Alcatraz Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 4 |
| First Seen: | November 1, 2016 |
| Last Seen: | June 1, 2018 |
| OS(es) Affected: | Windows |
The Alcatraz Ransomware is an encryption ransomware Trojan. The Alcatraz Ransomware is one of many recently developed ransomware Trojans that take advantage of corrupted macro scripts and are distributed through spam email messages. Encryption Trojans that take advantage of macros, such as the Alcatraz Ransomware, have gradually been favored by threat creators because of a variety of reasons. The two most common reasons for the popularity of these threats is that corrupted macro scripts generated from PDF or Microsoft Office documents may bypass anti-virus protections on infected computers. These files are also likelier to be opened by computer users than executable files or ZIP or RAR archives.
Table of Contents
How the Alcatraz Ransomware Attack Works
The Alcatraz Ransomware, like most ransomware Trojans, is designed to prevent computer users from accessing their files. Using an advanced encryption algorithm, the Alcatraz Ransomware will prevent access to the victim's files by encrypting them. The Alcatraz Ransomware will not limit its attack to the infected hard drive but also encrypt all removable drives connected to the infected computer, increasing the likelihood that the Alcatraz Ransomware will also encrypt the victim's backups. The Alcatraz Ransomware runs in the background, encrypting the victim's files and preventing Windows from displaying error notifications. This means that computer users may not realize that their files have been rendered useless until after the Alcatraz Ransomware carries out its attack. The Alcatraz Ransomware targets the following file types in its attack:
.3GP, .7Z, .APK, .AVI, .BMP, .CDR, .CER, .CHM, CONF, .CSS, .CSV, .DAT, .DB, .DBF, .DJVU, .DBX, .DOCM, ,DOC, .EPUB, .DOCX .FB2, .FLV, .GIF, .GZ, .ISO .IBOOKS, .JPEG, .JPG, .MKV, .MOV, .MP3, .MP4, .MPG .MPEG, .PICT, .PDF, .PPS, .PKG, .PNG, .PPT .PPTX, .PPSX, .PSD, .RAR, .RTF, .SCR, .SWF, .SAV, .TIFF, .TIF, .TBL, .TORRENT, .TXT, .VSD,.WMV, .XLS, .XLSX, .XPS, .XML, ZIP, .JAVA, .C, .CPP, .CS, .JS, .PHP, .DACPAC, .RBW, .RB, .MRG, .DCX, .DB3, .SQL, .SQLITE3, .SQLITE, .SQLITEDB, .PSD, .PSP, .PDB, .DXF, .DWG, .DRW, .CASB, .CCP, .CAL, .CMX, .CR2.
The Alcatraz Ransomware’s Ransom Note
The Alcatraz Ransomware encryption process can take a few minutes, depending on how much data is involved in the Alcatraz Ransomware attack. Files that have been encrypted by the Alcatraz Ransomware will have the file extension '.Alcatraz' added to their names. The Alcatraz Ransomware delivers its ransom note in the form of an HTML file dropped on the victim's computer. The following is the data contained in the Alcatraz Ransomware's ransom file, named 'ransomed.html':
'ALL YOUR DATA ARE ENCRYPTED.
Pay 0.5 BTC at [34 random characters]
Q&A
Q : What's happens?
A : You have been infected by a Alcatraz Locker
Q : What I have to do now ?
A : The only method to get back your document is to pay.'
Dealing with the Alcatraz Ransomware and Preventing Its Attacks
Unfortunately, the files that have been encrypted by the Alcatraz Ransomware are not recoverable without the decryption key. Because of this, as with most encryption ransomware Trojans, taking preventive measures is the most important aspect of eradicating these threats. Computer users are urged to backup all of their files regularly on an external device that is not connected physically or through a network to the main computer (to prevent the risk of threats like the Alcatraz Ransomware also encrypting the backups). PC security researchers strongly advise computer users to avoid contacting the people responsible for the Alcatraz Ransomware. There is little chance that they will keep their promise to provide the means to decrypt the compromised files after payment is carried out. It is more likely that the con artists will demand additional payments or simply ignore the victim. Even if they do help the victims recover their files, paying what is asked allows con artists to continue developing and releasing threats like the Alcatraz Ransomware, which will put more computer users at risk.
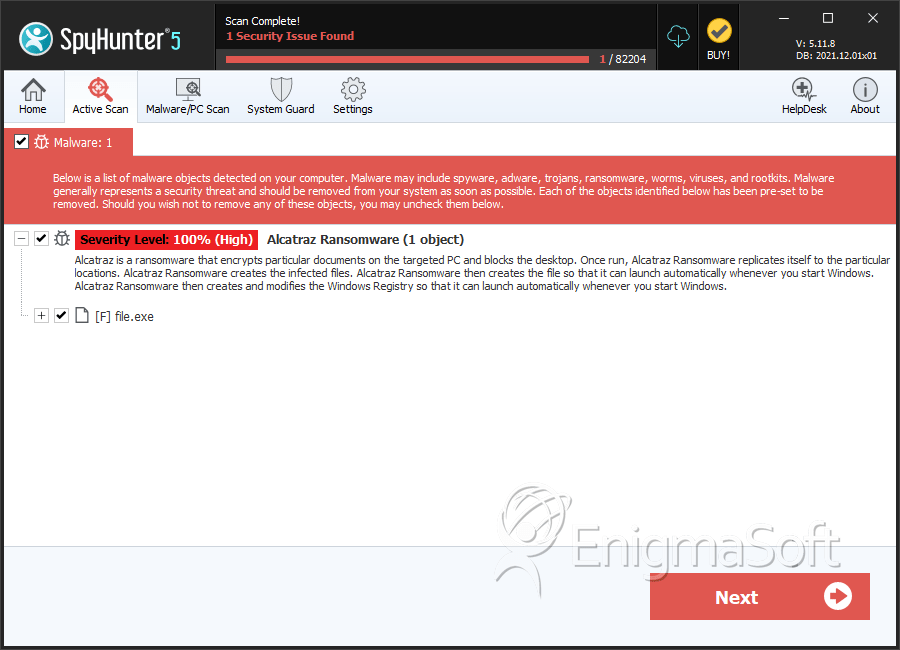
SpyHunter Detects & Remove Alcatraz Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 35d93ccc99cf73c9c46349718aeae588 | 0 |
| 2. | file.exe | cb44ccf09d8dc084a1377fe7b981084c | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.