Cryptolocker 1.0.0 Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 729 |
| First Seen: | September 11, 2013 |
| Last Seen: | April 8, 2022 |
| OS(es) Affected: | Windows |
The Cryptolocker 1.0.0 Ransomware is a ransomware Trojan that originated in Turkey, and was created by a programmer that is known as 'Alp.' The Cryptolocker 1.0.0 Ransomware is an upgrade of CryptoLocker, a well-known ransomware Trojan that was first observed in 2013. This ransomware Trojan was in development through the end of 2015, when its development was interrupted. Apparently, the Cryptolocker 1.0.0 Ransomware is part of an effort to return to the development of this well-known threat. The Cryptolocker 1.0.0 Ransomware uses the RSA-2048 encryption, a strong obfuscation procedure, a different packaging and interface, and an effective ransomware attack.
Table of Contents
How the Cryptolocker 1.0.0 Ransomware may Infect a Computer
The Cryptolocker 1.0.0 Ransomware is being distributed using social engineering techniques and corrupted email attachments. The Cryptolocker 1.0.0 Ransomware project was observed on GitHub and seems to be distributed as a PDF file that claims to be a job application or other legitimate file. Once the file is opened, the Cryptolocker 1.0.0 Ransomware infects the victim's computer, encrypting files on all local hard drives, external memory devices connected to the infected computer, and directories shared on a network. The Cryptolocker 1.0.0 Ransomware will encrypt the following file types during its attack:
.odt , .ods , .odp , .odm , .odc , .odb , .doc , .docx , .docm , .wps , .xls , .xlsx , .xlsm , .xlsb , .xlk , .ppt , .pptx , .pptm , .mdb , .accdb , .pst , .dwg , .xf , .dxg , .wpd , .rtf , .wb2 , .mdf , .dbf , .psd , .pdd , .pdf , .eps , .ai , .indd , .cdr , .jpg , .jpe , .dng , .3fr , .arw , .srf , .sr2 , .bay , .crw , .cr2 , .dcr , .kdc , .erf , .mef , .mrwref , .nrw , .orf , .raf , .raw , .rwl , .rw2 , .r3d , .ptx , .pef , .srw , .x3f , .der , .cer , .crt , .pem , .pfx , .p12 , .p7b , .p7c , .c , .cpp , .txt , .jpeg , .png , .gif , .mp3 , .html , .css , .js , .sql , .mp4 , .flv , .m3u , .py , .desc , .con , .htm , .bin , .wotreplay , .unity3d , .big , .pak , .rgss3a , .epk , .bik , .slm , .lbf , .sav , .lng , .ttarch2 , .mpq , .re4 , .apk , .bsa , .cab , .ltx , .forge , .asset , .litemod , .iwi , .das , .upk , .bar , .hkx , .rofl , .DayZProfile , .db0 , .mpqge , .vfs0 , .mcmeta , .m2 , .lrf , .vpp_pc , .ff , .cfr , .snx , .lvl , .arch00 , .ntl , .fsh , .w3x , .rim ,psk , .tor , .vpk , .iwd , .kf , .mlx , .fpk , .zip , .vtf , .001 , .esm , .blob , .dmp , .layout , .menu , .ncf , .sid , .sis , .ztmp , .vdf , .mcgame , .fos , .sb , .im , .wmo , .itm , .map , .wmo , .sb , .svg , .cas , .gho , .iso , .rar , .syncdb , .mdbackup , .hkdb , .hplg , .hvpl , .icxs , .itdb , .itl , .mddata , .sidd , .sidn , .bkf , .qic , .bkp , .bc7 , .bc6 , .pkpass , .tax , .gdb , .qdf , .t12 , .t13 , .ibank , .sum , .sie , .sc2save , .d3dbsp , .wmv , .avi , .wma , .m4a , .7z , .torrent , .csv , .cs , .jar , .java , .class.
The files that have been encrypted using the Cryptolocker 1.0.0 Ransomware Trojan will have the comment 'LOCKED File' added to the file's properties. The names and extensions of the affected files will remain the same, but their icon will become the icon for the default Text Editor. The Cryptolocker 1.0.0 Ransomware uses a ransom note that is displayed in a pop-up window that uses red and blue coloring and is named the Cryptolocker 1.0.0 Ransomware. The Cryptolocker 1.0.0 Ransomware ransom note contains the following text (originally in Turkish):
'Personal files
Photos and important files on the computer, videos, Documents, etc. were encrypted with a unique RSA-2048 key
RED [BUTTON]
- If you choose the RED, there are no copies. Goodbye to everything you have! We will delete your files.
Blue [BUTTON]
- If you take BLUE the story is better. I have the KEY with me. You can get rid of the Trojan and sleep comfortably.
Send me an email with the "Send Mail" button and save your files.
SEND MaiL'
Clicking on the RED button will delete all the encrypted files so that caution is paramount.
Dealing with the Cryptolocker 1.0.0 Ransomware
If your computer is infected with the Cryptolocker 1.0.0 Ransomware, ignore the ransom note and refrain from paying the Cryptolocker 1.0.0 Ransomware ransom. Instead, PC security researchers advise computer users to restore their files from a backup copy. Future infections also can be prevented with the help of a reliable, fully updated anti-malware application.
