SecureCryptor Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 5 |
| First Seen: | June 27, 2016 |
| Last Seen: | October 27, 2021 |
| OS(es) Affected: | Windows |
The SecureCryptor Ransomware is an encryption ransomware Trojan that carries out what has become a very well known type of attack. Essentially, the SecureCryptor Ransomware encrypts the victim's files, demanding the payment of a ransom in exchange for the decryption key. The SecureCryptor Ransomware has received its name because it adds the extension 'SECURECRYPTED' to the files that have been encrypted. It seems that the SecureCryptor Ransomware is a typical variant of these threats, carrying out an attack that has been observed countless times before in previous attacks. As with other ransomware Trojans, the best protection is to backup all files and use a reliable security application that is fully up-to-date to prevent the SecureCryptor Ransomware from entering the victim's computer in the first place.
Table of Contents
The SecureCryptor Ransomware Warns Its Victims About the Attack
Like other encryption ransomware Trojans, the SecureCryptor Ransomware enters the victim's computer and scans all the drives for files matching a list of file extensions contained in the SecureCryptor Ransomware's configuration files. Once it has completed its scan, the SecureCryptor Ransomware encrypts these files using an encryption algorithm, with the decryption key stored on its Command and Control server and out of reach of the computer user or the security software on the infected computer.
Every time the SecureCryptor Ransomware encrypts a file, it drops a copy of its ransom note on the victims' computer, alerting them of the attack. The SecureCryptor Ransomware's ransom notes follow an easily identifiable pattern that uses the file name, separated by a period from the string 'Contact_Here_To_Recover_Your_Files.' The SecureCryptor Ransomware ransom notes tend to take the form of text files with the extension 'TXT' and are dropped in every directory where files were encrypted by the SecureCryptor Ransomware. The following is a ransom message that has been associated with the SecureCryptor Ransomware's ransom notes:
'A L L Y O U R F I L E S A R E E N C R Y P T E D
All your data - documents, photos, videos, backups - everything is encrypted.
The only way to recover your files: contact us to the next email: recoveryhelp@bk.ru
Attach to e-mail:
1. Text with your IP server as Subject (To locate your encryption algoritm)
2. 1-2 encrypted files (please dont send files bigger than 1 MB)
We will check the encrypted file and send to you an email with your
Decrypted FILE as proof that we actually have the decrypter software.
Remember:
1. The FASTER you'll CONTACT US - the FASTER you will RECOVER your files.
2. We will ignore your e-mails without IP server number in Subject.
3. If you haven't received reply from us in 24 hours - try to contact us via public e-mail services such as Yahoo or so.'
Dealing with the SecureCryptor Ransomware
Although currently there is no decryption utility for the SecureCryptor Ransomware released by PC security analysts, PC security researchers suspect that it will be possible to create a decryption utility to help victims of this attack. Computer users can help PC security researchers by submitting copies of encrypted files with an unencrypted original, as well as copies of the ransomware executable to malware researchers. It is highly likely that a decryption utility for the SecureCryptor Ransomware will eventually be released since the encryption used does not seem to be particularly strong when compared to other, similar threats.
Computer users should have a reliable security program active at all times that is fully up to date to prevent the SecureCryptor Ransomware from entering a computer in the first place. To become fully invulnerable to the SecureCryptor Ransomware and similar attacks, PC security researchers recommend that computer users use a backup method of an off-site memory device. Having backups of all files will make this attack completely ineffective since the encrypted files can be easily recovered from the backup.
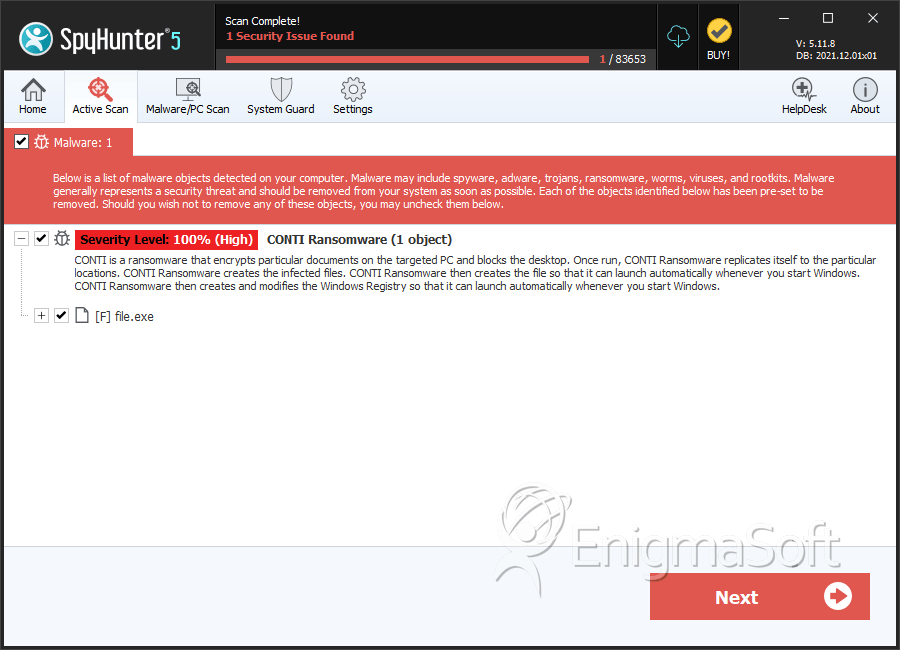
SpyHunter Detects & Remove SecureCryptor Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 196b1e6992650c003f550404f6b1109f | 1 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.