Coprofit Ads
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 20 % (Normal) |
| Infected Computers: | 130 |
| First Seen: | November 28, 2015 |
| Last Seen: | April 16, 2022 |
| OS(es) Affected: | Windows |
The Coprofit browser plug-in may be promoted to users as a shopping adviser that can help them save money and assist advertisers to provide exclusive offers to active online shoppers. However, the Coprofit shopping adviser is adware and might exploit its browser integration to determine your geographical location, read your Internet history and record your search terms on Google to execute behavioral marketing. The Coprofit adware may cover your browser surface with pop-up windows that invite you to shop for clothing, smartphones, shoes, accessories, books and everything in between that can be purchased online. Security experts note that the Coprofit adware may employ aggressive advertising techniques and utilize JavaScript to display banners, floating ad-boxes and inline ads that users cannot close until clicked upon.
The Coprofit adware may change your start page to Uber-Search.com that is associated with a browser hijacker and open several tabs loaded with promotions from sponsors. Needless to say, the activities of the Coprofit adware may claim a lot of your system resources and reduce the productivity of other running programs on your computer. The Coprofit adware functions similarly to Better Brain and Conduit Search, and may hide its main executable in the Temp folder that Windows uses to store cache files. Additionally, the Coprofit adware may load runtime DLL files when you start an online session in Google Chrome, Internet Explorer and Mozilla Firefox to facilitate its operations and avoid appearing in your extension and plug-in managers. The ads by Coprofit may not be safe and invite users to install badware like DownQuick and Fassurun that might cause browser crashes and problems with loading HTML5 media. Affected users that value security and optimal performance over coupons and discounts by adware like Coprofit should install a reputable anti-malware solution that can clean their Windows OS.
Table of Contents
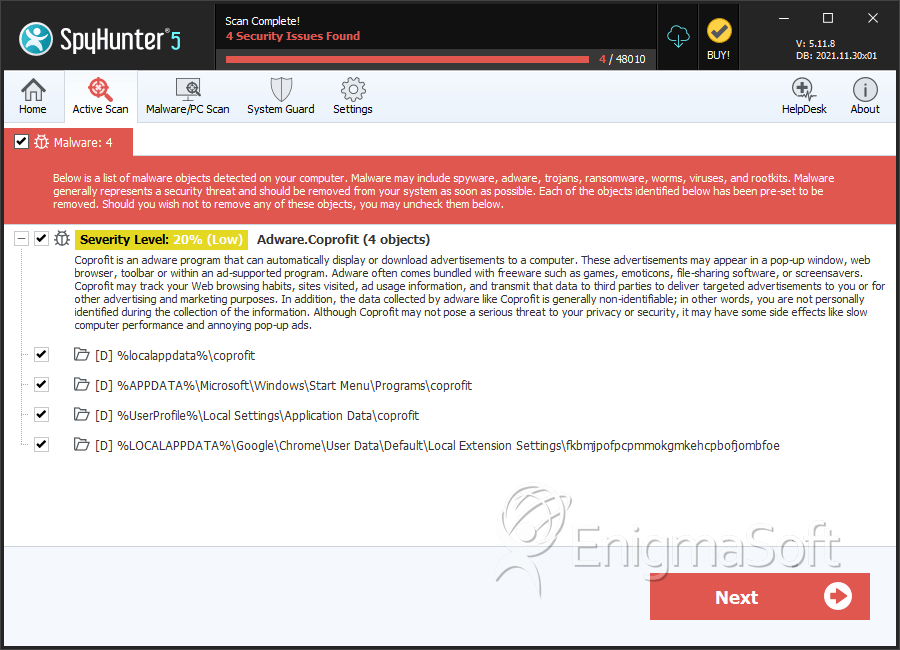
SpyHunter Detects & Remove Coprofit Ads
Directories
Coprofit Ads may create the following directory or directories:
| %APPDATA%\Microsoft\Windows\Start Menu\Programs\coprofit |
| %LOCALAPPDATA%\Google\Chrome\User Data\Default\Local Extension Settings\fkbmjpofpcpmmokgmkehcpbofjombfoe |
| %UserProfile%\Local Settings\Application Data\coprofit |
| %localappdata%\coprofit |
URLs
Coprofit Ads may call the following URLs:
| coprofit.ru |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.