Adware.Cling Clang
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
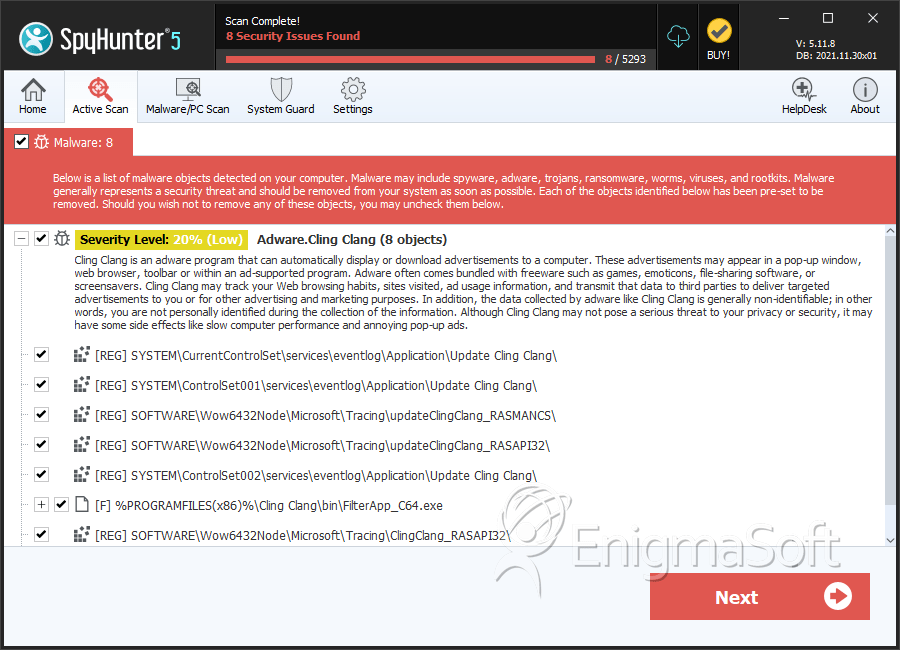
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 20 % (Normal) |
| Infected Computers: | 1,493 |
| First Seen: | February 6, 2014 |
| Last Seen: | May 4, 2023 |
| OS(es) Affected: | Windows |
Adware.Cling Clang is adware which is a component of a Web Cake adware group. Adware.Cling Clang is a potentially unwanted Web browser plug-in that may alter the default start page and search service and show pop-up advertisements and contextual in the Web browser of a PC. Cling Clang application is a free tool and supported by a variety of types of advertising, incorporating but not limited to banner, search, transitional and inline text advertisements. Advertisements and features that may occur on the websites visited by using Cling Clang are not connected with or endorsed by the websites. Some features and advertisement placements may encompass links to additional information and disabling instructions. The features, content and advertising of Cling Clang may be added, changed, discontinued, enabled or disabled at any time automatically and without extra announcement to the PC user.
Table of Contents
SpyHunter Detects & Remove Adware.Cling Clang
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | FilterApp_C64.exe | 39a18888bf75bd82562de783e71ea41d | 116 |
| 2. | XTLSApp.exe | 176abfd0ad9dfac5d0330a5b7783f174 | 71 |
| 3. | XTLSApp.exe | d565899030f84da81cc520f23eeafc12 | 57 |
| 4. | XTLSApp.exe | 06d00c1ed597c1b5a7877f0d091f9912 | 37 |
| 5. | FilterApp_C.exe | de2ee1b0097bb8e7aaea2e24a73ceada | 32 |
| 6. | XTLSApp.exe | e00a19f937a18dbadcb68a6205a4715a | 28 |
| 7. | ClingClang.PurBrowse64.exe | 4f0f7946ed7db0fb8afb2d9b0c4eaed7 | 26 |
| 8. | ClingClang.FirstRun.exe | 1161d07b03908cf950f566fe16be3beb | 9 |
| 9. | utilClingClang.exe | 459d3f50a47141676f8966a94c6bdaea | 2 |
| 10. | updateClingClang.exe | 5b6ed6c029daa5458a7868060e355a8a | 1 |
| 11. | utilClingClang.exe | 24219eea71099327cec845de39ad1026 | 1 |
| 12. | utilClingClang.exe | 59bd547f7974bb664867afbadd5f30fb | 1 |
| 13. | C:\Program Files\Cling Clang\updateClingClang.exe | ||
| 14. | C:\Program Files\Cling Clang\ClingClangUninstall.exe | ||
| 15. | C:\Program Files\Cling Clang\ClingClangBHO.dll |
Registry Details
Directories
Adware.Cling Clang may create the following directory or directories:
| %ProgramFiles%\Cling Clang |
| %ProgramFiles(x86)%\Cling Clang |
URLs
Adware.Cling Clang may call the following URLs:
| Cling Clang |
| Clingclang.biz/support |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.