Kronos Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
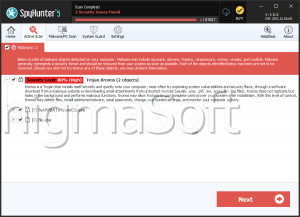
| Threat Level: | 100 % (High) |
| Infected Computers: | 2 |
| First Seen: | October 2, 2019 |
| Last Seen: | October 16, 2019 |
| OS(es) Affected: | Windows |
Recently, cybersecurity researchers have spotted a new ransomware threat. This brand-new file-locking Trojan is named Kronos Ransomware. After looking into it deeper, malware experts found striking similarities between this project and the already known Zeropadypt Ransomware. This made the researchers believe that it is likely the same actors are responsible for both data-encrypting Trojans. However, they have not yet been capable of cracking either one of them so that there are no free, publicly available decryption tools yet. However, if you have become a victim of the Kronos Ransomware, we encourage you to keep checking daily for a decryption tool.
The Distribution of the Kronos Ransomware
Researchers are not aware of the exact propagation methods employed in the spreading of the Kronos Ransomware. Some speculate that the ill-natured actors behind the Kronos Ransomware may have used bogus software updates, fake pirated copies of popular applications, and mass spam email campaigns to propagate their threatening creation. Once the Kronos Ransomware succeeds in compromising one’s system, it will perform a brief scan. When the scan is finished, all data of interest will be located. Then, the Kronos Ransomware will proceed the attack by starting its encryption process. All the newly locked files will have their names altered. This threat adds a ‘.email=[jacdecr@tuta.io]ID=[< VICTIM ID>].KRONOS’ extension to the affected files.
When the encryption process is through, the Kronos Ransomware will drop a ransom note. The note’s name is ‘HowToDecrypt.txt.’ In the ransom message, the creators of the Kronos Ransomware insist that the user contacts them via email. They have provided an email address where the victim is meant to get in touch with them – ‘jacdecr@tuta.io.’ The attackers demand the ransom fee to be paid in the shape of Bitcoin, which is a standard demand having in mind that cryptocurrency helps cyber crooks protect their anonymity.
The Removal of the Kronos Ransomware
You should ignore the demands of cybercriminals like the ones responsible for the Kronos Ransomware. Such sketchy individuals are not to be trusted. Instead, you should look into obtaining a legitimate anti-malware application, which will help you remove the Kronos Ransomware safely from your system.