Troj/ExpJS-II
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 6 |
| First Seen: | April 22, 2013 |
| Last Seen: | January 10, 2022 |
| OS(es) Affected: | Windows |
Troj/ExpJS-II is part of a malicious Java-based attack used to infect computers without the computer user's knowledge. Troj/ExpJS-II has been used in several attacks that take advantage of breaking news stories in order to convince computer users to visit websites containing videos or news stories. These websites are actually designed to redirect computer users to an attack website without their knowledge. In the case of Troj/ExpJS-II, this malicious infection was in an attack that attempted to convince computer users to view a video containing news about the fertilizer plant explosion in Waco, Texas. This same scam is concurrently being carried out with malicious messages claiming to contain information about the Boston Marathon bombing.
Table of Contents
The Social Engineering Scam Associated with Troj/ExpJS-II
Computer users initially receive a spam email message with a subject line claiming that the message contains news relating to the breaking news story (in the case of Troj/ExpJS-II that news story is the fertilizer plant explosion that occurred in April of 2013). If the computer user opens these email messages, he will observe an embedded link in the email message which leads the computer user to a website that seems to contain embedded YouTube videos. These videos are there merely to distract the computer user while the real attack occurs in the background. These kinds of social engineering attacks are commonly detected after an important breaking news story. The nature of the news story does not seem to matter much. Troj/ExpJS-II attacks are associated with news ranging from the new launch of an iPhone and celebrity deaths or important sports events, the ballot of a new pope to a school shooting. Unfortunately, the criminals responsible for Troj/ExpJS-II attacks care little about the sensibilities of exploiting news involving the deaths of innocents to distribute malware.
The website containing the embedded videos also contains a small iFrame which loads content from an attack website. The attack website uses an exploit kit known as RedKit which will try to take advantage of various software vulnerabilities in order to install Trojans on the victim's computer. RedKit uses various tactics to infect a computer with its main exploits associated with the Java Runtime Platform and Adobe Reader. Troj/ExpJS-II is a detection used to refer to the malicious iFrame used to load this dangerous content.
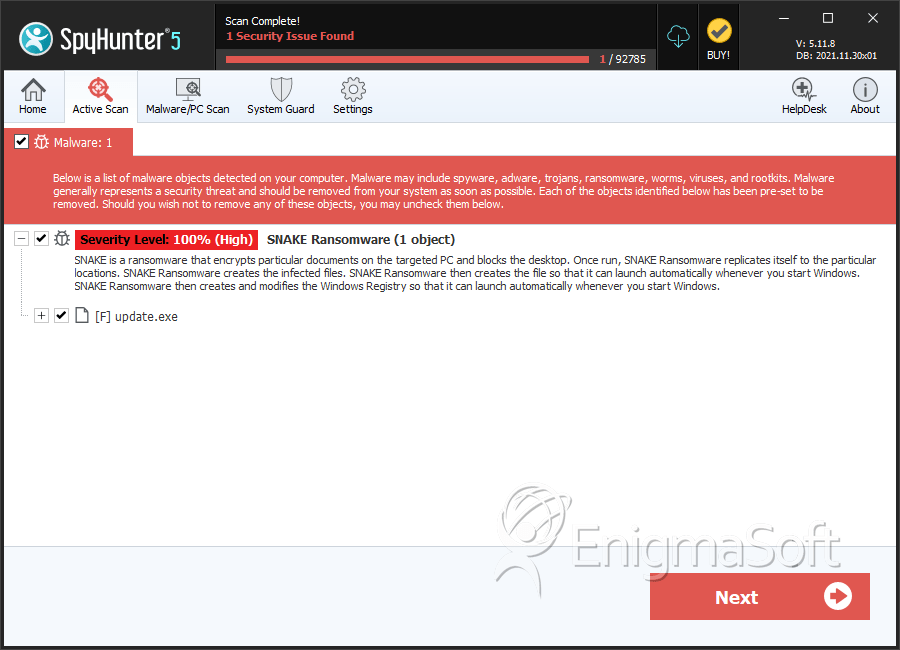
SpyHunter Detects & Remove Troj/ExpJS-II
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | update.exe | 3d1cc4ef33bad0e39c757fce317ef82a | 3 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.