Troj/Agent-YCW
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 90 % (High) |
| Infected Computers: | 1 |
| First Seen: | October 9, 2012 |
| Last Seen: | April 25, 2020 |
| OS(es) Affected: | Windows |
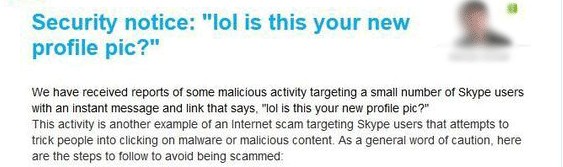
Troj/Agent-YCW Image
Troj/Agent-YCW is a dangerous Trojan infection that is associated with the Dorkbot botnet and a dangerous Skype scam that has claimed numerous victims around the world. ESG security researchers advise computer users to be extremely careful of scams on Skype, the popular VoIP application. Criminals have started to distribute dangerous Trojans (including Troj/Agent-YCW) through Skype by using messages similar to those used in other social media and instant messaging scams. If a computer becomes a victim of Troj/Agent-YCW, this Trojan will open a backdoor into the infected computer. Using this backdoor, criminals can gain control of the victim's computer in order to carry out attacks from a remote location. The infected computer is then integrated into the Dorkbot botnet, a vast network of infected computers that is used to carry out coordinated attacks on specific targets.
ESG malware analysts suspect that Troj/Agent-YCW is installed due to a worm infection that is designed to take over the victim's computer and then send out malicious messages using that computer's Skype account. These messages will typically read 'lol is this your new profile pic?' followed by a link which includes the victim's user name (which makes the attack much more effective than normal). Of course, clicking on this link downloads a compressed ZIP archive, with a name composed of the date and including the words 'Skype' and 'image'. Some examples of names for this malicious ZIP file include skype_06102012_image.zip and skype_08102012_image.zip. However, this ZIP file does not contain images. Rather, it contains executable files for a dangerous backdoor Trojan that ESG security researchers identify as Troj/Agent-YCW.
Once the victim opens the malicious ZIP file, Troj/Agent-YCW's executable file runs automatically and installs a backdoor on the victim's computer. It makes copies of itself on all drives connected to the infected computer and makes a malicious change to the Windows Registry that allows Troj/Agent-YCW to start up automatically upon start-up. These changes can be difficult to detect because Troj/Agent-YCW will register these changes as if they were part of Skype's registry entries. Once this is done, the infected computer is integrated into the Dorkbot botnet and may be used to distribute further copies of this malware threat, in addition to achieving other malicious tasks (such as DdoS attacks or sending out email and social media spam).
Table of Contents
File System Details
| # | File Name |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|
| 1. | %PROFILE%\Application Data\Jqfsfb.exe | |
| 2. | skype_08102012_image.zip | |
| 3. | skype_06102012_image.zip |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.