BTCWare-PayDay Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 10 |
| First Seen: | October 8, 2017 |
| Last Seen: | December 30, 2019 |
| OS(es) Affected: | Windows |
The BTCWare-PayDay Ransomware is an encryption ransomware that is used to extort computer users. Like most encryption ransomware Trojans, the BTCWare-PayDay Ransomware is designed to threaten computer users, making their files unreachable and then demanding the payment of a ransom to release the victim's files. To take the victim's files hostage, the BTCWare-PayDay Ransomware uses a strong encryption algorithm to make the files inaccessible and then displays a ransom note demanding that the victim pay a large ransom using Bitcoins in exchange for the decryption key that is necessary to regain access to the infected files. This tactic has been observed by PC security researchers countless times before and is today a common device used to force computer users to make large ransom payments.
Table of Contents
It can be a PayDay, but not for You
The BTCWare-PayDay Ransomware was first observed carrying out attacks on October 3, 2017. In the BTCWare-PayDay Ransomware attack, the encrypted files will be marked with a new file extension. The BTCWare-PayDay Ransomware will indicate that it has encrypted a file by adding the string '.[]-id-.payday' to each affected file's name. The BTCWare-PayDay Ransomware belongs to a family of ransomware that is derived from BTCWare, a ransomware Trojan that first appeared in April 2017. There are several variants of the BTCWare-PayDay Ransomware being released since April, most of them using very similar source code and carrying out attacks on victims, which are identical practically. Like other BTCWare variants, the BTCWare-PayDay Ransomware will communicate with its Command and Control servers using TOR for anonymity and has few, if any, identifying features that would differentiate it from other commonly seen ransomware Trojans.
The Consequences of a BTCWare-PayDay Ransomware Attack
The BTCWare-PayDay Ransomware is nearly identical to the Blocking Ransomware and the Wyvern Ransomware, both variants of BTCWare that have also been uncovered in 2017. The BTCWare-PayDay Ransomware, like other encryption ransomware Trojans, will target the user-generated files, typically attacking image files, text files, presentation files, audio, videos, etc. The BTCWare-PayDay Ransomware uses a strong encryption algorithm to make the victim's files inaccessible. Once the BTCWare-PayDay Ransomware has encrypted a file, its contents become inaccessible, and the victims will no longer be able to open the affected file or view its contents. The bulk of the BTCWare-PayDay Ransomware attacks seem to target victims in Western Europe. However, this does not mean that the BTCWare-PayDay Ransomware is geographically limited, and there is nothing stopping the BTCWare-PayDay Ransomware attacks from popping up in other parts of the world. It is likely that new variants of the BTCWare-PayDay Ransomware will appear, using different file extensions to mark the files, as well as different email accounts for victims to contact the attackers.
The BTCWare-PayDay Ransomware’s Ransom Demand
The BTCWare-PayDay Ransomware delivers a ransom note after encrypting the victim's files. This ransom note is named '!! RETURN FILES !!.txt' and is opened by the victim's default text editor. Below is the full text of the BTCWare-PayDay Ransomware ransom note:
'all your files have been encrypted
want return files?
write on email: keyforyou@tuta.io'
The BTCWare-PayDay Ransomware also will delete the Shadow Volume Copies and other recovery methods that could help computer users recover their files as part of its attack. This is why it is paramount to take preventive measures to ensure that the BTCWare-PayDay Ransomware cannot carry out its attack and the restoration of the files can be accomplished easily. Paying the BTCWare-PayDay Ransomware ransom is not a good option. Most of these threats demand a ransom of thousands of dollars, and the people responsible for the attacks seldom will keep their word and help the computer users restore their data after it has been compromised. The best protection against the BTCWare-PayDay Ransomware and similar threats is to have file backups on the cloud or another safe place. File backups give the computer users the choice of resto their files quickly without having to resort to paying the ransom.
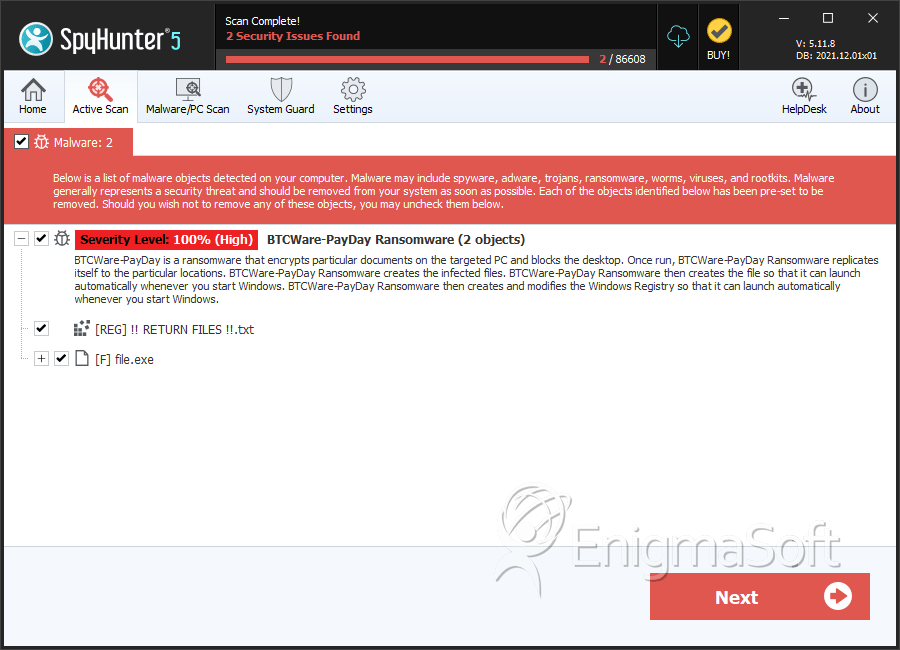
SpyHunter Detects & Remove BTCWare-PayDay Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 1c872d5b70ba7a49d1e743336e6fa18b | 0 |
| 2. | file.exe | b89668a8cee73f2d7083eb4c013e131c | 0 |
| 3. | file.exe | 43e5e55daf3ec8e032a7386c9a1710a6 | 0 |
| 4. | file.exe | 1887910c63217bfb9b811a03875bd668 | 0 |
| 5. | file.exe | e56cb01535e95b0160ea3ce103616356 | 0 |

