5H311 1NJ3C706 Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 4 |
| First Seen: | October 18, 2018 |
| Last Seen: | March 30, 2019 |
| OS(es) Affected: | Windows |
The 5H311 1NJ3C706 Ransomware is an encryption ransomware Trojan first observed on September 7, 2018. It seems that the 5H311 1NJ3C706 Ransomware is still under development. The 5H311 1NJ3C706 Ransomware, like most encryption ransomware Trojans, is designed to encrypt the victims' files to extort the victims by demanding a ransom payment in exchange for restoring access to the targeted data.
Table of Contents
Some Details about the 5H311 1NJ3C706 Ransomware Attack
PC security researchers reported that the 5H311 1NJ3C706 Ransomware was not capable of encrypting data after testing the 5H311 1NJ3C706 Ransomware. However, studying the 5H311 1NJ3C706 Ransomware's code reveals that the 5H311 1NJ3C706 Ransomware is designed to function as an encryption ransomware Trojan rather than a screen locker. When the 5H311 1NJ3C706 Ransomware works correctly, it targets the user-generated files and encrypts them by using the AES encryption, then adding the string '.5H11 1NJ3C706' to the encrypted files as a new extension. These attacks target the user-generated files, which may include files with the following file extensions:
.jpg, .jpeg, .raw, .tif, .gif, .png, .bmp, .3dm, .max, .accdb, .db, .dbf, .mdb, .pdb, .sql, .dwg, .dxf, .cpp, .cs, .h, .php, .asp, .rb, .java, .jar, .class, .py, .js, .aaf, .aep, .aepx, .plb, .prel, .prproj, .aet, .ppj, .psd, .indd, .indl, .indt, .indb, .inx, .idml, .pmd, .xqx, .xqx, .ai, .eps, .ps, .svg, .swf, .fla, .as3, .as, .txt, .doc, .dot, .docx, .docm, .dotx, .dotm, .docb, .rtf, .wpd, .wps, .msg, .pdf, .xls, .xlt, .xlm, .xlsx, .xlsm, .xltx, .xltm, .xlsb, .xla, .xlam, .xll, .xlw, .ppt, .pot, .pps, .pptx, .pptm, .potx, .potm, .ppam, .ppsx, .ppsm, .sldx, .sldm, .wav, .mp3, .aif, .iff, .m3u, .m4u, .mid, .mpa, .wma, .ra, .avi, .mov, .mp4, .3gp, .mpeg, .3g2, .asf, .asx, .flv, .mpg, .wmv, .vob, .m3u8, .dat, .csv, .efx, .sdf, .vcf, .xml, .ses, .qbw, .qbb, .qbm, .qbi, .qbr , .cnt, .des, .v30, .qbo, .ini, .lgb, .qwc, .qbp, .aif, .qba, .tlg, .qbx, .qby , .1pa, .qpd, .txt, .set, .iif, .nd, .rtp, .tlg, .wav, .qsm, .qss, .qst, .fx0, .fx1, .mx0, .fpx, .fxr, .fim, .ptb, .ai, .pfb, .cgn, .vsd, .cdr, .cmx, .cpt, .csl, .cur, .des, .dsf, .ds4, .drw, .eps, .ps, .prn, .gif, .pcd, .pct, .pcx, .plt, .rif, .svg, .swf, .tga, .tiff, .psp, .ttf, .wpd, .wpg, .wi, .raw, .wmf, .txt, .cal, .cpx, .shw, .clk, .cdx, .cdt, .fpx, .fmv, .img, .gem, .xcf, .pic, .mac, .met, .pp4, .pp5, .ppf, .nap, .pat, .ps, .prn, .sct, .vsd, .wk3, .wk4, .xpm, .zip, .rar.
The 5H311 1NJ3C706 Ransomware will deliver a ransom note in the form of a program window. The 5H311 1NJ3C706 Ransomware ransom note contains the following message:
'Ransomware 5H311 1NJ3C706
You Has Been Hacked
+What happened to my file
All your file has been locked. You must pay money to have a key.
If you don;t pay , after 24h your file will be delete.
+How to buy
You must send 300 Bitcoin to my address
+How to have Bitcoin
You can buy Bitcoin on website or other website.
hxxps://coinsutra[.]com/go/Coinbase/
hxxps://coinsutra[.]com/go/Bitstamp/
+Where address to send
To see my wallet address, click Button "Pay Money".
After we receive Bitcoin from you. We will send key to your email.
Time [24h countdown timer]
Created By Hacker Thn
Give for fan
5H311 1NJ3C706'
Dealing with the 5H311 1NJ3C706 Ransomware
If the 5H311 1NJ3C706 Ransomware has infected your computer, it may be necessary to disable the 5H311 1NJ3C706 Ransomware's ransom note. Bypassing the 5H311 1NJ3C706 Ransomware screen locker component can be done by using the password '666HackerThn.' However, if the 5H311 1NJ3C706 Ransomware manages to encrypt your files, then it will be more difficult to recover them. The encryption methods used by these threats are usually very strong and cannot be reversed without the decryption key. Because of this, the best protection against the 5H311 1NJ3C706 Ransomware, as with most encryption ransomware Trojans, is to have file backups, which can enable quick recovery of any compromised data after a 5H311 1NJ3C706 Ransomware infection. This, coupled with a trustable security program, can help computer users recover from most attacks like this one.
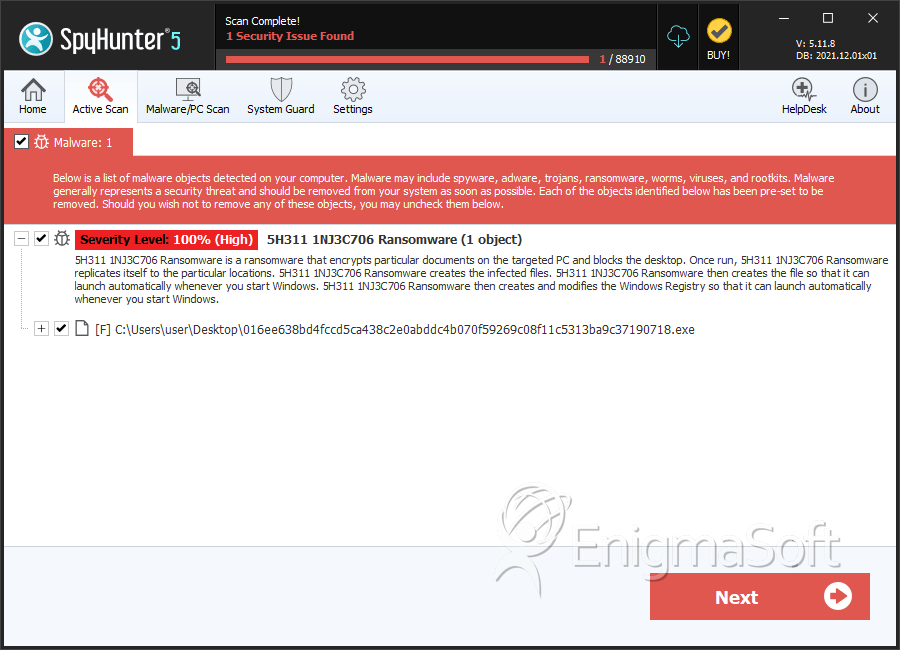
SpyHunter Detects & Remove 5H311 1NJ3C706 Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | 016ee638bd4fccd5ca438c2e0abddc4b070f59269c08f11c5313ba9c37190718.exe | 9ca8eed140b1f02fa97967afbdc763c5 | 1 |

