Windows Threats Destroyer
Windows Threats Destroyer Image
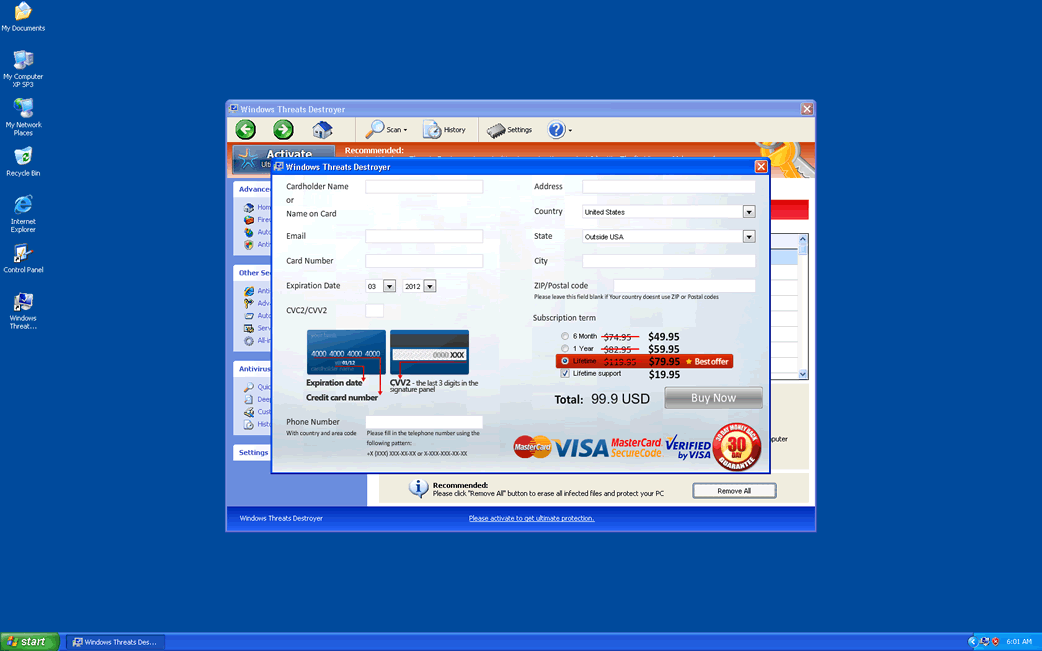
The awkwardly-named Windows Threats Destroyer is a fake security application from the FakeVimes family of rogue anti-virus programs. Basically, Windows Threats Destroyer is designed to imitate Microsoft Security Essentials superficially, acting as a supposed advanced version of Security Center. However, ESG malware analysts have detected that Windows Threats Destroyer has no way of removing or detecting malware. This is because Windows Threats Destroyer is a kind of malware infection itself. Windows Threats Destroyer or its clones will usually use deception in order to trick computer users into downloading Windows Threats Destroyer itself or a Trojan infection designed to deliver Windows Threats Destroyer. Once installed, Windows Threats Destroyer makes various threats, claiming that the victim's computer system is severely infected and that a 'full version' of Windows Threats Destroyer is needed to obtain 'ultimate protection' and remove these imaginary threats from the infected computer system.
The FakeVimes family of malware become a widespread problem due to the attacks of its many members. Clones of Windows Threats Destroyer include Virus Melt, Presto TuneUp, Fast Antivirus 2009, Extra Antivirus, Windows Security Suite, Smart Virus Eliminator, Packed.Generic.245, Volcano Security Suite, Windows Enterprise Suite, Enterprise Suite, Additional Guard, PC Live Guard, Live PC Care, Live Enterprise Suite, Security Antivirus, My Security Wall, CleanUp Antivirus, Smart Security, Windows Protection Suite, Windows Work Catalyst.
