BlackMist Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 5 |
| First Seen: | September 29, 2017 |
| Last Seen: | August 17, 2022 |
| OS(es) Affected: | Windows |
The BlackMist Ransomware is an encryption ransomware Trojan that was first observed by PC security researchers on September 26, 2017. It is clear that the BlackMist Ransomware is still under development since various aspects of this threat are unfinished clearly, and it does not seem to operate successfully. The BlackMist Ransomware can be identified easily because it adds the file extension '.blackmist' to the files it encrypts and runs as 'BlackMist.exe' on victims' computers. The BlackMist Ransomware, like many other encryption ransomware Trojans, uses the AES 256 encryption to make the victims' files inaccessible, essentially taking them hostage. The BlackMist Ransomware then displays a ransom demand, asking the victim to pay a lot of money to be provided with the decryption key necessary to restore the affected files. The BlackMist Ransomware's ransom note is displayed on a pop-up window that is titled 'BlackMist.'
Table of Contents
The Black Mist that cannot Reach Your Files Yet
The BlackMist Ransomware is designed to infect computers running the Windows operating system. The BlackMist Ransomware seems to be based on numerous other encryption ransomware Trojans and may have been modified from an open source ransomware engine. The BlackMist Ransomware does not run a successful attack, and it is possible that the BlackMist Ransomware was developed by an amateur or unsophisticated group. This is because, in many cases, the BlackMist Ransomware will crash as soon as it launches and fails to carry out its intended attack of encrypting the victim's files.
How a BlackMist Ransomware Attack is Supposed to Work
Although the BlackMist Ransomware crashes and does not carry out an effective ransomware attack in most cases, the BlackMist Ransomware will attempt to encrypt files on the victim's computer. Most ransomware Trojans like the BlackMist Ransomware target the user-generated files, such as the ones with the following file extensions:
.3gp, .7z, .apk, .avi, .bmp, .cdr, .cer, .chm, .conf, .css, .csv, .dat, .db, .dbf, .djvu, .dbx, .docm, ,doc, .epub, .docx .fb2, .flv, .gif, .gz, .iso .ibooks, .jpeg, .jpg, .key, .mdb .md2, .mdf, .mht, .mobi .mhtm, .mkv, .mov, .mp3, .mp4, .mpg, .mpeg, .pict, .pdf, .pps, .pkg, .png, .ppt .pptx, .ppsx, .psd, .rar, .rtf, .scr, .swf, .sav, .tiff, .tif, .tbl, .torrent, .txt, .vsd, .wmv, .xls, .xlsx, .xps, .xml, .ckp, .zip, .java, .py, .asm, .c, .cpp, .cs, .js, .php, .dacpac, .rbw, .rb, .mrg, .dcx, .db3, .sql, .sqlite3, .sqlite, .sqlitedb, .psd, .psp, .pdb, .dxf, .dwg, .drw, .casb, .ccp, .cal, .cmx, .cr2.
The BlackMist Ransomware will demand a ransom payment from the victim after encrypting the victim's files. The ransom demand that is displayed after a BlackMist Ransomware infection reads:
'BlackMist
[Info|TAB] [Dashboard|TAB]
The Black Mist has consumed your computer, and all files contained within it. Each file has been encrypted.
To restore your computer, you must moke a Payment of 100$ Bitcoin to the address specified. You will have 48 Hours to do so. After 24 hours, each following hour will execute the deletion of a portion of your files. After
the full 48 hours, all files will have been deleted, along with your operating system.
Attemping to close this application or shutdown you computer will result in full deletion of your files.
Time left: [48H COUNTDOWN TIMER]'
The people responsible for the BlackMist Ransomware demand a payment of 100 USD in BitCoins. This is a much lower amount than many other encryption ransomware Trojans. However, due to the poor implementation of the BlackMist Ransomware attack, it is very unlikely that the people responsible for the BlackMist Ransomware attack are capable of helping their victim's restore their files after a BlackMist Ransomware infection (in the cases where the BlackMist Ransomware was successful in carrying out the BlackMist Ransomware infection without crashing). As with other encryption ransomware Trojans, it is necessary to take deterrent precautions. The best effective preventive measure computer users can take against the BlackMist Ransomware is to use a dedicated security program and have file backups of their files.
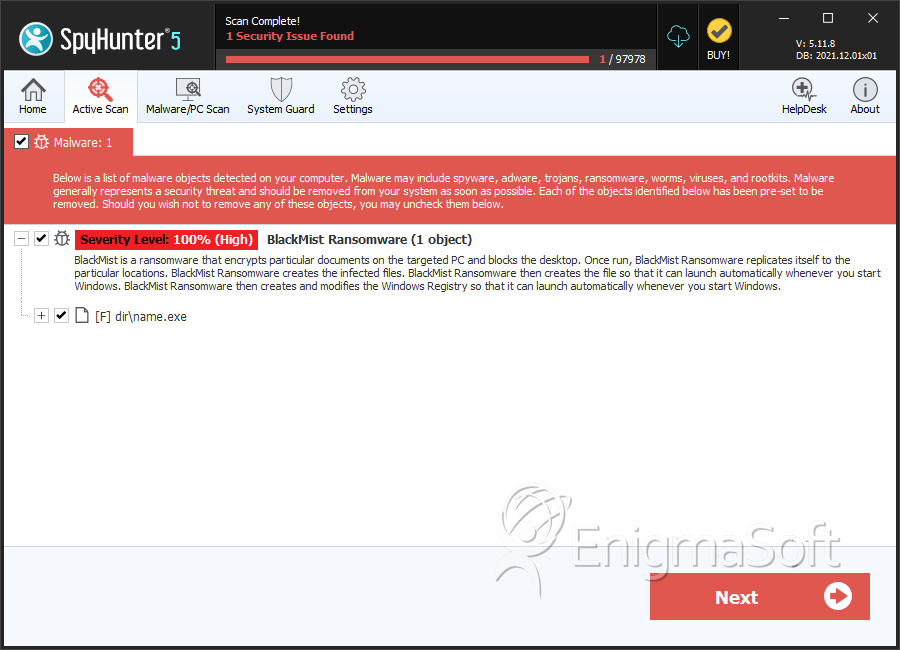
SpyHunter Detects & Remove BlackMist Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | name.exe | 0bd3c20690a758eab3830a41e10a6578 | 2 |

