BadEncript Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 7 |
| First Seen: | December 27, 2016 |
| Last Seen: | August 17, 2022 |
| OS(es) Affected: | Windows |
The BadEncript Ransomware is an encryption ransomware Trojan that is used to force computer users to pay large amounts of money. The BadEncript Ransomware encrypts its victims' files to demand ransom in exchange for the decryption key. The poor implementation of the encryption routine has resulted in a threat that is probably still in development, and there is no way of decrypting the affected files. Because of this, computer users should never agree to pay the BadEncript Ransomware ransom.
Table of Contents
The Bad Consequences of a BadEncript Ransomware Infection
There are flaws in the BadEncript Ransomware's code that make it clear that this Trojan is still in development and remains unfinished. The BadEncript Ransomware's ransom note is also incomplete, meaning that victims cannot pay the ransom fee associated with the BadEncript Ransomware. The BadEncript Ransomware is just one of the countless ransomware Trojans released in 2016. These threats are developed both by amateurs and large unlawful organizations. In the case of the BadEncript Ransomware, it is clearly the first of these options. The BadEncript Ransomware does not store the decryption key anywhere, not in the victim's computer or on its Command and Control servers. Once the BadEncript Ransomware has been stopped, the decryption key, which is stored in memory, becomes impossible to extract. Because of this, any potential method to retrieve the decryption key of the BadEncript Ransomware infection would require computer users not to shut down or restart their computers. Fortunately for computer users, this is unlikely to happen. The BadEncript Ransomware does not seem to be distributed actively, and PC security researchers retrieved a sample of the BadEncript Ransomware on an online virus scanner, probably uploaded by its creators as a way to gauge whether the BadEncript Ransomware can evade anti-virus detection.
The BadEncript Ransomware will Cause Permanent Damage to the Victim’s Data
Although the BadEncript Ransomware has no way of retrieving the decryption key, its encryption routine is still carried out. The BadEncript Ransomware uses a strong encryption method to encrypt every file it finds that matches its criteria (typically a list of targeted file extensions). The files that are encrypted by the BadEncript Ransomware will have their extensions changed to '.bript,' making it simple to tell when a file has been affected by the BadEncript Ransomware attack. The BadEncript Ransomware delivers its ransom note in an HTML file named 'more.html,' which is dropped on the infected computer's desktop. The BadEncript Ransomware's ransom note seems to be incomplete, since it does not specify the amount of the ransom to be paid, nor does it give the victim details to contact the people responsible for the attack.
The BadEncript Ransomware Doesn’t Provide a Way to Contact Its Perpetrators
The Bitcoin wallet address that is included in the BadEncript Ransomware ransom note is empty, meaning that the victims of the BadEncript Ransomware attack have no way to carry out their payments. It is clear that even if the victims find a way to pay the people responsible for the BadEncript Ransomware infection, the con artists will have no way to restore the victim's files since the decryption key is not saved anywhere. Unfortunately, once the BadEncript Ransomware has encrypted a file, it becomes completely inaccessible. The BadEncript Ransomware targets media files, images, documents, databases, spreadsheets, and a wide variety of other files. The BadEncript Ransomware has the potential to become a ransomware threat, but in its current state, it poses no danger to computer users.
Dealing with the BadEncript Ransomware Infection
The best way to protect your files from threats like the BadEncript Ransomware is to have backups. PC security researchers strongly advise computer users to back up all files on the cloud or an external memory device. Backups make computer users invulnerable to these attacks since con artists can no longer ask for ransom if the victim can recover the files from the backup copy quickly.
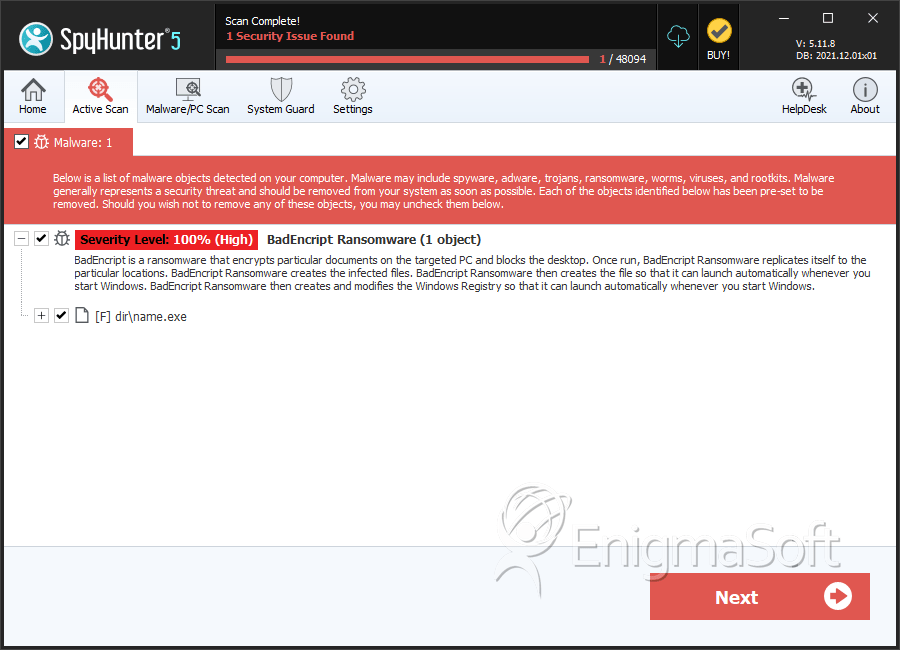
SpyHunter Detects & Remove BadEncript Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | name.exe | e7818e26919dc4f84c6ac683f78eba88 | 2 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.