KEYHolder Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 14 |
| First Seen: | December 12, 2014 |
| Last Seen: | April 2, 2020 |
| OS(es) Affected: | Windows |
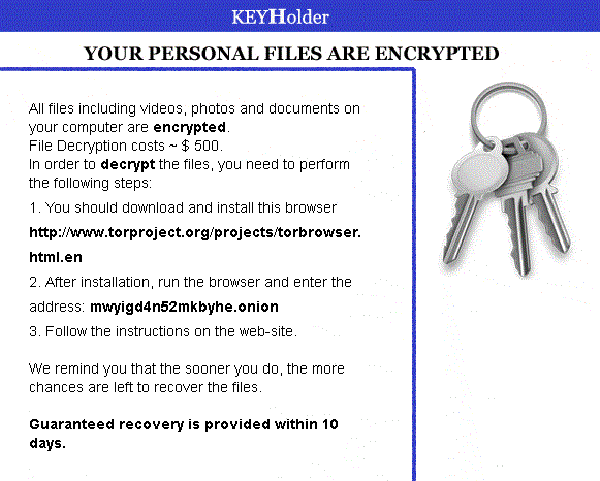
KEYHolder Ransomware Image
The KEYHolder Ransomware is an encryption ransomware infection that encrypts the PC user's files and then requests the payment of $500 USD in order to restore the victim's files. The KEYHolder Ransomware will scan the victim's computer for documents, images, videos and other files to encrypt. Once the KEYHolder Ransomware encrypts a file, it cannot be accessed. Whenever the KEYHolder Ransomware encrypts a file on the victim's computer, the KEYHolder Ransomware also drops an HTML and a GIF file into the same folder containing decryption instructions. The instructions read as follows:
YOUR PERSONAL FILES ARE ENCRYPTED
All files including videos, photos and documents on your computer are encrypted.
File Decryption costs ~ $500.
In order to decrypt the files, you need to perform the following steps:
1. You should download and install this browser: http://www.torproject.org/projects/torbrowser.html.en
2. After installation, run the browser and enter the address: mwyigd4n52mkbyhe.onion
3. Follow the instructions on the Web-site.
We remind you that the sooner you do, the more chances are left to recover the files.
Guaranteed recovery is provided within 10 days.
Unfortunately, encryption ransomware like the KEYHolder Ransomware may be worse to deal with than other types of ransomware. While many ransomware Trojans take the victim's computer hostage by preventing access, threats like the KEYHolder Ransomware Trojan alter the victim's files, making it nearly impossible to restore the encrypted files without the encryption key or other components.
Table of Contents
How the KEYHolder Ransomware Tries to Take Advantage of PC Users
As can be seen in the KEYHolder Ransomware message, the people behind this tactic want computer users to use the Tor browser (designed to access hidden portions of the Internet that are known for their anonymity) to access their website and pay the ransom. It is not probable that you will get your files back after following the KEYHolder Ransomware's instructions. Although they may give you a decryption utility, they could also take your money and then not give you anything in return. It is advised not to pay the KEYHolder Ransomware ransom or follow this threat's instructions. Unfortunately, Windows Restore will not recover your files.
Dealing with the KEYHolder Ransomware Infection
The KEYHolder Ransomware infection is not hard to remove. Most security programs that are fully updated should be capable of removing the KEYHolder Ransomware. Unfortunately, restoring encrypted files is beyond the abilities of most security programs. To restore encrypted files, it may be necessary to use an external utility made specifically for this purpose. With time, previous encryption ransomware infections have been countered by the release of these types of utilities by security researchers. However, this may take some time, and a solution for the KEYHolder Ransomware encrypted files may not be available. This is why always having a backup is important, both to protect yourself and avoid giving money and power to third parties such as those responsible for the KEYHolder Ransomware Trojan. Many websites and online services may be offering the KEYHolder Ransomware decryption guides or utilities, but unless backed by a reputable PC security firm or researcher, these are probably not legitimate.
Preventing a KEYHolder Ransomware Infection
In most cases, the KEYHolder Ransomware spreads through spam email attachments. In many cases, the KEYHolder Ransomware-containing emails are sent to specific corporations or companies in an attempt to infect more than one computer in a more profitable environment. This also allows third parties to create spam email messages that are more effective, specifically targeting a particular audience. The email message may contain a body that is crafted to trick inexperienced computer users into clicking on the attached file or the embedded link. The attachment may contain the KEYHolder Ransomware Trojan itself or, more likely, a backdoor Trojan. These types of threats may create an entrance into your computer that then allow a third party to install other types of threats (such as the KEYHolder Ransomware) or collect the contents of the infected computer.

