FakeScanti
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 2,836 |
| First Seen: | November 30, 2010 |
| Last Seen: | January 10, 2022 |
| OS(es) Affected: | Windows |
The Trojan:Win32/FakeScanti's family of rogue anti-spyware programs is an especially numerous family, which has been present online since at least 2010. Like on most rogue anti-spyware applications, the malware in the Trojan:Win32/FakeScanti family will claim that the infected computer is severely infected. The malware will do this, in an attempt to convince its victim to purchase a license or a "full version" for a useless fake security application. ESG security researchers recommend ignoring all claims from rogue anti-spyware programs from the Trojan:Win32/FakeScanti family; none of the supposed security programs associated with the Trojan:Win32/FakeScanti have real anti-spyware capabilities. Some examples of malware belonging to the Trojan:Win32/FakeScanti family include AV Protection 2012, AV Protection 2011, Cloud AV 2012, Security Guard 2012, Wolfram Antivirus, OpenCloud Security, OpenCloud AV, Milestone Antivirus and Your PC Protector. Rather than fixing your computer system, FakeScanti-related rogue anti-spyware programs will actually negatively impact your system's performance, deliberately cause a number of problems and pester you with a constant stream of fake security alerts and alarming error messages. Inexperienced computer users may be taken in by Trojan:Win32/FakeScanti's use of legitimate Microsoft logos or superficially-impressive user interfaces. However, ESG security researchers strongly recommend removing any malware associated with Trojan:Win32/FakeScanti immediately.
Table of Contents
Main Effects of Trojan:Win32/FakeScanti
Rogue anti-spyware programs in the Trojan:Win32/FakeScanti family will make harmful changes to your operating system's settings. They will usually also create new files in your Windows or System folder. Examples of these include svchasts.exe and desot.exe. Trojan:Win32/FakeScanti will also alter the Windows registry so that rogue anti-spyware programs will be allowed to start up automatically when Windows is launched, stop and start file processes and block certain programs or access to the Internet. When installed, a rogue anti-spyware program will also create a shortcut icon on the infected computer's desktop and add an entry to the Windows Start Menu.
Understanding the Trojan:Win32/FakeScanti Scam
