Adware.AdAgent
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
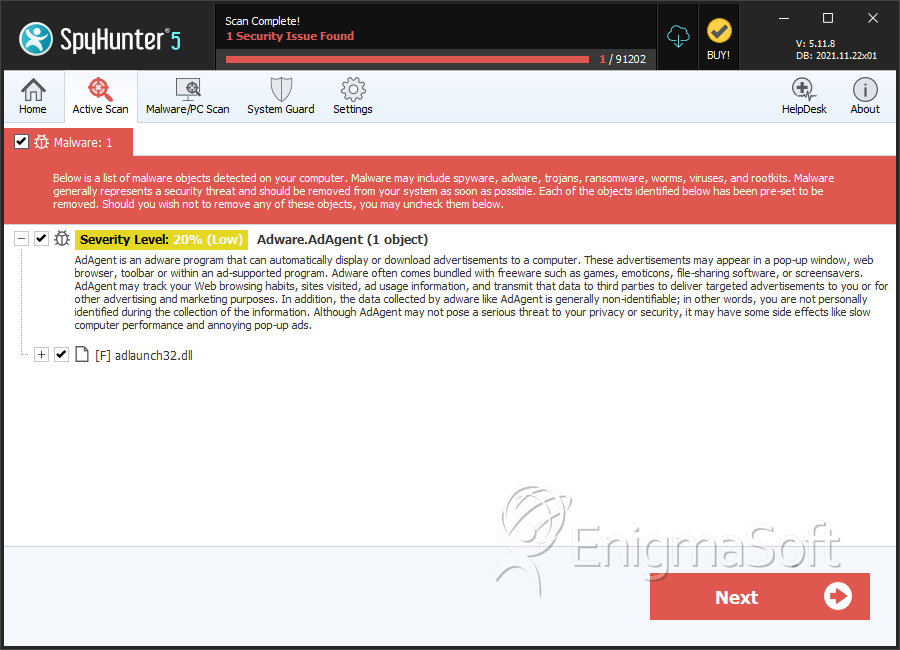
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 9,456 |
| Threat Level: | 20 % (Normal) |
| Infected Computers: | 958 |
| First Seen: | December 1, 2009 |
| Last Seen: | January 28, 2026 |
| OS(es) Affected: | Windows |
Adware.AdAgent is very dangerous adware program that will only cause you many problems as well as invade your privacy. Adware.AdAgent will get access to your computer, without your knowledge or permission. Adware.AdAgent will continuously bombard your computer with numerous advertisements and pop-up warnings. Adware.AdAgent is also able to control your web browsing activities and occupy some of your private details. Adware.AdAgent may completely invade your privacy and be able to take over all your confidential data. Adware.AdAgent may cause your entire PC system to malfunction and become increasingly unstable. Adware.AdAgent is also able to make your computer system to freeze or shut down sporadically. Remove Adware.AdAgent as soon as you detect it on your PC system.
Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Antivirus Vendor | Detection |
|---|---|
| NOD32 | Win32/Nuwvult.A |
| McAfee-GW-Edition | Ad-Spyware.AdAgent.R |
| K7AntiVirus | not-a-virus:AdWare.Win32.AdAgent.r |
| Fortinet | Adware/AdAgent |
| F-Secure | AdWare.Win32.AdAgent.r |
| eTrust-Vet | Win32/ASuspect.GIMGE |
| CAT-QuickHeal | AdWare.AdAgent.r (Not a Virus) |
| BitDefender | Adware.Generic.61588 |
| Antiy-AVL | AdWare/Win32.AdAgent.gen |
| AntiVir | ADSPY/AdAgent.R |
| AhnLab-V3 | Win-Trojan/Adagent.83992 |
| Sophos | Mal/Generic-A |
| Panda | Trj/CI.A |
| McAfee-GW-Edition | Heuristic.LooksLike.Win32.H |
| McAfee | potentially unwanted program Generic PUP |
SpyHunter Detects & Remove Adware.AdAgent
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | %programfiles\Adware.Adware.AdAgent \defhook.dll | ||
| 2. | %programfiles\Adware.Adware.AdAgent \defext.dll | ||
| 3. | %programfiles\Adware.Adware.AdAgent \buy.ico | ||
| 4. | %desktop%\Adware.Adware.AdAgent support.lnk | ||
| 5. | %commonprograms%\Adware.Adware.AdAgent \activate.lnk | ||
| 6. | %programfiles\Adware.Adware.AdAgent \activate.ico | ||
| 7. | %appdata%\microsoft\internet explorer\quick launch\Adware.Adware.AdAgent .lnk | ||
| 8. | %commonprograms%\Adware.Adware.AdAgent \about.lnk | ||
| 9. | %programfiles\Adware.Adware.AdAgent \about.ico | ||
| 10. | %programfiles\Adware.Adware.AdAgent \def.db | ||
| 11. | %desktop%\Adware.Adware.AdAgent .lnk | ||
| 12. | adlaunch32.dll | ca8df29bbac6f0c1cf435bb82090c7c6 | |
| 13. | adlaunch32.dll | ae8d528538eb42d63ced6fbb67e5fb1b | 0 |
Registry Details
Analysis Report
General information
| Family Name: | Adware.AdAgent |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
c7d811cbb112331f40e94f0192135bc3
SHA1:
697799b1747b036b4fd747d553a1f42d73b8db0a
SHA256:
8310A1A84DB6E716A278E7FA3BD32DBBE437F54F92D049FCC1E2D8E8CA9E71C1
File Size:
63.72 KB, 63715 bytes
|
|
MD5:
d5d14072391f45e92e903ec6737ee288
SHA1:
edd5468d9d396bb19c032c408189539fe5b6a8c0
SHA256:
EE99E2563CA4EFB81939F306E2D575B3F4EC8111A3753DD281A0A189539B3060
File Size:
63.71 KB, 63714 bytes
|
|
MD5:
05cd87e73552774838cb56eaa3503b54
SHA1:
21823d296dd0c181eed9cb9a8c214c68dd8a0305
SHA256:
154BA45EA37DCB314628C021E6D963587D4C606DDC8C5EACD766C6AA8918B1BF
File Size:
63.70 KB, 63701 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
Show More
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Original Filename |
|
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Anti Debug |
|
| User Data Access |
|
