JAVA_JACKSBOT.A
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
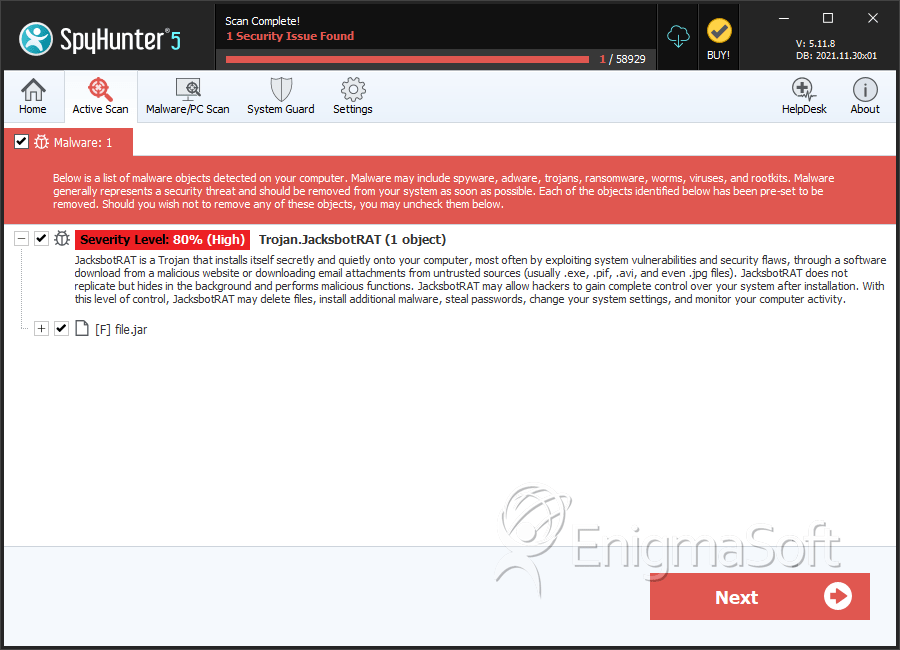
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 14 |
| First Seen: | November 1, 2012 |
| Last Seen: | January 13, 2021 |
| OS(es) Affected: | Windows |
JAVA_JACKSBOT.A is a dangerous JavaScript backdoor Trojan with plenty of nasty components that have caught the attention of PC security researchers. Although, initially, JAVA_JACKSBOT.A was thought to be a relatively low risk malware infection, ESG security researchers have observed that the JAVA_JACKSBOT.A infection is starting to becoming more widespread than initially thought and that JAVA_JACKSBOT.A has some components that were not apparent at first. This is considerably more alarming when one considers that the JAVA_JACKSBOT.A Trojan is a cross-platform malware infection, meaning that JAVA_JACKSBOT.A can affect computers with diverse operating systems such as Mac OS X and the various versions of Windows. This is due to the fact that the Java RunTime Environment is used in several different operating systems and that the JAVA_JACKSBOT.A is created to exploit several versions of Java.
The JAVA_JACKSBOT.A Trojan belongs to the JACKSBOT family of Trojan infections, usually infecting a computer in the form of a Java application. Since no actual infections in the wild had been detected by ESG security researchers, JAVA_JACKSBOT.A was initially considered to be a low risk threat Neverthtless, ESG malware analysts have noted that the JAVA_JACKSBOT.A infection is starting to appear in the wild after infections by Malaysia and Australia. This means that there is reason to believe that the JAVA_JACKSBOT.A infection is not being distributed and is spreading via social engineering tactics.
Table of Contents
How JAVA_JACKSBOT.A is Used to Attack a Computer
The JAVA_JACKSBOT.A Trojan is distributed as a mod for the popular computer game Minecraft (a sandbox environment that computer users can use to build impressive virtual worlds and structures). In fact, one of the most curious aspects of the JAVA_JACKSBOT.A infection is that JAVA_JACKSBOT.A responds to the command 'MC' which can be used to steal Minecraft passwords. One of the most worrying aspects of JAVA_JACKSBOT.A is its RAT component (Remote Access Trojan). Once JAVA_JACKSBOT.A has infected a computer, criminals can issue commands that allow JAVA_JACKSBOT.A to carry out several malicious tasks on the infected computer. Some of these malicious tasks include displaying messages on the infected computer, corrupting files, deleting files, stealing files, taking screenshots, shutting down processes, listing file processes, causing the infected computer's web browser to connect to a specific website and restart or shut down the infected computer. Most importantly, JAVA_JACKSBOT.A can track keystrokes and mouse movements and send this information to a remote party, making JAVA_JACKSBOT.A an effective tool for spying and stealing sensitive information.
SpyHunter Detects & Remove JAVA_JACKSBOT.A
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.jar | 0c19e3d68c08d4bf547db0f003295c84 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.