Trojan.Spyeyes
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
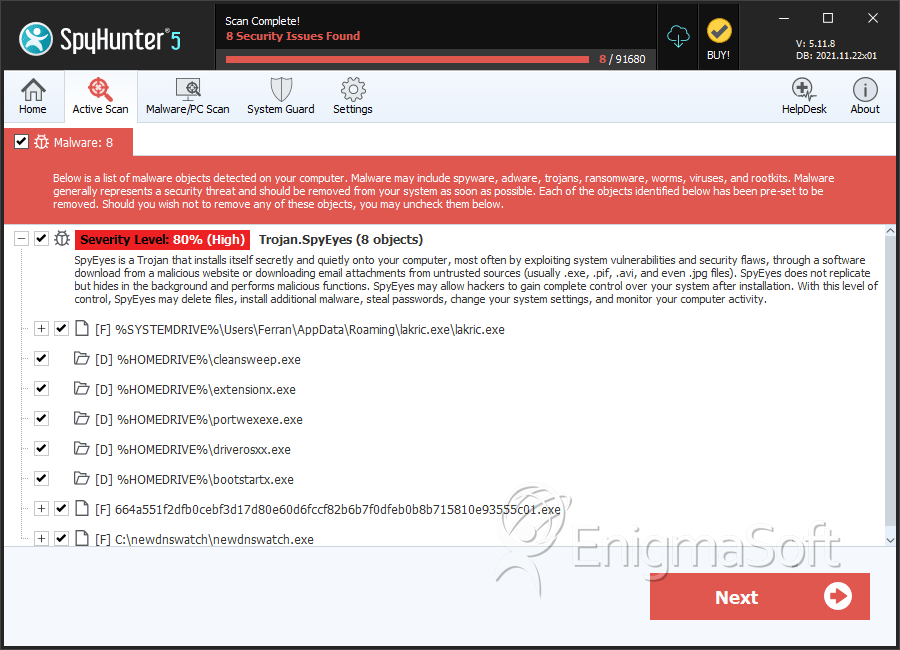
| Threat Level: | 80 % (High) |
| Infected Computers: | 510 |
| First Seen: | April 20, 2011 |
| Last Seen: | July 1, 2025 |
| OS(es) Affected: | Windows |
Trojan.Spyeyes is an especially dangerous piece of malware. This is one of those rare instances when a threat really is dangerous enough to do real harm to the user of an infected computer. Trojan.Spyeyes is designed to steal money from the users of infected computers and to control infected computers remotely, and Trojan.Spyeyes is designed to do it directly, by stealing personal information. What makes Trojan.Spyeyes an especially serious threat is that Trojan.Spyeyes can do all of its deeds, and you will not know about it – unless you have an anti-virus application that detects the infection.
Table of Contents
What is Trojan.Spyeyes?
Trojan.Spyeyes – more commonly referred to as Spyeyes – is a sophisticated program. Trojan.Spyeyes is written in a way that allows Trojan.Spyeyes to hide itself from the users of the computers that Trojan.Spyeyes infects, preventing Trojan.Spyeyes' Registry entries, files, and activities from being located or detected. For example, Spyeyes injects its code into your computer's running processes, so that Trojan.Spyeyes can run within them invisibly. Spyeyes also takes advantage of file compression and basic memory functions, by compressing Trojan.Spyeyes' files in a way that it can only be unlocked by a specific password – and that the password is hidden inside the machine's memory at the assembly level (within the stack), so that it can't be accessed later on its own. The person who created Spyeyes knew what he/she was doing, which is why Spyeyes does not cause any symptoms. So, you will not know that Spyeyes has infected your computer unless you use security program that knows to look for the Trojan, and detects the changes that the malware has made. Otherwise, Spyeyes can hang out on your PC indefinitely, stealing data and giving a remote user the ability to control your computer as part of a botnet.
Like the Zeus Trojan kit before it, Trojan.Spyeyes is a money-making venture for Trojan.Spyeyes' creator and for users of the malware. The Spyeyes software is sold (in the underground) for about $500, and for that the buyer receives what is essentially a Trojan builder. Spyeyes has a wide variety of configurable options, including which web browsers to attack, which countries to attack, which information to steal, and even what to call the main executable file that is called by the Windows Registry when Windows starts. (By default, it is called cleansweep.exe, but each individual Spyeyes user may name it whatever he or she wishes for each Spyeyes Trojan that is built. Therefore, the publicly-listed "aliases" for cleansweep.exe listed in some locations online are misleading, because they only refer to individual Spyeyes builds, by individual people, and not to any larger scheme or pattern.)
