'Alex.vlasov@aol.com' Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 69 |
| First Seen: | July 21, 2016 |
| Last Seen: | August 17, 2022 |
| OS(es) Affected: | Windows |
The 'alex.vlasov@aol.com' Ransomware is a ransomware Trojan that has been identified as a variant of Troldesh, also known as 'Shade'. The 'alex.vlasov@aol.com' Ransomware and its variants were created in Russia and are easily identified because they use the extensions .XTBL or YTBL to identify the files that have been encrypted during the 'alex.vlasov@aol.com' Ransomware attack. Some variants of the 'alex.vlasov@aol.com' Ransomware will also include the infected computer's unique identifier and the email address linked to the 'alex.vlasov@aol.com' Ransomware attack in the encrypted files' names.
The 'alex.vlasov@aol.com' Ransomware and Other Troldesh Variants
The ransom notes associated with the 'alex.vlasov@aol.com' Ransomware include the text files named README1.txt and 'How to decrypt your files.txt'. The 'alex.vlasov@aol.com' Ransomware will also replace the victim's Desktop Wallpaper image and drop image files with instructions to email the 'alex.vlasov@aol.com' address to receive instructions for payment. Variants of Troldesh such as the 'alex.vlasov@aol.com' Ransomware have been responsible for numerous attacks around the world. Unfortunately, it may not be possible to decrypt files that have been encrypted using the 'alex.vlasov@aol.com' Ransomware or other Troldesh variants currently.
Backups of your Files can Neutralize the 'alex.vlasov@aol.com' Ransomware Attack
It is simple to understand the 'alex.vlasov@aol.com' Ransomware attack; the 'alex.vlasov@aol.com' Ransomware will take the victim's files hostage by encrypting them using an advanced encryption algorithm. The victim is then forced to pay a large ransom in exchange for the decryption key. PC security analysts strongly advise computer users to avoid paying the 'alex.vlasov@aol.com' Ransomware ransom since this enables con artists to continue producing ransomware variants and carrying out these attacks. You also have no guarantee that the con artists responsible for the 'alex.vlasov@aol.com' Ransomware will honor their promise and return your files after you pay. It is equally likely that they will instead demand even more money, or simply outright ignore your requests. The best way to protect yourself from the 'alex.vlasov@aol.com' Ransomware attacks is to ensure that using a reliable backup method on an external memory device properly backs up all your files.
The 'alex.vlasov@aol.com' Ransomware Attack and How It Relates to Troldesh
The Troldesh ransomware variant has been studied extensively, and it turned out as being one of the major ransomware families active today. The 'alex.vlasov@aol.com' Ransomware and other Troldesh variants will rename the files with the format Base64[AES_encrypt-original file name] and then add the XTBL extension. In the case of the 'alex.vlasov@aol.com' Ransomware, the email address associated with this attack also is included in the changed file names. Unfortunately, the files encrypted by the 'alex.vlasov@aol.com' Ransomware are not decryptable yet, although PC security analysts are working on decryption tools to help computer users that have become victims of Troldesh variants constantly. There are decryptors available for some variants of Troldesh currently. Computer users are advised to attempt decryption using one of them if their files were not backed up properly.
Preventing an Infection with the 'alex.vlasov@aol.com' Ransomware
The 'alex.vlasov@aol.com' Ransomware may be installed with the help of a different threat. In most cases, the 'alex.vlasov@aol.com' Ransomware delivery method will exploit vulnerabilities in the target's computer. In many cases, the 'alex.vlasov@aol.com' Ransomware will be distributed using corrupted email attachments. Computer users are advised to exercise caution when dealing with these files. Once the 'alex.vlasov@aol.com' Ransomware is installed, it will search for files matching a list of file extensions in its configuration files and then use its encryption algorithm to encrypt them. This can be prevented by ensuring that a computer is protected properly with a reliable, fully updated anti-malware program capable of detecting and intercepting threats like the 'alex.vlasov@aol.com' Ransomware. PC security analysts also strongly advise computer users to have reliable back-ups of all important files or, ideally, a disk image of their hard drives. If your files are backed up properly on an external device, you will become invulnerable to these kinds of attacks, since con artists no longer have any leverage to demand a ransom when you can recover the encrypted files easily.
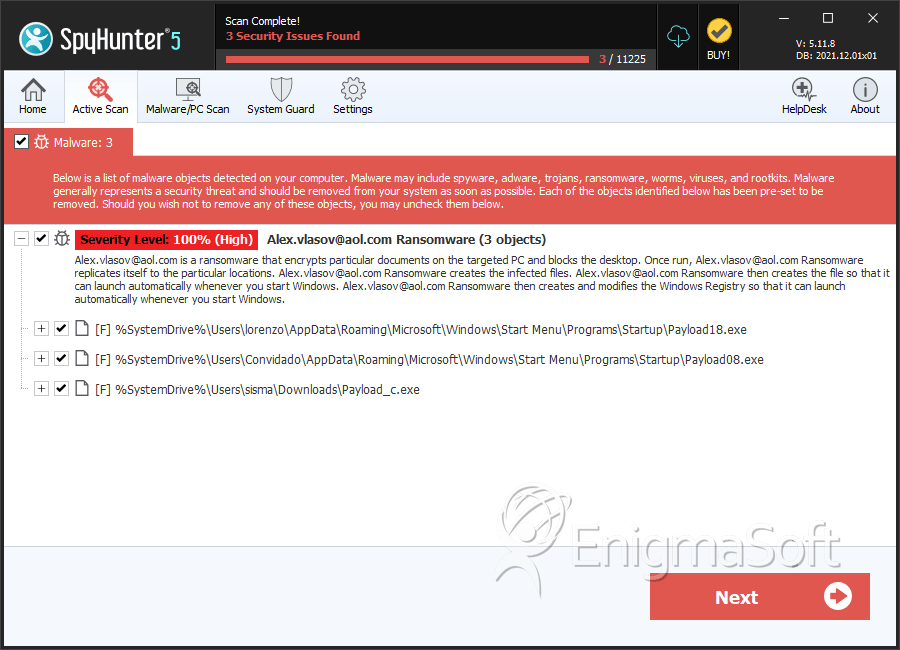
SpyHunter Detects & Remove 'Alex.vlasov@aol.com' Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | Payload18.exe | 55ce2d19629b55950d550feec3da04f6 | 30 |
| 2. | Payload08.exe | d371b702161c64a6dc29c8fe46dcb19c | 4 |
| 3. | Payload_c.exe | 03b502d2de91bc1e8dd8bc967074938b | 2 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.