Aliases
13 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| AVG | Inject2.BWZN |
| Fortinet | W32/Bitman.FO!tr |
| Ikarus | Trojan.Win32.Injector |
| McAfee | Artemis!E78654D43FCF |
| Microsoft | Ransom:Win32/Tescrypt.A |
| Antiy-AVL | Trojan[Ransom]/Win32.Bitman |
| Sophos | Troj/Ransom-AST |
| DrWeb | Trojan.AVKill.36611 |
| Comodo | TrojWare.Win32.Ransom.Bitman.~NS |
| Kaspersky | Trojan-Ransom.Win32.Bitman.fo |
| Avast | Win32:Malware-gen |
| Symantec | Trojan.Gen |
| K7AntiVirus | Trojan ( 004bc9ff1 ) |
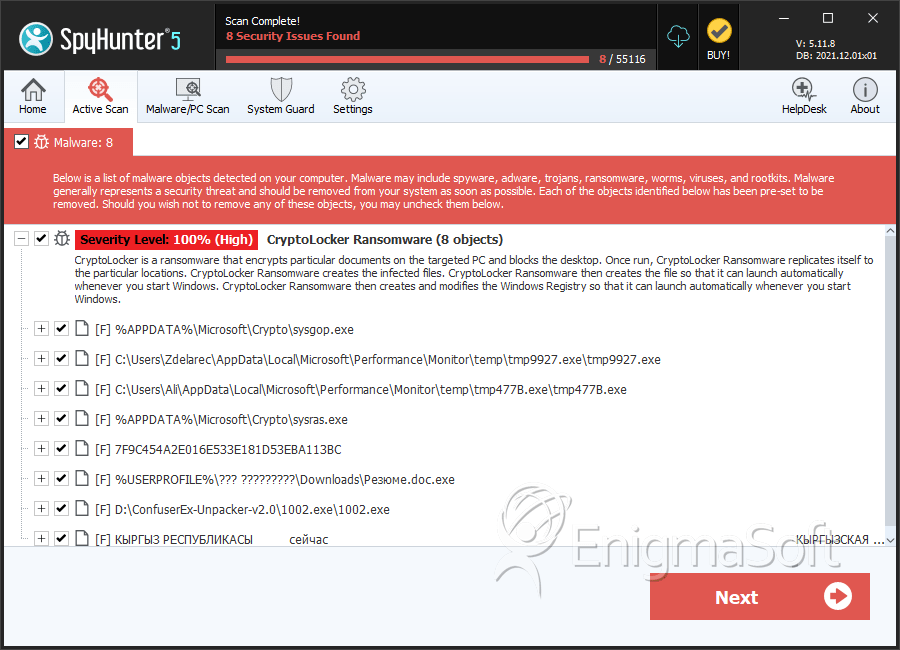
SpyHunter Detects & Remove Cryptolocker 1.0.0 Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | sysgop.exe | 3c282af747b4f70340dca3170d55ae29 | 247 |
| 2. | tmp9927.exe | eb2cde846127106689d14afe7911bcec | 151 |
| 3. | tmp477B.exe | 1b21b27589ddc173ba795213e108a096 | 39 |
| 4. | sysras.exe | 881f86bf4bb4b9f0e993b2853a0a27cf | 36 |
| 5. | 7F9C454A2E016E533E181D53EBA113BC | 7f9c454a2e016e533e181d53eba113bc | 14 |
| 6. | 1002.exe | 829dde7015c32d7d77d8128665390dab | 10 |
| 7. | Резюме.doc.exe | 12303bbfe7194fd4f0070cd4d1005209 | 8 |
| 8. | КЫРГЫЗ РЕСПУБЛИКАСЫ сейчас КЫРГЫЗСКАЯ РЕСПУБЛИКА.docx.exe | acf9873c86e35b9bee0db158befe8163 | 7 |
| 9. | d765e722e295969c0a5c2d90f549db8b89ab617900bf4698db41c7cdad993bb9 | 04fb36199787f2e3e2135611a38321eb | 7 |
| 10. | план части.docx.exe | bac4daf1ba563a5fdd01691441cedc9b | 6 |
| 11. | $R803NKR.exe | b8ebbc2a6001ff318e49e0ec679c185f | 3 |
| 12. | сопроводительное в прокуратуру.docx.exe | b51d416995590c6a35a0602cfd2df94d | 2 |
| 13. | Министерство образования и науки Кыргызской Республики.docx.exe | a686e81153a11ea2817ecf58a9b0b25d | 1 |
| 14. | Министерство образования и науки Кыргызской Республики1.docx.exe | 5bcb809524857f26a89ac67ffc80f6f5 | 1 |
| 15. | PROGRAMPEMBELAJARANKELAS4.docx.exe | 7c87cdad5223b0ac9e1a5e2e5cc0d20f | 1 |
| 16. | رزمايش.docx.exe | 64cc41e5aa1d5b34e6c49cbd9ffe9233 | 1 |
| 17. | Testing Draft 2.docx.exe | 9406c8ea0f180383d3a8d5fedb105bb1 | 1 |
| 18. | 3.DAFTAR-LAMPIRAN--wahabkhoter.blogspot.com.docx.exe | 85242fee40a9a0bc3ce6c20f52050643 | 1 |
| 19. | RPPTematikBerkarakterKelas1SDPengalamansms1.docx.exe | 14434f09c026e189161254a3230523e9 | 1 |
| 20. | Списывание.docx.exe | b870f4a3f292452971628fcb54d9067e | 1 |
| 21. | Инструкция как скачать чит и ссылка на него.docx.exe | 860bfffc08296bd13d43bef865b33f76 | 1 |
| 22. | Тесты по модулю Пищеварительная система для студентов 2-курса факультета лечебное дело.docx.exe | 49115ff6fe4016169c24ff3783010321 | 1 |
| 23. | Выписка из Протокола.docx.exe | 06dbb0786866ec652b12ddfcc204a735 | 1 |
| 24. | eb5eb336636e3f6cacf6c8db6bf4ea00 | eb5eb336636e3f6cacf6c8db6bf4ea00 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.