Spora Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 253 |
| First Seen: | January 11, 2017 |
| Last Seen: | February 27, 2023 |
| OS(es) Affected: | Windows |
The Spora Ransomware is a sophisticated ransomware Trojan that has an advanced payment site and the capacity to carry out its attacks online. The Spora Ransomware first appeared in January 2017 and caught the attention of PC security researchers immediately, because of its ability to carry out attacks online, a strong encryption engine, and a sophisticated ransomware payment site that is far more advanced than payment sites associated with other ransomware Trojans observed previously.
Table of Contents
How the Spora Ransomware may be Distributed
The Spora Ransomware may be distributed using spam email messages that trick computer users into believing that the email contains an invoice attachment. The attachment is a ZIP archive file that contains HTA files inside. These HTA files use a double extension, which causes computer users to believe that the file is a PDF or a DOC file. Opening this HTA file begins the process of installing the Spora Ransomware on the victim's computer. The HTA file extracts a JavaScript file named 'close.js' into the Temp directory on the targeted computer. This, in turn, extracts an executable file and runs it. The executable associated with the Spora Ransomware uses a randomly generated name and encrypts the victim's files. Apart from the executable, a corrupted DOCX file will also be extracted and executed. The file will show an error message deliberately, making the computer user believe that the file is a damaged invoice file that was not accessible, while the attack occurs in the background.
The Spora Ransomware can Work Even on an Off-Line Computer!
One aspect of the Spora Ransomware that sets it apart from many other ransomware Trojans is that it can work offline; the Spora Ransomware does not generate traffic to its Command and Control servers. The Spora Ransomware also does not target a large variety of files (unlike some Trojans that can encrypt up to one thousand different file types!). The Spora Ransomware limits its attack to the following files:
.xls, .doc, .xlsx, .docx, .rtf, .odt, .pdf, .psd, .dwg, .cdr, .cd, .mdb, .1cd, .dbf, .sqlite, .accdb, .jpg, .jpeg, .tiff, .zip, .rar, .7z, .backup.
The Spora Ransomware will encrypt files on all local drives and shared network drives. The Spora Ransomware leaves file names unchanged, not adding file extensions as other ransomware Trojans do. The Spora Ransomware avoids Windows system files and program directories, to ensure that the victims can still access their computers to pay the Spora Ransomware ransom.
The Spora Ransomware uses a solid encryption method. It is very unlikely that PC security researchers will release a decryption utility for the Spora Ransomware threat. The Spora Ransomware's encryption method is quite sophisticated, resulting in a .KEY file and an encryption key necessary for the decryption of the affected files. To decrypt the affected files, victims of the Spora Ransomware attack are asked to send the generated .KEY file to the people responsible for the attack. They can then use their own private key to retrieve the decryption key necessary to decrypt the victim's files.
Some Curiosities about the Spora Ransomware’s Payment Website
The Spora Ransomware's payment website is accessible through the Spora.bz publicly. However, this website is a gateway to a hidden TOR site that is not accessible to the public. At the time of writing, there are at least ten different URLs that have been associated with the Spora Ransomware. Victims of the Spora Ransomware attack can log into the decryption service by using an ID number delivered in the Spora Ransomware ransom note. Victims also have to upload the .KEY file created on their computers. Once this information has been synchronized, the victims of the Spora Ransomware attack have access to the following features:
'Decrypt files (currently $79)
Buy immunity from future the Spora infections (currently $50)
Remove all the Spora-related files after paying the ransom (currently $20)
Restore a file (currently $30)
Restore 2 files for free'
The layout of the Spora Ransomware payment website is quite sophisticated, more similar to an eCommerce website than to a ransomware payment website.
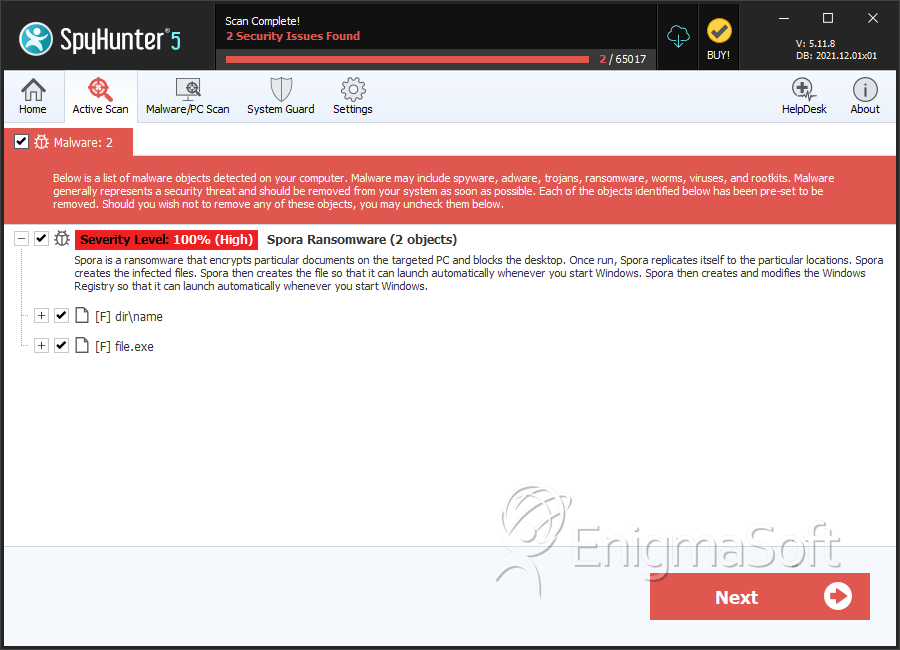
SpyHunter Detects & Remove Spora Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 312445d2cca1cf82406af567596b9d8c | 5 |
| 2. | name | 0817d2e6f614d618527acd25057e8819 | 0 |
| 3. | file.exe | 69b0c8f0308dd268dfc22af86dea87f1 | 0 |
| 4. | file.exe | 84396f618f3286277f1919d575ab4650 | 0 |
| 5. | file.exe | 0e8cb01c48f5fd141b1f8e83c60dd67e | 0 |

