'.potato File Extension' Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 121 |
| First Seen: | January 26, 2017 |
| Last Seen: | July 3, 2020 |
| OS(es) Affected: | Windows |
The '.potato File Extension' Ransomware is a ransomware Trojan that also is known as the 'Potato Ransomware' because it marks the files that it affects with the extension '.potato.' The '.potato File Extension' Ransomware works by encrypting the victim's files, making them inaccessible. The files that have been encrypted by the '.potato File Extension' Ransomware will no longer be accessible. The victim is then asked to pay a substantial ransom to recover the files that were affected during the attack. Threats like the '.potato File Extension' Ransomware may be distributed using spam email messages, although malware analysts have received reports that the '.potato File Extension' Ransomware infections may be linked to a RAT (Remote Access Trojan) infections and installed on the victim's computer by the people responsible for the attack directly.
How the '.potato File Extension' Ransomware may Enter a Computer
There are many possible ways in which the '.potato File Extension' Ransomware could be installed on a computer, including direct installation, social engineering, or using exploits that take advantage of software vulnerabilities on the victim's computer. Once enters the victim's computer, it will make changes to the affected computer's Registry to ensure that the '.potato File Extension' Ransomware starts up whenever Windows starts up. The '.potato File Extension' Ransomware will then begin encrypting the victim's files, working in the background. Each file encrypted by the '.potato File Extension' Ransomware will be identified with the same file extension.
The '.potato File Extension' Ransomware's Ransom Note
After encrypting the victim's files, the '.potato File Extension' Ransomware will deliver a ransom note, which alerts the victim of the attack and includes instructions for paying a ransom to recover the files. The '.potato File Extension' Ransomware creates a folder named 'POTATO' on the victim's Desktop. This folder contains the following files:
'How to recover my files.txt
ID_number.txt
encrypted.txt
decryptor.exe
MSVCR100.dll'
The file 'How to recover my files.txt' contains the '.potato File Extension' Ransomware's main ransom note. The following is the full text of the '.potato File Extension' Ransomware's ransom note:
'YOUR FILES WERE ENCRYPTED
using military-grade encryption (AES-256). The encrypted files
have the additional extention .potato. You won't be able to retrieve your
data unless you make a payment by following the steps below:
1. Download the TOR browser
2. Access the following adress through TOR Browser for further instructions
http://tzakpakp6v5vwqqh.onion/
3. Enter your ID (see below) and hit 'GET KEY' for further instructions
NOTICE: There's a folder on your desktop named POTATO which
contains the following files:
ID_number.txt – an unique number that identifies your computer, which is mandatory for the payment process
encrypted.txt – a list of files that were encrypted; if you decide to have them back,
DO NOT DELETE IT
decryptor.exe (including MSVCR100.dll) – the program you'll use for decryption
once the payment is made and the decryption key is transmitted to you'
Dealing with the '.potato File Extension' Ransomware
PC security analysts strongly advise computer users against paying the '.potato File Extension' Ransomware ransom. There is no guarantee that the people responsible for this attack will keep their promise and restore the affected files. It is equally likely that the con artists will simply ignore the victim or even ask for more money. Even if the decryption key that they deliver does work, the ransom payment helps finance their activities and create more threats.
Unfortunately, the files encrypted by the '.potato File Extension' Ransomware cannot be recovered without the decryption key. Because of this, it is critical to take preemptive measures to minimize the damage caused by attacks like the '.potato File Extension' Ransomware. Malware researchers strongly advise computer users to backup all files on the cloud or an external memory device. File backups allow computer users to restore the affected files quickly, removing any need to pay the ransom. Apart from backups, you should have a reliable security program that is fully up-to-date to prevent the '.potato File Extension' Ransomware Trojan from entering the targeted computer.
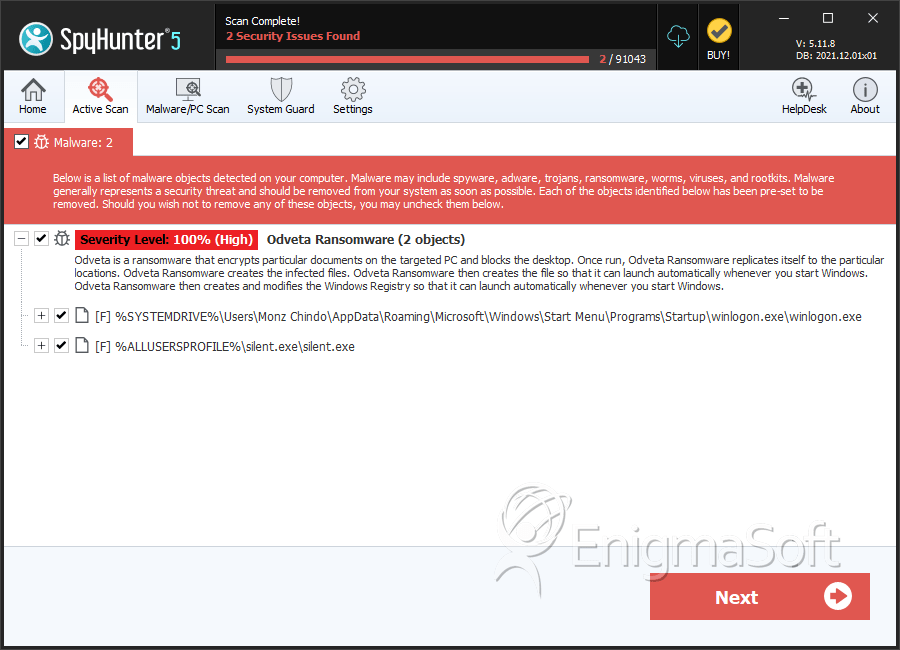
SpyHunter Detects & Remove '.potato File Extension' Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | winlogon.exe | 7d24e960023c7aefe6377e3cf5e7f996 | 80 |
| 2. | silent.exe | ad9f6e9022d4abe2447c21c7fc59bdba | 17 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.