BUYUNLOCKCODE
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 3 |
| First Seen: | January 6, 2015 |
| OS(es) Affected: | Windows |
BUYUNLOCKCODE is a ransomware Trojan that encrypts the victim's files and then requires a payment in order to decrypt the affected files. Currently, there is no standard payment amount. This is because BUYUNLOCKCODE forces computer users to contact BUYUNLOCKCODE's creators via email in order to receive payment instructions. The ransom amount may be different depending on the client. For example, an individual may be required to pay $500 USD while the fee for an affected corporate victim may be several thousand dollars. There have been several disposable emails associated with BUYUNLOCKCODE, including Sin.Jun@tom.com, nick.jameson@expressmail.dk and ChiuKhan@tom.com as well as many more.
Table of Contents
How BUYUNLOCKCODE Attacks a Computer User
The reason why BUYUNLOCKCODE receives its name is because after BUYUNLOCKCODE infects the victim's computer, BUYUNLOCKCODE encrypts the files on the affected hard drive (that may include documents, pictures, videos and similar types of files) and then creates a file on the victim's desktop named BUYUNLOCKCODE.txt. This ransomware Trojan will also replace the victim's desktop wallpaper with BUYUNLOCKCODE's instructions on receiving a decrypting utility. This image takes the form of a black background with the BUYUNLOCKCODE text. BUYUNLOCKCODE uses RSA-1024 encryption algorithm which requires a unique code for decryption. BUYUNLOCKCODE does not delete Shadow Volume copies, meaning that may exist a way to restore some of the affected files after removing the BUYUNLOCKCODE Trojan from the affected computer using utilities like Previous Versions or Shadow Explorer.
The BUYUNLOCKCODE text file has the following text:
'Hi, your ID = XXXXX
All important files were encoded with RSA-1024 encryption algorithm.
There is the only way to restore them - purchase the unique unlock code.
Warning! Any attempt to recovering files without our "Special program" will cause data damage or complete data loss.
As we receive your payment, we will send special program and your unique code to unlock your system.
Guarantee: You can send one of the encrypted file by email and we decode it for free as proof of our abilities.
No sense to contact the police. Your payment must be made to the e-wallet. It's impossible to trace.
Don't waste your and our time.
So, if you are ready to pay for recovering your files, please reply this email Sin.Jun@tom.com
Then we will send payment instructions.'
Dealing with BUYUNLOCKCODE Ransomware
If your files have been encrypted using BUYUNLOCKCODE, PC security researchers strongly advise remaining calm and never paying money for the unlock code unless the encrypted files were essential. However, with files so important, computer users should make it a policy to use offsite backups to reinstall them in the event of a catastrophe. Paying BUYUNLOCKCODE's ransom will only allow the creators of BUYUNLOCKCODE to continue carrying out their strategy, affecting numerous other computer users.
Computer users should attempt to use Shadow Volume restoration tools to recover at least some of the files. However, a reliable, fully updated security application should first be used to ensure that no traces of BUYUNLOCKCODE and its associated threats remain on the infected computer. Using these types of tools may help recover some of the encrypted content. Paying the BUYUNLOCKCODE asked fee will not guarantee that the persons responsible for this attack will allow you to recover your files. The best path in these situations is not to allow them to win. In case of a BUYUNLOCKCODE infection or an attack with a similar threat you should:
- Always make sure that all of your important files are backed up on an offsite location, such as a separate machine or on the cloud.
- Protect your computer with a fully updated security program and run regular scans of your computer.
- Avoid unknown or untrustworthy online content to prevent infection with Trojans and other threats associated with BUYUNLOCKCODE and other file encryptors.
Aliases
11 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| AVG | Win32/DH{gQwPAxNk} |
| Ikarus | Trojan.Win32.Filecoder |
| McAfee | Artemis!31D50DE977A0 |
| Antiy-AVL | Trojan[:HEUR]/Win32.AGeneric |
| Sophos | Mal/Generic-S |
| McAfee-GW-Edition | BehavesLike.Win32.SpywareLyndra.fh |
| DrWeb | Trojan.Siggen6.27667 |
| Comodo | TrojWare.Win32.TrojanDownloader.Delf.~TZ |
| Kaspersky | HEUR:Trojan.Win32.Generic |
| Avast | Win32:Malware-gen |
| Symantec | Trojan.Cryptolocker.E |
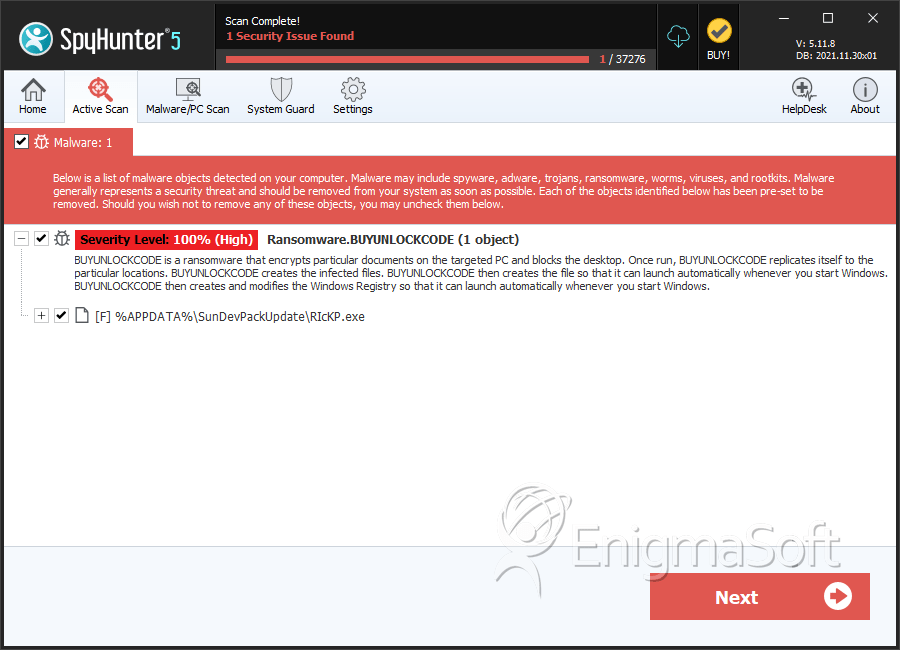
SpyHunter Detects & Remove BUYUNLOCKCODE
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | RIcKP.exe | 31d50de977a0c214f0c35ac769c399ad | 3 |
| 2. | BUYUNLOCKCODE.txt |