, .pcd, .pct, .pcx, .plt, .rif, .svg, .swf, .tga, .tiff, .psp, .ttf, .wpd, .wpg, .wi, .raw, .wmf, .txt, .cal, .cpx, .shw, .clk, .cdx, .cdt, .fpx, .fmv, .img, .gem, .xcf, .pic, .mac, .met, .pp4, .pp5, .ppf, .nap, .pat, .ps, .prn, .sct, .vsd, .wk3, .wk4, .xpm, .zip, .rar.
When the @LOCKED Ransomware attacks a computer, it will connect with its Command and Control servers to send data about the infected computer. The @LOCKED Ransomware encrypts the files using a method that makes it easy to recognize them because the @LOCKED Ransomware marks them with the addition of the file extension '.@LOCKED' to the file's name. The @LOCKED Ransomware delivers a ransom note in a text file that includes the following message, written both in Russian and English:
'Your files have been encrypted.
If you want to restore files, send one more file us to the e-mail: unk921@protonmail.com
Only in case you do not receive a response from the first email address
withit 24 hours, please use use TOR browser from www.torproject[.]com and see current
e-mail in hxxp://n3r2kuzhw2hx6j5[.]onion (hxxps://n3r2kuzhw2h7x6j5.tor2web[.]io/ - from any other browser w/o using a TOR)
Using another tools could corrupt your files, in case of using third party
software we dont give guarantees that full recovery is possible so use it on
your own risk.'
Dealing with the @LOCKED Ransomware Infection
Computer users are advised against contacting the criminals responsible for the @LOCKED Ransomware attack. Instead, steps should be taken to protect their data preemptively. The best protection is to have file backups. Threats like the @LOCKED Ransomware can be intercepted by updated security applications (although these will generally not be able to restore files that have been encrypted in an attack) before the victim's data is compromised.
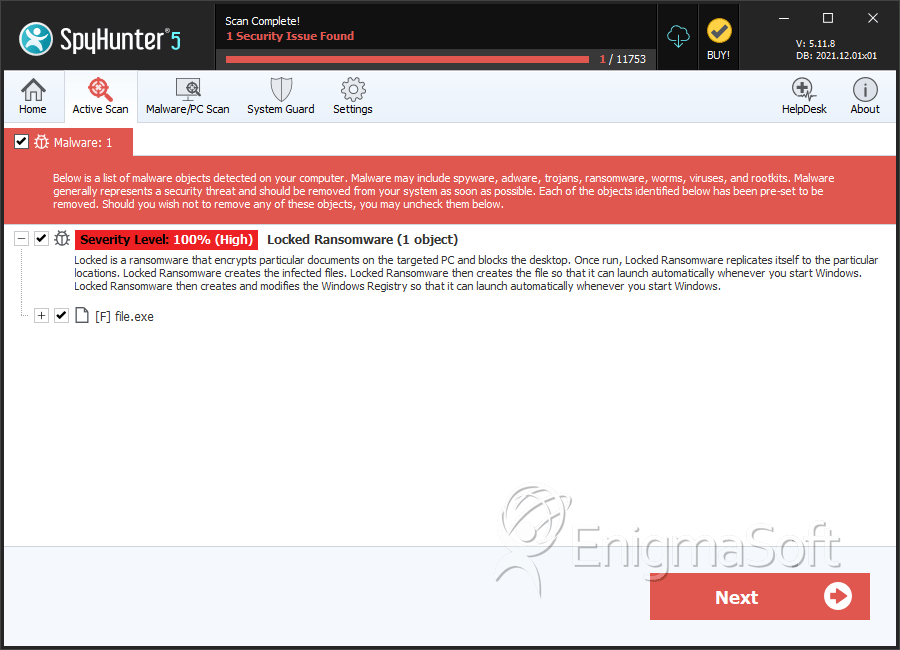
SpyHunter Detects & Remove @LOCKED Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | f578c991d6dbc426103c119f8c97e577 | 1 |