Although Spyeyes was originally only capable of attacking Internet Explorer and Firefox, Trojan.Spyeyes now targets Chrome and Opera as well, meaning that information accessed via those browsers can be stolen. Because Spyeyes captures keystrokes and saves them instantaneously, even information entered into a secure form or on a secure site can be stolen. In order to corner the market on malware that targets banking information, Spyeyes has also developed the idea to kill or remove any instances of the Zeus Trojan that Trojan.Spyeyes finds on infected PCs, as well as the ability to use the infected computer as part of a botnet, to launch denial-of-service attacks on Abuse.ch, a site that tracks and reports on Spyeyes botnets and other similar Trojan threats.
Where Does Trojan.Spyeyes Came From?
Spyeyes was first released in Russia in the fall of 2009, and infections began to be detected by major anti-virus companies in February 2010. Since then, Trojan.Spyeyes has become increasingly widespread. With the addition of the ability to attack more web browsers, as well as to attack Zeus and Abuse.ch, Trojan.Spyeyes became significantly more dangerous in January and February 2011. Since then, Spyeyes infections have become more common and problematic, with some financial institutions being hit hard by abuse of stolen banking information.
Keep in mind that Trojan.Spyeyes is, as Trojan.Spyeyes' name implies, a Trojan. Trojan.Spyeyes can't replicate itself, and Trojan.Spyeyes can't spread on its own. Trojan.Spyeyes is installed when you are tricked into installing Trojan.Spyeyes, one way or another. Most commonly, Trojan.Spyeyes is installed when you download a file from a pirating site or peer-to-peer service, or when you open or run a file that is attached to a spam email. In other words, it is easy to avoid getting Trojan.Spyeyes – far easier than it is to know that your computer has Trojan.Spyeyes, or to remove Trojan.Spyeyes.
SpyHunter Detects & Remove Trojan.Spyeyes
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | lakric.exe | 6c3a9fa758e6a7100736624d402ab538 | 39 |
| 2. | 664a551f2dfb0cebf3d17d80e60d6fccf82b6b7f0dfeb0b8b715810e93555c01.exe | 7779f923da8c1418764fecc7d1ba86cf | 1 |
| 3. | 861aa9c5ddcb5284e1ba4e5d7ebacfa297567c353446506ee4b4e39c84454b09.exe | 84714c100d2dfc88629531f6456b8276 | 1 |
| 4. | c1a600ed8fcf88685e19c299efe5154164e104d9bf57698221c72db9af012ca2.exe | ef24131db9e8ec83e551c0a8ba2b2f56 | 1 |
| 5. |
C:\Documents and Settings\ |
||
| 6. | newdnswatch.exe | 4ea38c25f53d82d9f79a2e3e47f88440 | 0 |
| 7. | 0b6a0aff13618e3d91f6c87456991222d642456db946bf32f94afc77dcd25609.exe | 9d2a48be1a553984a4fda1a88ed4f8ee | 0 |
| 8. | 38c6ba7df4823d50feef28842531a4bd8a28039e0d518bd3fe3efbcd4ccaa7b1.exe | d64ca15261c53279a7288616b3cb1a92 | 0 |
| 9. | 9459b0d6f7cdec6860c458944386896f78cb60befdd04fbeab0df5b6661a3f81.exe | 5942ba36cf732097479c51986eee91ed | 0 |
| 10. | 966ba7601becffb361a55f02d02fc129903d19be45e793946361383106f521da.exe | 2b8a408b56eaf3ce0198c9d1d8a75ec0 | 0 |
| 11. | a7b061a30f875be1de8994084f2935175ccb4edce87a88fc4430c63e0f738376.exe | 97c73a29ab07f04458f5e8834f8db1ba | 0 |
Registry Details
Directories
Trojan.Spyeyes may create the following directory or directories:
| %HOMEDRIVE%\bootstartx.exe |
| %HOMEDRIVE%\cleansweep.exe |
| %HOMEDRIVE%\driverosxx.exe |
| %HOMEDRIVE%\extensionx.exe |
| %HOMEDRIVE%\portwexexe.exe |
