Kuluoz
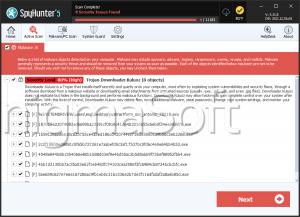
Kuluoz, or Win32/Kuluoz, is a family of malware that has been very active in the month of June, 2012. Malware in the Kuluoz family poses a severe threat to any infected computer system. Basically, Kuluoz is a Trojan infection that is planned to penetrate a computer and steal sensitive data, especially passwords. Kuluoz can delve into certain applications and sensitive files in order to retrieve password data. Kuluoz also has the ability to connect to a remote server and to download and install additional malware on the victim's computer system. Kuluoz Trojans will often install other variants in the same Kuluoz family as well as malware in the Sirefef family of rootkits. ESG security researchers have also observed that Kuluoz Trojans are often responsible for installing rogue security software in the WinWebSec and FakeSysdef families of malware.
Table of Contents
An Overview of the Kuluoz Family of Trojans
One of the most dangerous aspects of the Kuluoz family of malware is the fact that these Trojans will seldom display any symptoms. This makes Kuluoz infections more effective at stealing data and passwords, since computer users are unlikely to realize that their computer system is severely infected. Most of the time, the only symptoms of a Kuluoz infection is an alert from the infected system's anti-virus program. This is why ESG security researchers strongly advise keeping your security software fully up to date. Once installed, Kuluoz will target Microsoft office documents and files used to save passwords for most web browsers.
How Malware in the Kuluoz Family Enters a Computer
ESG malware analysts have associated Kuluoz family with a spam email campaign that will often carry Kuluoz as a malicious attachment. Most of the time, this attachment will be in the form of a compressed ZIP archive file. Spam email messages associated with Kuluoz will follow well-known social engineering techniques, such as pretending to be messages from courier services such as FedEx or various banks. When the victim opens the ZIP file attachment, it will run an executable file automatically that will be installed on your computer system. As part of its installation process, Kuluoz makes changes to the Windows Registry that makes possible for it Kuluoz to start up by its own nature and run in the background. Kuluoz Trojans use executable names that are very similar to legitimate Windows services and file processes, making it very difficult to distinguish them from legitimate Windows file processes in the Task Manager.
File System Details
| # | File Name |
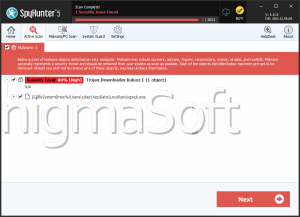
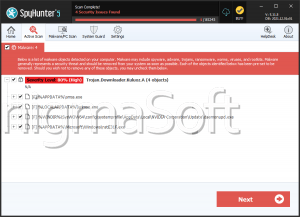
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|
| 1. | %LocalAppData%\pfranvvn.exe | |
| 2. | %LocalAppData%\[RANDOM CHARACTERS].exe |