The Trojan:Win32/FakeScanti scam is typical of most rogue anti-spyware programs. However, rogue anti-spyware programs related to Trojan:Win32/FakeScanti are characterized by having very convincing interfaces and error messages. While most rogue security applications tend to be poorly written and can be quickly discerned by their bad grammar and spelling, rogue anti-spyware programs are highly professional in appearance and can trick their victims into purchasing these useless programs. Because of this, ESG malware analysts recommend being extremely wary of any unexpected pop-up messages or error messages that show up while browsing the Internet, especially if they are prompting you to download or purchase a security application or to run a free scan of your computer system. This is usually the first step in a dangerous malware infection.
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| AntiVir | TR/Fake.Scanti.626 |
| Kaspersky | Backdoor.Win32.Gbot.qmq |
| CAT-QuickHeal | Backdoor.Gbot.qmq |
| BitDefender | Gen:Heur.Conjar.9 |
| Kaspersky | Trojan-PSW.Win32.Fareit.lc |
| AVG | Generic26.GYK |
| Kaspersky | Trojan-FakeAV.Win32.OpenCloud.ca |
| CAT-QuickHeal | TrojanFakeAV.OpenCloud.ca |
| AVG | Generic26.DBG |
| Fortinet | W32/Sirefef.11L711!tr |
| AVG | Generic25.BVGI |
| McAfee-GW-Edition | Artemis!04E7ECC7F7AC |
| AntiVir | TR/PSW.Fareit.40 |
| Kaspersky | Trojan.Win32.Jorik.Gbot.rlh |
| Avast | Win32:Rootkit-gen [Rtk] |
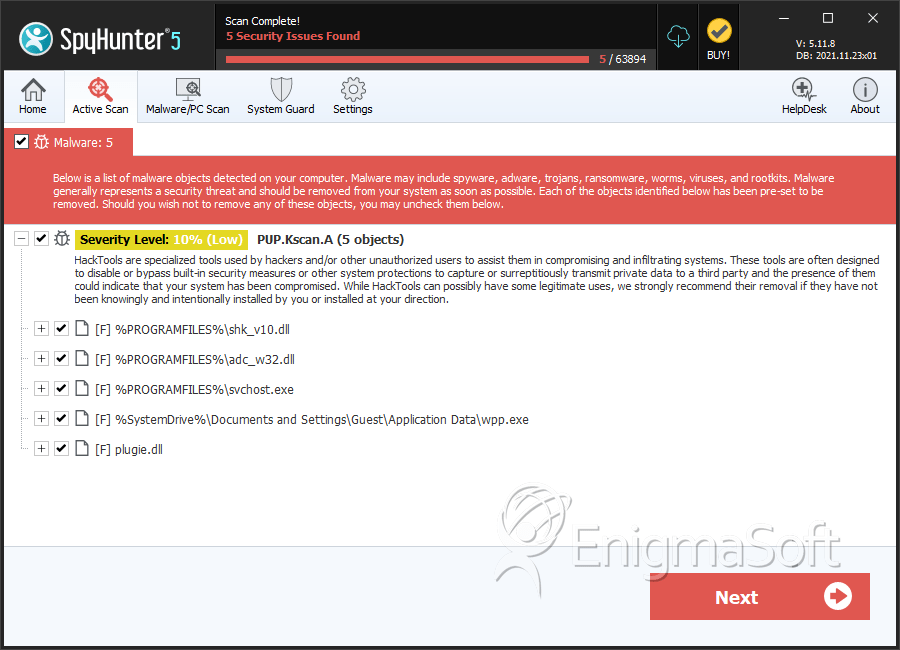
SpyHunter Detects & Remove FakeScanti
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | java.exe | b5ac23200df9524102f1f04de2ceba4f | 67 |
| 2. | java.exe | 49cc9036a42eca3abda63ea64c5f751d | 34 |
| 3. | java.exe | 22dd77527a0698b1a3edc5cea7d01efc | 34 |
| 4. | java.exe | 72bea5fbec7981da9ea61a9d16152299 | 22 |
| 5. | java.exe | 20f5fb0b21a127ea1a5c91c9c638469d | 20 |
| 6. | java.exe | c9a078fbb9f5e1df927f8de43fedc250 | 16 |
| 7. | java.exe | c21763e31fb15162feb65e78612e0b23 | 14 |
| 8. | java.exe | db713dcd6bfcd61476d4a7584bf75a76 | 12 |
| 9. | iexplore.exe | 057481cd2a00cb223ed1de0e6620d49f | 10 |
| 10. | Cloud AV 2012v121.exe | 41096615e6206b00f9206caf5307ba6a | 10 |
| 11. | iexplore.exe | 583700a254cfd66ad644b7da67df534b | 8 |
| 12. | java.exe | 1eb3390d1fc4a26a92b8b8b89a2b3e1e | 8 |
| 13. | java.exe | d03b6003e2780a216316843cf6952b4e | 7 |
| 14. | Cloud AV 2012v121.exe | 11fd80a3de0c4461f96d966d935005b5 | 6 |
| 15. | firefox.exe | dc4572c236c6eab67c4ddcedbe38ba8b | 5 |
| 16. | Cloud AV 2012v121.exe | b7f4641a84a3ba51b01c1386d440d443 | 5 |
| 17. | iexplore.exe | 670d36e7d3ae3d08c48a602ab4a72406 | 4 |
| 18. | Cloud AV 2012v121.exe | 644a649c104f47d63b0f87ee7296024b | 4 |
| 19. | firefox.exe | 792eef348cacb5cdc974cfd60f142533 | 3 |
| 20. | iexplore.exe | ccf74c83faaab41fea45ed735b914565 | 2 |
| 21. | firefox.exe | bb79fa479e3d4273e84c42985a8edb9f | 2 |
| 22. | tvq.exe | e5b10e4f60bc6005191d0ea509daaa2a | 2 |
| 23. | firefox.exe | 6c527aa9b17ff8405e52a44465176620 | 1 |
| 24. | chrome.exe | 8c348da2e1cb2660a9b003959fddd879 | 1 |
| 25. | atm.exe | f126ed56bc868c1a941e9e016bc731ab | 1 |
| 26. | firefox.exe | 12c269bc2b30d0a54bee59de6aba861a | 1 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.