Bkransomware Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 6 |
| First Seen: | May 16, 2018 |
| Last Seen: | July 18, 2018 |
| OS(es) Affected: | Windows |
The Bkransomware Ransomware is an encryption ransomware Trojan, used to force computer users to pay large ransoms by taking their files hostage. The Bkransomware Ransomware makes the victim's files inaccessible and seems to target computer users located in Vietnam, with ransom notes written in Vietnamese and payment methods tailored to this specific part of the world. However, the Bkransomware Ransomware can't be prevented from spreading to other parts of the world.
Table of Contents
How the Bkransomware Ransomware Generates Gain to Its Developers
The most common way of delivering the Bkransomware Ransomware to its victims is through the use of spam email messages. The Bkransomware Ransomware will often be delivered as a spam email attachment, which will present itself as a Microsoft Word file with embedded macro scripts that download and install the Bkransomware Ransomware onto the victim's computer. Threats like the Bkransomware Ransomware also may be delivered through other means, such as by taking advantage of poor password protection, poorly guarded RDP (Remote Desktop Protocol) connections or other tactics. Once the Bkransomware Ransomware has been installed onto the victim's computer, the Bkransomware Ransomware will use the SHA encryption to make the victim's files inaccessible. The Bkransomware Ransomware targets a wide variety of files, which may include the following:
.3dm, .3g2, .3gp, .7zip, .aaf, .accdb, .aep, .aepx, .aet, .ai, .aif, .as, .as3, .asf, .asp, .asx, .avi, .bmp, .c, .class, .cpp, .cs, .csv, .dat, .db, .dbf, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .dwg, .dxf, .efx, .eps, .fla, .flv, .gif, .h, .idml, .iff, .indb, .indd, .indl, .indt, .inx, .jar, .java, .jpeg, .jpg, .js, .m3u, .m3u8, .m4u, .max, .mdb, .mid, .mkv, .mov, .mp3, .mp4, .mpa, .mpeg, .mpg, .msg, .pdb, .pdf, .php, .plb, .pmd, .png, .pot, .potm, .potx, .ppam, .ppj, .pps, .ppsm, .ppsx, .ppt, .pptm, .pptx, .prel, .prproj, .ps, .psd, .py, .ra, .rar, .raw, .rb, .rtf, .sdf, .sdf, .ses, .sldm, .sldx, .sql, .svg, .swf, .tif, .txt, .vcf, .vob, .wav, .wma, .wmv, .wpd, .wps, .xla, .xlam, .xll, .xlm, .xls, .xlsb, .xlsm, .xlsx, .xlt, .xltm, .xltx, .xlw, .xml, .xqx, .xqx, .zip.
The Bkransomware Ransomware marks the files encrypted by the attack adding the file extension '.hainch' to each affected file's name, making it very easy to tell which files have been compromised. The Bkransomware Ransomware also will delete the Windows backups, such as the Shadow Volume Copies of the affected files and the System Restore point, apart from encrypting the victim's files.
The Bkransomware Ransomware’s Unusual Ransom Payment Method
Most encryption ransomware Trojans demand payment using crypto-currency, such as Bitcoin. The Bkransomware Ransomware, instead, demands payment and asks for 50,000 Viette, a mobile phone credit, to be deposited to a specific mobile phone number. The ransom note is very direct, and simply reads:
'send 50k to 0963210438 to restore your data
Press any key to continue...'
However, infected PC users should refrain from paying the ransom, since there is no real way for the con artists help the victims restore their files. Furthermore, paying these ransoms allows these people to continue financing their threats, creating new ransomware Trojans and distributing them to more victims. Instead of paying the Bkransomware Ransomware ransom, they should take precautions against the Bkransomware Ransomware and other ransomware Trojans.
Keeping Your Data Protected from Threats Like the Bkransomware Ransomware
The best protection against threats like the Bkransomware Ransomware is to have file backups on external devices. The combination of file backups with a trustable security program that is fully up-to-date can help computer users restore their files easily after an attack, removing any need to contact the people responsible for the attack and negotiate the return of the affected files. Ransomware Trojans like the Bkransomware Ransomware are becoming more common increasingly, and it is more important than ever to take steps to ensure that your data and computer are well protected from the Bkransomware Ransomware and other threats like this one.
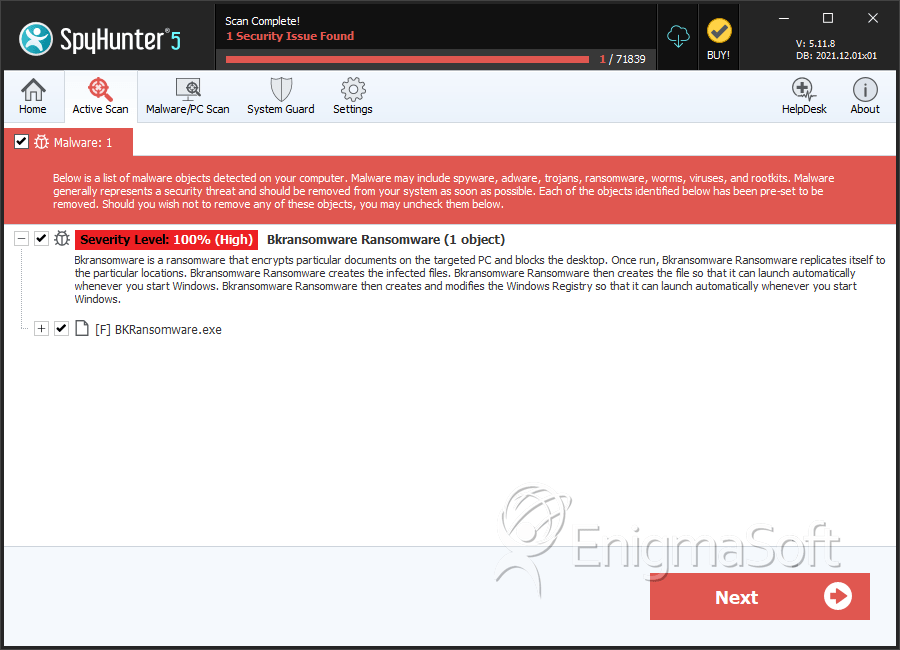
SpyHunter Detects & Remove Bkransomware Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | BKRansomware.exe | 892da86e60236c5aaf26e5025af02513 | 1 |

