BlackShades Crypter Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 8 |
| First Seen: | May 26, 2016 |
| Last Seen: | August 14, 2021 |
| OS(es) Affected: | Windows |
The BlackShades Crypter Ransomware is a ransomware threat that is used to encrypt its victims' system files and demand the payment of a ransom. The BlackShades Crypter Ransomware takes the affected computer hostage, making the victim's files useless until they are forced to pay its elevated ransom amount. Attacks like the BlackShades Crypter Ransomware are quite common and have increased in popularity in the last year. There are several reasons why the BlackShades Crypter Ransomware and other encryption ransomware Trojans have become so common, including the rise of the RaaS (Ransomware as a Service) industry and the fact that these attacks offer a quick return on investment to con artists. The best way to deal with the BlackShades Crypter Ransomware and similar attacks is through preventive measures. Malware analysts recommend the use of a reliable anti-malware program and keeping backups of all files to prevent becoming a victim of these threats.
Table of Contents
How the BlackShades Crypter Ransomware may be Distributed
Most ransomware Trojans, including the BlackShades Crypter Ransomware, may be distributed through corrupted email attachments. Victims of the BlackShades Crypter Ransomware may receive an email message containing an attachment or embedded link, often seeming to come from a legitimate source such as a shipping company or a bank. When computer users click on the link or open the attachment, the BlackShades Crypter Ransomware is installed on their computers. There are other ways in which the BlackShades Crypter Ransomware and similar threats can be distributed. Threats like the BlackShades Crypter Ransomware may be found on file sharing networks, included inside popular torrent files, or on attack websites that exploit vulnerabilities in Java or other such platforms. Avoiding risky online locations, such as file sharing websites, and never opening unsolicited email messages are some of the best preventive measures to avoid the BlackShades Crypter Ransomware and similar attacks.
The BlackShades Crypter Ransomware can Encrypt Numerous Files
After the BlackShades Crypter Ransomware is installed on the victim's computer, the BlackShades Crypter Ransomware scans all drives for files with extensions that match its configuration settings. When the BlackShades Crypter Ransomware finds one of these files, it encrypts it using an advanced encryption algorithm. The following are the types of files that threats like the BlackShades Crypter Ransomware typically target in their attacks:
.sql, .mp4, .7z, .rar, .m4a, .wma, .avi, .wmv, .csv, .d3dbsp, .zip, .sie, .sum, .ibank, .t13, .t12, .qdf, .gdb, .tax, .pkpass, .bc6, .bc7, .bkp, .qic, .bkf, .sidn, .sidd, .mddata, .itl, .itdb, .icxs, .hvpl, .hplg, .hkdb, .mdbackup, .syncdb, .gho, .cas, .svg, .map, .wmo, .itm, .sb, .fos, .mov, .vdf, .ztmp, .sis, .sid, .ncf, .menu, .layout, .dmp, .blob, .esm, .vcf, .vtf, .dazip, .fpk, .mlx, .kf, .iwd, .vpk, .tor, .psk, .rim, .w3x, .fsh, .ntl, .arch00, .lvl, .snx, .cfr, .ff, .vpp_pc, .lrf, .m2, .mcmeta, .vfs0, .mpqge, .kdb, .db0, .dba, .rofl, .hkx, .bar, .upk, .das, .iwi, .litemod, .asset, .forge, .ltx, .bsa, .apk, .re4, .sav, .lbf, .slm, .bik, .epk, .rgss3a, .pak, .big, wallet, .wotreplay, .xxx, .desc, .py, .m3u, .flv, .js, .css, .rb, .png, .jpeg, .txt, .p7c, .p7b, .p12, .pfx, .pem, .crt, .cer, .der, .x3f, .srw, .pef, .ptx, .r3d, .rw2, .rwl, .raw, .raf, .orf, .nrw, .mrwref, .mef, .erf, .kdc, .dcr, .cr2, .crw, .bay, .sr2, .srf, .arw, .3fr, .dng, .jpe, .jpg, .cdr, .indd, .ai, .eps, .pdf, .pdd, .psd, .dbf, .mdf, .wb2, .rtf, .wpd, .dxg, .xf, .dwg, .pst, .accdb, .mdb, .pptm, .pptx, .ppt, .xlk, .xlsb, .xlsm, .xlsx, .xls, .wps, .docm, .docx, .doc, .odb, .odc, .odm, .odp, .ods, .odt.
Whenever the BlackShades Crypter Ransomware encrypts a file, it drops a text or HTML file in that directory. This file contains the BlackShades Crypter Ransomware's ransom note, which instructs the victim on how to pay the ransom to recover the infected files. Currently, it may not be possible to decrypt the files that have been encrypted by the BlackShades Crypter Ransomware. Because of this, the best measure in dealing with the BlackShades Crypter Ransomware is to restore the encrypted files from a backup location. Apart from encrypting the victim's files, the BlackShades Crypter Ransomware also deletes Shadow Volume copies of encrypted files and System Restore points, preventing victims of the BlackShades Crypter Ransomware from recovering using these alternate methods.
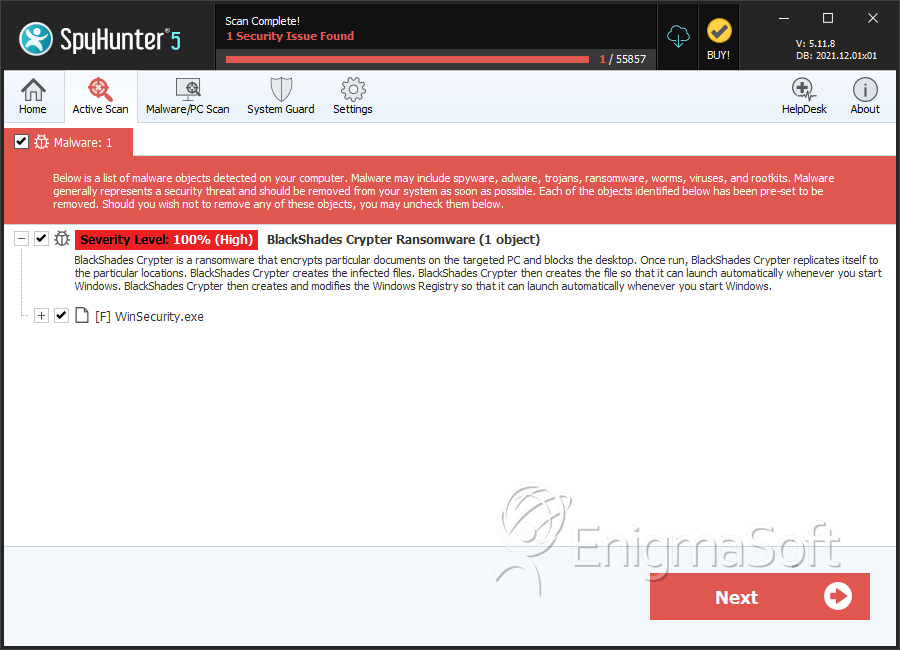
SpyHunter Detects & Remove BlackShades Crypter Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | WinSecurity.exe | 45beca45fc84cfea06cfc50490a222ba | 7 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.