ProposalCrypt Ransomware
The ProposalCrypt Ransomware is a ransomware Trojan that is used to force computer users to pay a fee to recover their files, which the ProposalCrypt Ransomware takes hostage. The ProposalCrypt Ransomware carries out a typical ransomware attack, encrypting the victims' files to take them hostage. Victims will not be able to access the encrypted files and will need to pay the ProposalCrypt Ransomware ransom to obtain the necessary decryption utility or code. PC security researchers consider threats like the ProposalCrypt Ransomware as real dangers to the computer users' data and money. Therefore, by taking preemptive steps such as backing up all data and using a reliable security program that is fully up-to-date you can protect your data from encryption ransomware Trojans like the ProposalCrypt Ransomware.
Table of Contents
The Proposal Every Computer User Wants to Refuse
The ProposalCrypt Ransomware receives its name from the file that is being used to deliver this threat. The file, named 'proposal.doc_________.exe' uses a name that is designed to trick computer users into believing that it is a DOC file when it is an EXE executable file. This is a common way of hiding threatening file types by disguising them as more benign types of data. The distribution method and attack strategy that is used by the ProposalCrypt Ransomware is not different from most commonly used ransomware Trojans that are active currently. However, despite that the ProposalCrypt Ransomware is virtually identical to most commonly used ransomware Trojans, it does not make it any less threatening or difficult to deal with. It is important for computer users to take precautions to keep data safe from threats like the ProposalCrypt Ransomware.
How the ProposalCrypt Ransomware Carries out Its Attack
To encrypt the victim's files, the ProposalCrypt Ransomware uses an open source encryption algorithm. The ProposalCrypt Ransomware uses a customized AES-256 encryption algorithm that is publicly available currently. This encryption algorithm has important benign functions, since it helps companies and computer users keep their data safe. However, it also may be used for nefarious purposes, such as with encryption ransomware Trojans like the ProposalCrypt Ransomware. The ProposalCrypt Ransomware was submitted to the Google's VirusTotal platform, which is used to keep track of threats. It is possible that the ProposalCrypt Ransomware is still under development and the con artists responsible for the ProposalCrypt Ransomware may have submitted to the Google platform itself to find out if its code can bypass anti-virus programs and analysts currently.
The ProposalCrypt Ransomware attack is simple to understand. Once the ProposalCrypt Ransomware enters a computer, it searches for files with certain file extensions. The ProposalCrypt Ransomware tends to target media files, databases, office documents, eBooks, and numerous other potentially valuable files. The files that have been compromised by the ProposalCrypt Ransomware can be recognized easily because the extension '.crypted' will be added to the end of the file's name. Numerous other ransomware Trojans use the extension '.crypted' to identify the encrypted files, although this does not indicate a direct connection between the ProposalCrypt Ransomware with these other threats. New encryption ransomware Trojans will recycle and collect features and code from one another constantly, making it difficult to differentiate one ransomware threat from another.
Dealing with the ProposalCrypt Ransomware
The people responsible for the ProposalCrypt Ransomware demand payment of 1 BitCoin (approximately $850 USD at the current rate) in exchange for the decryption key. Fortunately, there is a decryption utility available publicly, meaning that computer users can recover from the ProposalCrypt Ransomware attack quickly without any need for payment. However, even if the decryption utility was not available, PC security researchers strongly advise computer users to avoid paying the ransom for these attacks. The people behind most encryption ransomware Trojans may ignore victims, increase the rate of the ransom after it has been paid, or deliver a non-functioning decryption program.
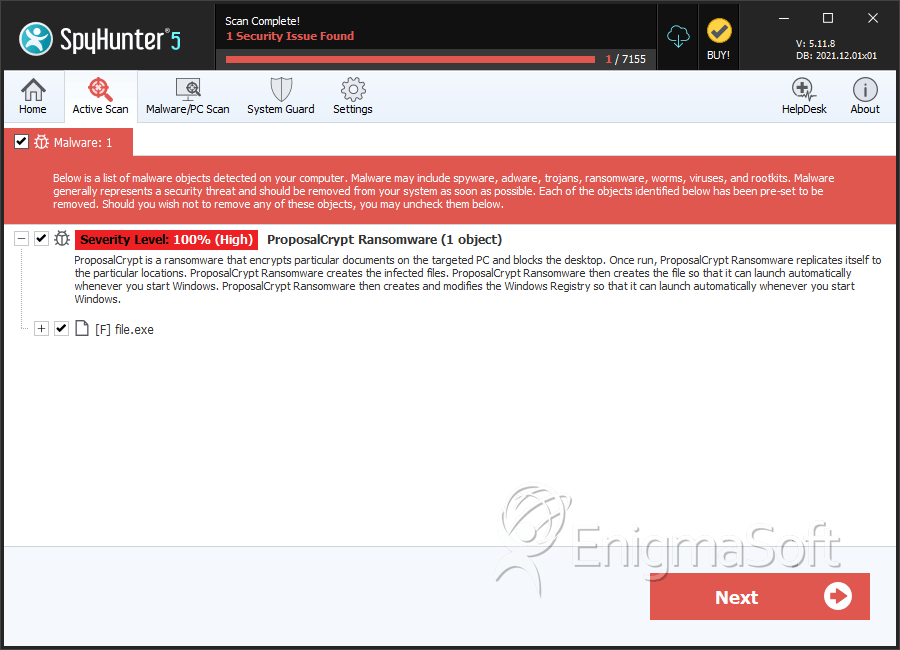
SpyHunter Detects & Remove ProposalCrypt Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | c471c1d03557e657777c4b5ce9f02cb7 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.