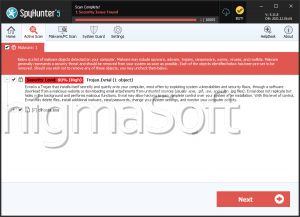
Evrial Trojan
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 3,362 |
| Threat Level: | 20 % (Normal) |
| Infected Computers: | 129 |
| First Seen: | August 16, 2023 |
| Last Seen: | September 21, 2023 |
| OS(es) Affected: | Windows |
The Evrial Trojan is a threat that was developed by a hacker known as 'qutra.' The Evrial Trojan is part of a campaign that is being advertised on forums on the Dark Web. PC security researchers observed ads for the Evrial Trojan selling this threat platform for approximately 30 USD in Rubles (the Evrial Trojan is being advertised to Russian hackers). The Evrial Trojan is an information collecting Trojan, based on the Ovidiy Stealer. The Evrial Trojan's developers offer third parties access to the Evrial Trojan's services after they purchase these services using Bitcoin. The Evrial Trojan's most important feature is its ability to modify clipboard content in a way that is more effective than most similar ransomware Trojans, and this allows the con artists to extract data from the affected computer and communicate with the Evrial Trojan quite effectively through the Web.
Table of Contents
Why the Evrial Trojan Infects a Computer
The people that purchase access to the Evrial Trojan project receive a building kit that allows them to build a custom version of the Evrial Trojan for their own use. They can use a variety of ways to then distribute the Evrial Trojan, such as spam email messages or by hacking into the targeted computer directly. After the people operating the Evrial Trojan manage to sneak this threat on to the victim's computer, this Trojan will be installed and modify the Windows Registry to ensure that it runs automatically when Windows starts up. The Evrial Trojan's purpose is to collect data from the infected computer. The Evrial Trojan does this in a variety of ways, which include the following:
- The Evrial Trojan can be used to gather files from the victim's computer and transfer them to the cybercrooks' servers.
- The Evrial Trojan can be used to take screenshots of the infected computer.
- The Evrial Trojan can be used to collect login and password information from various applications, which may include the most commonly used Web browsers, as well as FTP software or instant messaging software on the infected computer.
The Evrial Trojan’s Clipboard Modification Feature
The Evrial Trojan will monitor the content that is copied to the infected computer's clipboard, scanning it for strings that may be linked to information such as online login information or online banking. When the Evrial Trojan detects one of these strings, the Evrial Trojan connects to a Web panel that is used to control it remotely. The Evrial Trojan will make various changes to the data, for example replacing a cryptocurrency wallet address with another (typically involving long strings that are unlikely to be memorized or copied by hand, but rather transferred to the clipboard). The victim will then, without being aware, transfer money to the cybercrooks' wallet or carry out another operation that benefits its controllers. The Evrial Trojan will target numerous money transfer methods, cryptocurrencies, and even the Steam trade with this tactic. The cybercrooks can modify the rules for clipboard modification to make it work to their needs specifically, making the Evrial Trojan particularly effective at this specific tactic.
Protecting Your Computer from Threats Like the Evrial Trojan
The Evrial Trojan can be difficult to detect, and the differences in how the affected computers work are not very apparent. The Evrial Trojan will run as an executable file named '2lexf3zueyw.exe' in many cases. The Evrial Trojan will run in the background, and it may be associated with a rootkit component or other component designed to make it difficult to detect and remove the Evrial Trojan. The best protection against threats like the Evrial Trojan is a security program that is fully up-to-date to protect your data. Apart from this, computer users should use reasonable security measures to protect their computers from the main distribution vectors associated with threats like the Evrial Trojan, such as spam email messages or direct installation through compromised Remote Desktop Protocol connections.
URLs
Evrial Trojan may call the following URLs:
| datlngllfe.net |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.