Troj/VB-FPL
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 90 % (High) |
| Infected Computers: | 1 |
| First Seen: | October 11, 2011 |
| Last Seen: | April 23, 2020 |
| OS(es) Affected: | Windows |
The Troj/VB-FPL Trojan is a fairly typical Trojan infection that makes harmful changes to the Windows Registry and installs malicious software onto the infected computer. The Troj/VB-FPL Trojan, in particular, has been closely associated with several distinct strains of Adware. While this Trojan infection is thought to have been created in 2008, Troj/VB-FPL made headlines in 2011 when Troj/VB-FPL was used in a widespread spam email scam.
Table of Contents
The Troj/VB-FPL Trojan and the YesAsia.com Scam
YesAsia.com is a website dedicated to selling products, mainly music, electronics and videos to Asian audiences. It would be fair to compare it to Amazon, although aimed at consumers in Asian countries. Criminals have sent out a large quantity of spam emails containing a compressed attachment that, when opened, infects the victim's computer with the Troj/VB-FPL Trojan. These spam emails are designed to look like invoices from YesAsia.com. The victim will typically receive a fake invoice from YesAsia.com claiming that a specific item was bought. The email will instruct the victim to open the attached .zip for more details. ESG PC security researchers warn against opening this attachment, or any other unknown email attachments. When this .zip file is opened, it will actually infect the victim's computer system with the Troj/VB-FPL Trojan. This Trojan, in turn, may infect the victim's computer with Adware or allow a hacker to gain access to the infected operating system. Using the Troj/VB-FPL Trojan, a criminal can install a Remote Access Tool onto the infected computer. This can allow the criminal to control the infected computer system from afar, with the help of automated software. Using this kind of malware, the infected computer can, in turn, be used to send out additional spam email so that more victims become infected with the Troj/VB-FPL Trojan.
Avoiding a Troj/VB-FPL Trojan Infection
There are several steps you can take to avoid a Troj/VB-FPL Trojan infection. ESG PC security researchers strongly recommend using fully-updated security applications and a strong anti-spam filter for your email account. Having a real-time anti-virus scanner and a strong firewall can help prevent Trojan infections. However, the most important thing you can do to prevent a Troj/VB-FPL Trojan infection is simply to avoid opening suspicious emails and learning to identify the characteristics of a typical spam email. Most importantly, it is essential to avoid downloading email attachments from unexpected senders
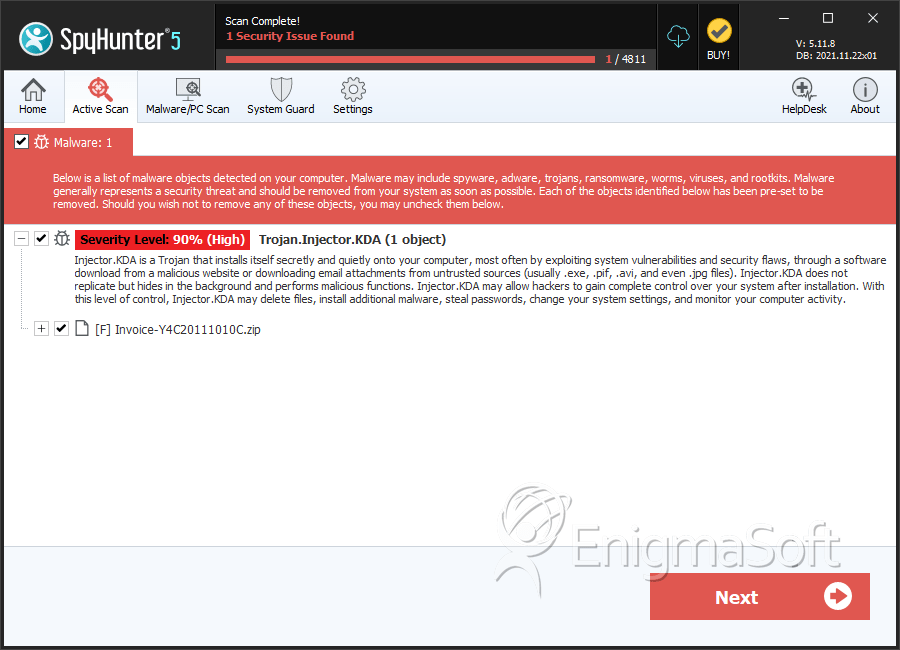
SpyHunter Detects & Remove Troj/VB-FPL
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. |
C:\Documents and Settings\ |
||
| 2. | Invoice-Y4C20111010C.zip | de24db11baedf78ea225bd24e02aec7f | 0 |
| 3. | Invoice-Y4C20111010C.zip | 32cd46571103505d4e8d3792c9940d0f | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.