IXESHE
ESG security researchers have observed a marked raise of highly targeted malware attacks on specific individuals, governments and organizations. While traditional malware attacks are designed to attack millions of computers, Advanced Persistent Threats, are often highly targeted and are at times even state-sponsored or linked to specific groups looking to further their own agenda. A particularly persistent group of these kinds of attackers is known as IXESHE due to the detection for the malware that they use. IXESHE has been known to target a German telecommunications company and governments located in Eastern Asia. Typically, an IXESHE attack will use malicious email messages that are targeted towards the attacked group. These email messages will contain attached PDF files that take advantage of various exploits in order to install malicious executable files on the victim's computer system. ESGsecurity researchers have linked IXESHE attacks to two malicious email campaigns that took advantage of zero-day exploits in Adobe Systems software; one of these took place in 2009 and the other in 2011.
Table of Contents
IXESHE and Command and Control Servers
IXESHE attacks will typically use command and control servers that, sometimes, may be hosted on the victim's own networks. Through this method, criminals behind IXESHE were at one time able to take over at least sixty servers for use as malware command and control servers. This specific approach also gives criminals the advantage of being able to thwart PC security analysts due to the fact that their command and control servers will be hosted in the victim's own networks. IXESHE attacks are very adept at covering their tracks, and the source of the attacks is often quite difficult to detect.
Known Targets of IXESHE Attacks
IXESHE malware attacks are designed to spy on the infected computer system, gathering data without the victim's knowledge. ESG security researches have been able to determine three distinct victims for IXESHE attacks since 2009:
– An important telecommunications firm based in Germany
– Various electronics manufacturers located in Taiwan
– Governments of East Asian nations
Due to the fact that IXESHE malware tends to remain hidden in order to gather data without being detected, it is probable that many victims are not aware that they have become infected. As soon as a probable victim is identified, PC security researchers will contact them to warn them of the fact. ESG security analysts suspect that IXESHE attacks have been active at least since July of 2009.
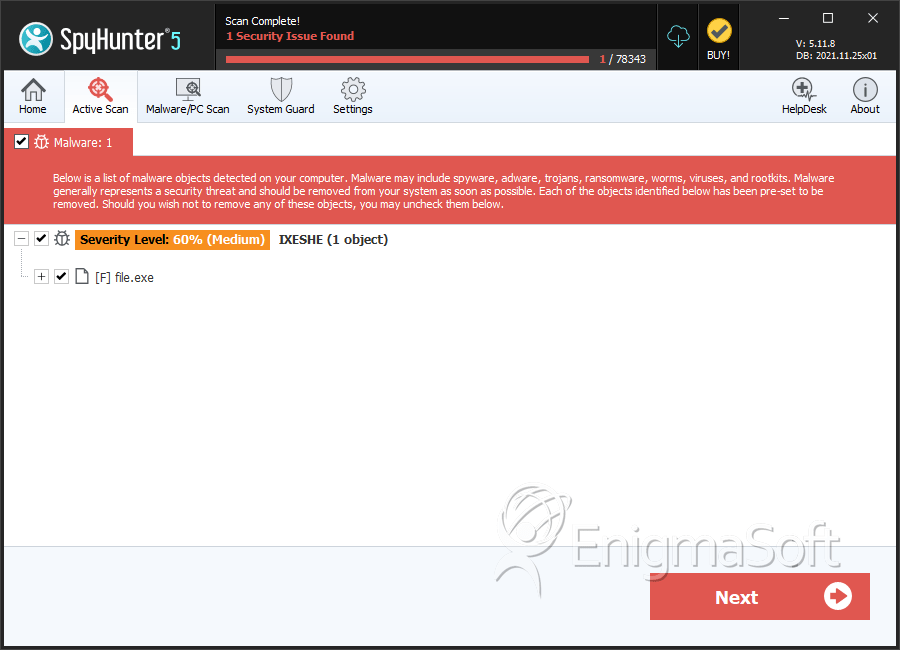
SpyHunter Detects & Remove IXESHE
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | d1fd08826fc243d8cf98ae628383ae4d | 0 |
| 2. | file.exe | c5ca2ab869c1ec1eb4afc04f410b40fd | 0 |
| 3. | file.exe | 1877fc47280a7990d08f7d6e9ac515de | 0 |
| 4. | file.exe | f2df77bd695d3e81eea7d176581badc3 | 0 |
| 5. | file.exe | 989a05d16f9bfaa6f06cc7d79b7d26f2 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.