Table of Contents
How Windows Threats Destroyer Enters Your Computer System
Windows Threats Destroyer will usually enter a computer system with the aid of a Trojan infection. Like their name implies, Trojans (much like the Trojan Horse from the Iliad) will enter the victim's computer by pretending to be legitimate or useful files. Then, they release their payload, which in this case will usually be the Windows Threats Destroyer installer and various associated malware threats. Trojans associated with Windows Threats Destroyer tend to be disguised as video codecs or system updates on malicious websites. Another common source of Windows Threats Destroyer infection is online advertisements claiming to scan your PC for malware.
ESG security analysts strongly recommend that computer users avoid supposed scanners making these claims. Any anti-malware scan should be done with a reliable anti-malware program from a well-known, recommended manufacturer. By agreeing to these kinds of online scans, computer users are basically putting their computer system at the disposal of the criminals behind Windows Threats Destroyer. This can result in two things: first, the malicious scanner will attempt to install Windows Threats Destroyer by exploiting known vulnerabilities in the victim's computer system. Second, Windows Threats Destroyer will display a report claiming that the victim's computer is infected and that downloading Windows Threats Destroyer is needed to control this imaginary malware threat.
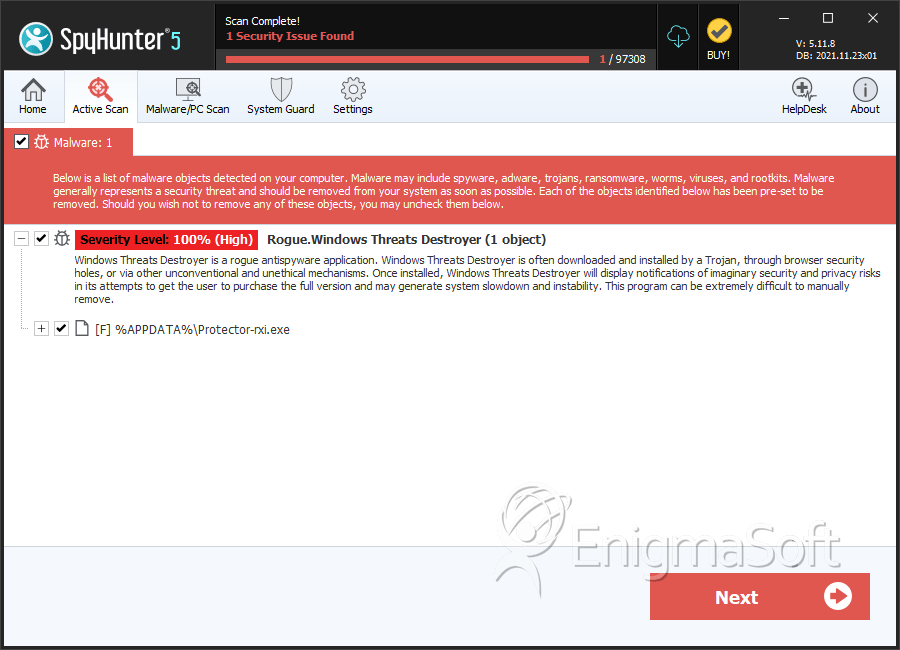
SpyHunter Detects & Remove Windows Threats Destroyer
Windows Threats Destroyer Video
Tip: Turn your sound ON and watch the video in Full Screen mode.

File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | %AppData%\NPSWF32.dll | ||
| 2. | %AppData%\Protector-[RANDOM CHARACTERS].exe | ||
| 3. | %AppData%\Microsoft\Internet Explorer\Quick Launch\Windows\Threats Destroyer.lnk | ||
| 4. | %StartMenu%\Windows Threats Destroyer.lnk | ||
| 5. | %Desktop%\Windows Threats Destroyer.lnk | ||
| 6. | %AppData%\result.db | ||
| 7. | Protector-rxi.exe | 89c3bd82bc57b2b7bdc4acd8b49b6b45 | 0 |

