FakeDef
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 20 |
| First Seen: | January 16, 2013 |
| OS(es) Affected: | Windows |
FakeDef is a family of rogue security applications. The FakeDef family of threats is used to extort money from inexperienced computer users by impersonating legitimate security programs. FakeDef will harass computer users with fake warnings of threats on the infected computer. The purpose of this is to convince PC users that they need to acquire a 'complete version' of FakeDef in order to remove these nonexistent threat infections. There are numerous rogue security programs in the FakeDef family of threats, usually adjusting to the affected computer's operating system. Some of the names of threats in the FakeDef family that have been observed include Vista Defender, Win 7 Defender, Windows Server Defender, Win 8 Defender 2013 and Xpdefender. There isn't almost any difference between rogue security programs from the FakeDef family, but different names and slight interface changes to match the infected operating system.
Table of Contents
The FakeDef Family Members can Cause Numerous Problems to PC Users
Typically, FakeDef is distributed using threat distribution techniques such as spam email messages social engineering and attack websites. The following are the steps typically taken by threats in the FakeDef family:
- Once a threat from the FakeDef family is installed, it makes harmful changes to the affected computer's settings. These changes allow FakeDef to interfere with other software in the infected computer and activate itself automatically.
- FakeDef will do anything possible to prove to PC users that their machines are full of threats. To do this, FakeDef will display numerous irritating, fake error messages and alarming, bogus system scans. These will all alert the computer user that numerous threats have been found on the affected computer.
- FakeDef infections may also cause other problems on the affected computer, designed to prevent removal of the rogue security program and to convince computer users that there is a rampant threat infection on the affected computer. FakeDef may block all executable files from running and cause Web browser redirects.
- Trying to use FakeDef to remove these supposed threats leads to additional error messages claiming that it is necessary to spend money buying a 'full version' of the fraudulent security program.
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| Panda | Trj/OCJ.A |
| AVG | Dropper.Generic6.CNVC |
| Fortinet | W32/Injector.BNS!tr |
| Ikarus | Trojan-Dropper.Win32.Injector |
| AntiVir | TR/Dldr.Injector.I |
| Comodo | TrojWare.Win32.Trojan.Agent.Gen |
| Kaspersky | Trojan-Dropper.Win32.Injector.fzuj |
| Avast | Win32:Trojan-gen |
| Symantec | Suspicious.Cloud.5 |
| K7AntiVirus | Riskware |
| McAfee | Generic.tfr!cq |
| CAT-QuickHeal | TrojanDropper.Injector.fzuj |
| AVG | Generic30.CCAB |
| Fortinet | W32/Duhsad.ASD!tr |
| Ikarus | Win32.Kryptik |
SpyHunter Detects & Remove FakeDef
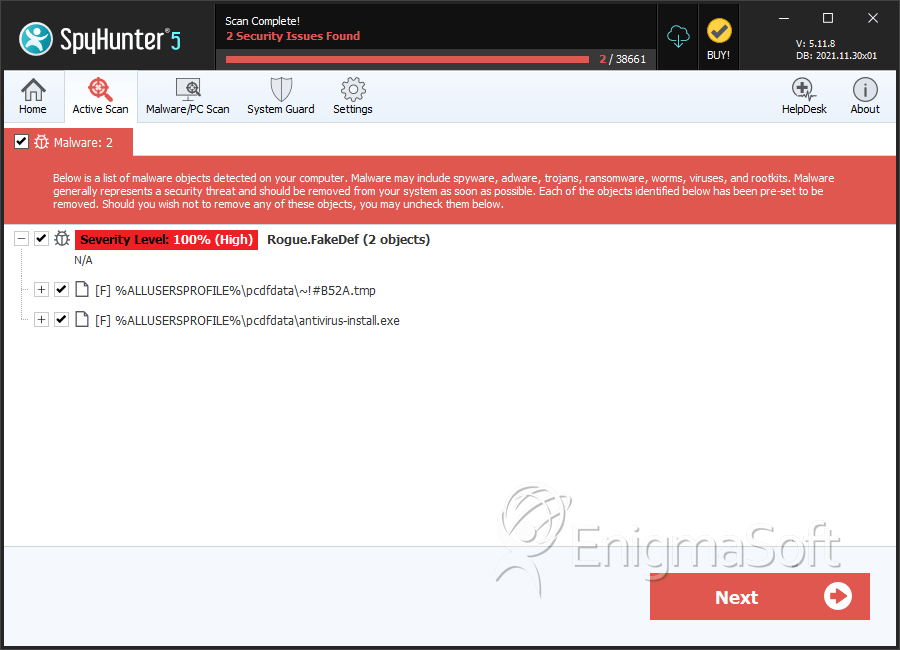
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | ~!#B52A.tmp | 2d8989cc253f3a1d92c2b7da1908d600 | 16 |
| 2. | antivirus-install.exe | b8622bd2428618367f1ca5aef29c86dd | 4 |

